Saint_I_Aint @S41NTsec
FT Purple-Teamer @ A Place You've Heard Of. | Early Career | Windows Focus | 🏳️🌈 - I share Atk+Def resources, and adore obscure/intricate attack chains. Texas, USA Joined October 2018-
Tweets3K
-
Followers55
-
Following257
-
Likes3K
One of good friends @cyb3rp_nk put together this fantastic research paper about tactical containment of Active Directory in the event of domain dominance by an adversary. If you work with AD, in IR or anything adjacent, it is well worth your time to read - sans.edu/cyber-research…
''APT28: From Initial Damage to Domain Controller Threats in an Hour (CERT-UA#8399)'' #infosec #pentest #redteam #blueteam medium.com/cyberscribers-…
Bye bye to my admin->kernel priv8 0day 👋 Was sitting on it due to an NDA and i thought it was a quite unique bug, turns out it wasn't. TTP burned 🔥 I might have a blogpost in the future in which i describe how i (differently) exploited it, let's see if time permits...
Bye bye to my admin->kernel priv8 0day 👋 Was sitting on it due to an NDA and i thought it was a quite unique bug, turns out it wasn't. TTP burned 🔥 I might have a blogpost in the future in which i describe how i (differently) exploited it, let's see if time permits...
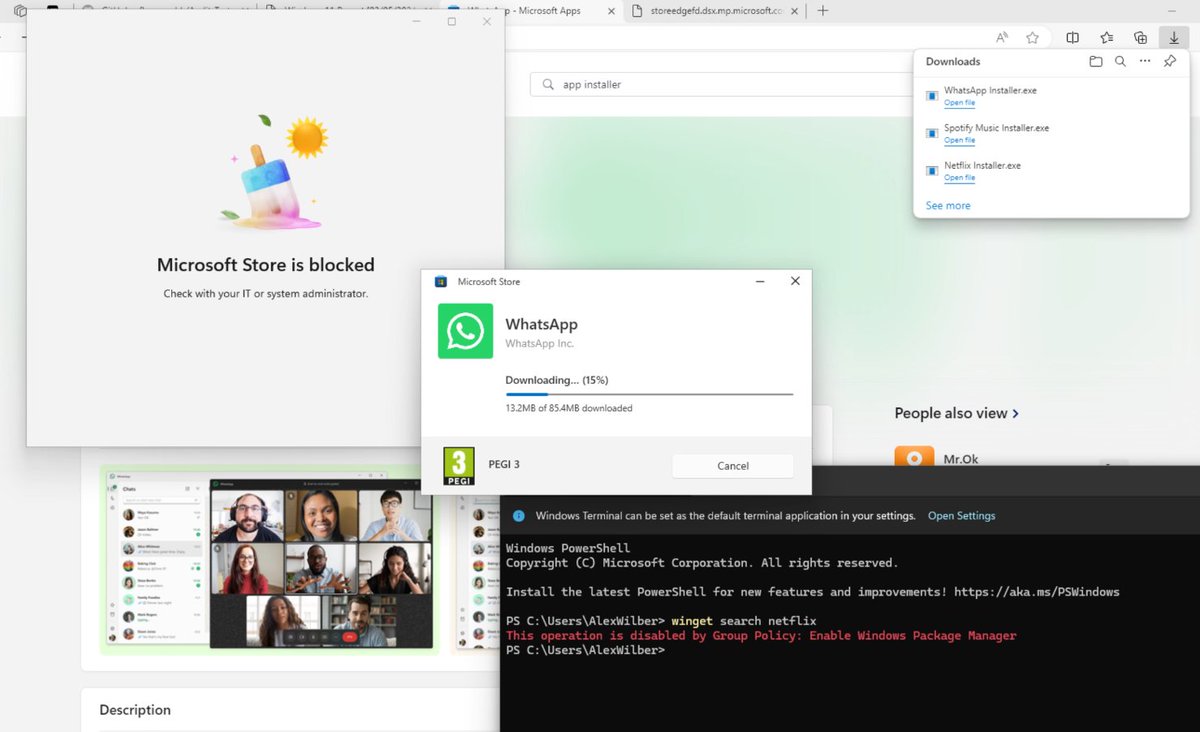
Microsoft please. What is this? Can we please not allow bypasses that are so easy, that a normal user can do it?
Microsoft please. What is this? Can we please not allow bypasses that are so easy, that a normal user can do it?
Reminder: It's never been safe to run a program out of a directory that contains other untrusted files. insights.sei.cmu.edu/blog/carpet-bo…
Reminder: It's never been safe to run a program out of a directory that contains other untrusted files. insights.sei.cmu.edu/blog/carpet-bo… https://t.co/qHq84xC3gc
When the EDR on your idle workstation suddenly alerts on "ping.exe" run as System/Authority... Turns out it was just a Google Chrome Update.
Bypass the anti-tampering mechanism of a leading EDR to execute malicious code within one of the EDR's own processes and altered the mechanism to gain unique, persistent, and fully undetectable capabilities. : safebreach.com/blog/dark-side…
Microsoft has identified longstanding activity by the Russian-based threat actor we track as Forest Blizzard using a custom tool we call GooseEgg to exploit CVE-2022-38028 in the Windows Print Spooler service to elevate permissions and steal credentials: msft.it/6014YG3oI
MITRE says state hackers breached its network via Ivanti zero-days bleepingcomputer.com/news/security/…
Just released new version of WDACConfig ✅MSFT Defender for Endpoint Advanced Hunting ✅High performance and Accurate logs processing ✅Scalable ✅GUI for cloud log selection and filtering ✅All logic built-in 💯 github.com/HotCakeX/Harde… #Windows #CyberSecurity #BlueTeam 💙
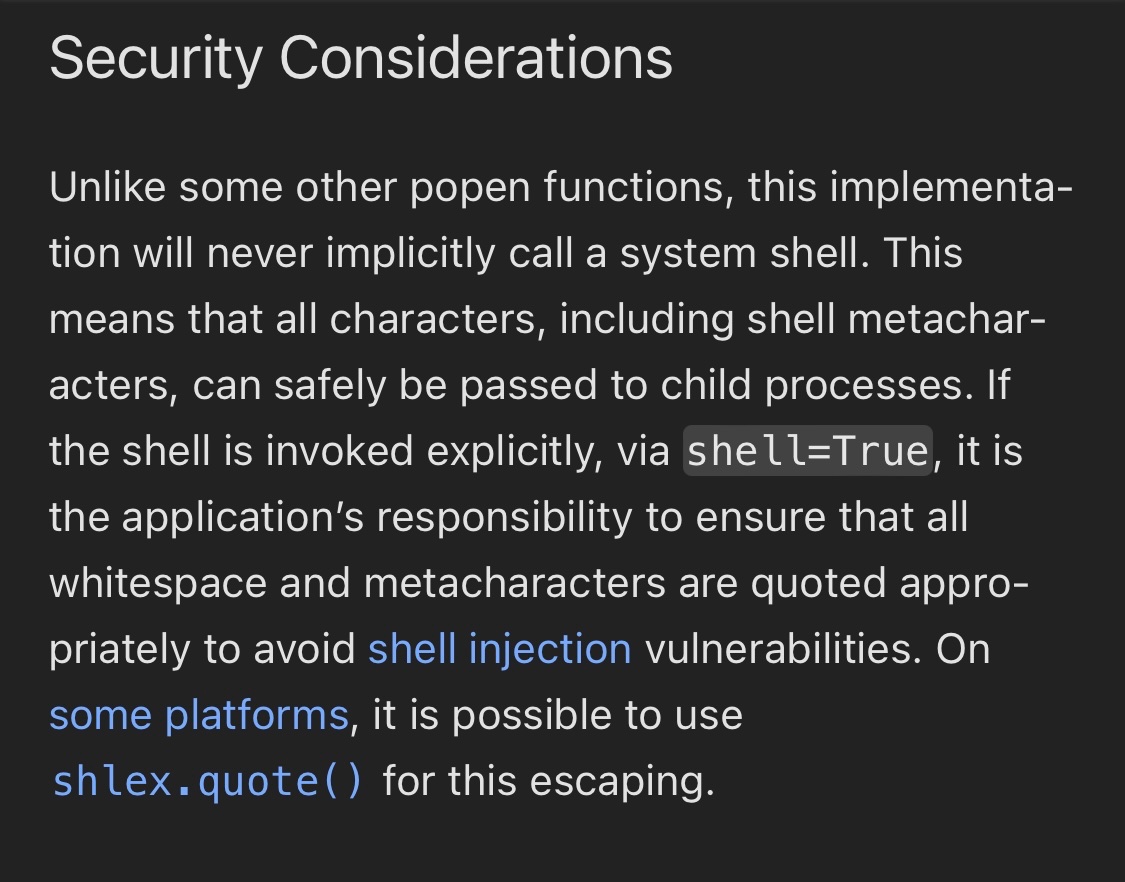
What are the consequences of a vendor for a security product choosing to use a feature (shell=true) that's well documented to introduce vulnerabilities? Oh, right. None. There aren't any.
What are the consequences of a vendor for a security product choosing to use a feature (shell=true) that's well documented to introduce vulnerabilities? Oh, right. None. There aren't any. https://t.co/ompuMx0Soy
ICYMI: Last week @_Mayyhem released the open-source scanner MisconfigurationManager.ps1, which helps administrators more easily identify weaknesses in their SCCM environments. Check out @CSOonline to learn more. ⬇️ ghst.ly/4aWw1AV
CVE-2024-3400: OS Command Injection Vulnerability in GlobalProtect Gateway Severity: CRITICAL (10/10) ⚠️ Poc: github.com/DrewskyDev/CVE… Other info: unit42.paloaltonetworks.com/cve-2024-3400/ volexity.com/blog/2024/04/1…
@Chirag99Artani Nah Watchtowr did a real nice write up labs.watchtowr.com/palo-alto-putt…
Since it's out there now this is what I caught in wild CVE-2024-3400 GET /global-protect/login.esp HTTP/1.1 Host: X User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.36 Accept-Encoding: gzip, deflate, br…
Evidence of exploitation and post-exploitation activity for #CVE20243400 can be found in log files on the FW in these locations: /var/log/pan/gpsvc.log /var/log/pan/md_out.log /var/log/pan/device_telemetry_send.log /var/log/syslog-system.log /var/log/pan/mp-monitor.log
Evidence of exploitation and post-exploitation activity for #CVE20243400 can be found in log files on the FW in these locations: /var/log/pan/gpsvc.log /var/log/pan/md_out.log /var/log/pan/device_telemetry_send.log /var/log/syslog-system.log /var/log/pan/mp-monitor.log
Well the cat is out of the bag. If you are interested in all things authentication and passkeys, my talk on Okta Verify might be of interest pretalx.com/bsides-cymru-2…
SMB Enumeration Cheatsheet, by @0xdf_ 0xdf.gitlab.io/2024/03/21/smb…
@4renwald @fin3ss3g0d Thank you! SMS phishing is pretty much a no-go for red teaming since February, but QR code generation (image and ANSI-based) for dynamically generated lures is definitely something to consider and shouldn't be hard to implement.
XSS Bypass Trick onerror=" 𐂃='',𐃨=!𐂃+𐂃,𐂝=!𐃨+𐂃,𐃌=𐂃+{},𐁉=𐃨[𐂃++],𐃵=𐃨[𐂓=𐂃],𐀜=++𐂓+𐂃,𐂠=𐃌[𐂓+𐀜],𐃨[𐂠+=𐃌[𐂃]+(𐃨.𐂝+𐃌)[𐂃]+𐂝[𐀜]+𐁉+𐃵+𐃨[𐂓]+𐂠+𐁉+𐃌[𐂃]+𐃵][𐂠](𐂝[𐂃]+𐂝[𐂓]+𐃨[𐀜]+𐃵+𐁉+'(𐂃)')()" Resource: aem1k.com/aurebesh.js/

Hildegard Schuckers @HildegardS8099
86 Followers 5K Following
Cheryll Weidemann @CheryllWei70640
86 Followers 5K Following
Nayla Pigeon @nayla_pig
26 Followers 5K Following
Etty Splonskowski @SplonskowskEt
41 Followers 5K Following
RdtHbr_65 @rdthbr39531
1 Followers 926 Following
Brianna Boyarsky @BoyarskyBr85567
39 Followers 5K Following
Leonardo Kwieciński @kwiecz1910
191 Followers 750 Following Software Engineer, Fullstack Development for Web & Mobile Apps, DevOps, Cybersecurity Addict.
Tosmaez @Tosmaez117627
33 Followers 2K Following
JudieWillson @judie29555
200 Followers 2K Following
Joe Farjallah @lefayjey
395 Followers 938 Following Pentester, Red-Purple Teamer / SEC699, OSEP/OSWE/OSCP, RTL/RTO, CARTP / If you don't find me behind my PC, I'm definitely stepping off a plane somewhere...
Imad Madieh @ImadMadie60299
224 Followers 2K Following
Dillon Franke @dillon_franke
416 Followers 281 Following Hacker & Vulnerability Researcher @ Google/Mandiant
Dave Kennedy @HackingDave
206K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Omri Baso @omri_baso
207 Followers 142 Following #OSCP #OSWE #OSED #Reverser #Pentester #RedTeamer #Researcher
CrowdCyber 🌐 @CrowdCyber_Com
342 Followers 2K Following The idea is to create big opportunities in Cybersecurity. Meanwhile we’re Revolutionizing and Democratizing Cybersecurity information.
David Eckel @mcdave2k1
561 Followers 3K Following Cybersecurity nerd | Ethical hacker | Foodie | Hiker | Let's hack the digital world together! #ethicalhacking #infosec #dfir #kaeferjaeger
HTB PRO Labs Writeup @htbprolabs
1K Followers 5K Following HackTheBox Pro Labs Writeups - DM me for details
IAMERICA @EricaZelic
7K Followers 4K Following Your perception is not my reality. My head is in your cloud. Posts don't represent my employer(s).
ahmed khlief 🇵🇸.. @ahmed_khlief
362 Followers 367 Following Purple Teamer who like to attack and defend. #APT-Hunter #NinjaC2 https://t.co/pX9YnnvWmU
Remko Weijnen @RemkoWeijnen
3K Followers 874 Following I like to hack stuff, EUC, Application Compatibility, Security, reverse engineering, Citrix CTP. Opinions are my own.
Cyber XYZ @haneeni61853819
4K Followers 5K Following i am cyber security engineer, Web penetration tester and Bug bounty hunter
Dr. Pinky @TheDrPinky
650 Followers 602 Following PhD, CCDC competitor for 4 years, panoply and cptc competitor. @BsidesSATX social media coordinator. DC726 founder. tweets and thoughts are my own. She/Her
Sandra Walker @SandraW20451870
405 Followers 3K Following
Patrick Davidson Trem.. @HPxpat
428 Followers 2K Following Red Team Lead - Any sufficiently advanced persistent threat is indistinguishable from magic.
Sven Schlüter @secsven
526 Followers 696 Following Advanced Attack Simulation Specialist @ysecurityde - running all sorts of adversary emulations & pentests. https://t.co/RmM5DE1Gmg
Claudio Moletta @redr2e
451 Followers 756 Following @Silentgrid Security co-founder. Adversary Simulation / Penetration Testing.
Rob Fuller @mubix
81K Followers 26K Following Dad / Husband / Marine / Student / Teacher / IAM, Red Team, CTI Director / @Hak5 / @NoVAHackers / @SiliconHBO / @NationalCCDC / @MARFORCYBER Auxiliary
thebairam @thebairam
489 Followers 2K Following Zero-Trust 🧑💻 Aspiring Threat Hunter | ENTHUSIASTIC | All opinions and dreams are mine.
Josh @kernelpanicj0sh
8 Followers 77 Following
Klepisimo @Klepisimo
341 Followers 497 Following I play games and like to sometimes have people watch Affiliate @Twitch @StreamCaptainTV Stream Team - @ChillConfirmed Certified 'Digital Dipshit'
segf4u1t @tuxbuddha
25 Followers 196 Following
Texas Cyber Summit ®.. @texascyber
3K Followers 4K Following 🤠 Texas Deeply Technical 🪓Hacker & Cybersecurity conference - Join us Next Year, ✨ May 21-23, 2025 - J.W Marriott. Austin, Texas 🌎 https://t.co/OBECpq76Q5
Belarchaoui Youcef @BelarchaouiY
103 Followers 564 Following Cyber Security Engineer . Penetration Tester | DFIR | Bug Hunter owner of cve-2022-35728
maximilian @iMaxiMix
71 Followers 901 Following
Jim Sykora @JimSycurity
2K Followers 2K Following I enjoy security, technology, learning, books, & the great outdoors. Trying to be human & kind. Opinions = mine. He/Him/Hän
0xdf @0xdf_
22K Followers 437 Following Training Architect @ HackTheBox "Potentially a legit security researcher" he/him https://t.co/GCcLVlmdQK https://t.co/uQWVpw4nft 0xdf on discord
Conor Ford / Hideouts @RSPN_Hideouts
108K Followers 909 Following Apex Security @Respawn | Speak softly and carry a big ban hammer. | I make music sometimes | My views are my own.
Pirate Software @PirateSoftware
142K Followers 254 Following Game Developer 💛 @Twitch @YouTube @Discord Partner 💜 Making #Heartbound with @RiverMakes & @StijnvanWakeren 💛 Business: [email protected]
Dave W Plummer @davepl1968
46K Followers 59 Following Hi! I'm Dave Plummer. You might remember me from such Windows components as Task Manager, Windows Pinball, Calc, ZIPFolders, Product Activation, etc. Cheers!
ap @decoder_it
7K Followers 257 Following Incident Response and Security Consultant @semperistech . Independent Security Researcher. Cyclist & Scubadiver. MSRC MVR 2022.
MENASecurity @menasec1
3K Followers 40 Following Applied Security Research | Threat Hunting | DFIR | [email protected] 👁🗨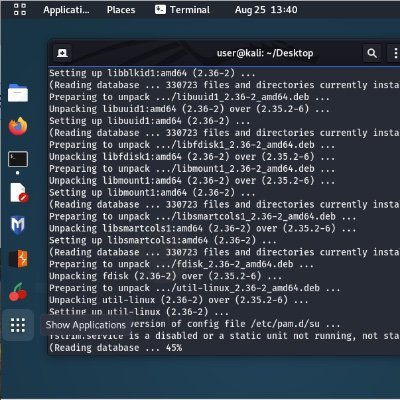
assume_breach @assume_breach
4K Followers 137 Following Why yall have so many calculators in your screenshots? | QAnon Red Team | Labeled Misinformation Propagandist
Mike Takahashi @TakSec
21K Followers 530 Following Pentester | Bug Bounty Hunter | AI Whisperer '><embed src=javascript%26%63%6f%6c%6f%6e%3balert('TakSec')>
April C Wright @aprilwright
20K Followers 5K Following The Infosec Diplomat, Curious Polymath Hacker Speaker Author @defcongroups @oreilly @BSidesBos #Privacy #SecurityAwareness #SecurityArchitecture 🇺🇦🇮🇪🏳️🌈
SV1 @0xSV1
603 Followers 292 Following Red team stuff at @banshie. AD/AAD/Windows security. Detection engineering enthusiast. 5H3LL member. Voice on @5H3LLCAST @ https://t.co/9aY9dEsKAv.
Dillon Franke @dillon_franke
416 Followers 281 Following Hacker & Vulnerability Researcher @ Google/Mandiant
Elliot @ElliotKillick
3K Followers 40 Following Security engineer and researcher | Elliot on Security
Andrew @4ndr3w6S
2K Followers 2K Following Senior Manager of Detection Engineering @HuntressLabs | Prev. Practice Lead, TAC (Purple Team) @TrustedSec | @SpursOfficial Super Fan - COYS!
Megan @mega_spl0it
398 Followers 248 Following Purple Teamer | Probably a SIEM log | Send Memes | Putting the Tater in Administater | Security Spud @TrustedSec
Dark Web Intelligence @DailyDarkWeb
92K Followers 0 Following https://t.co/3gj0T4Udv3 | Your daily dose from the dark side ☠️ For any questions about a post, you can send an email to [email protected]
Dominic Chell 👻 @domchell
16K Followers 530 Following Just your friendly neighbourhood red teamer @MDSecLabs | Creator of /r/redteamsec | https://t.co/3k3EBAZqGd | https://t.co/KwO2OwDOkl
Luca @luca_cloud
31K Followers 188 Following The platform engineering guy. 👾 I ask the best dev teams about their DevOps practices. Then I tweet about it. Product @Humanitec_com, Baker @ Platform Weekly
Austin Hudson @ilove2pwn_
6K Followers 35 Following Offline and looking for work. Living life happy and to its fullest . To reach me, I'm available @ [email protected].
Hacking Articles @hackinarticles
224K Followers 403 Following House of Pentesters Follow us: https://t.co/Y6XOlSOA92
Michael Maltsev @m417z
1K Followers 127 Following About me: https://t.co/rMRTHfHkLh Software: https://t.co/LC4pX87GAC Source code: https://t.co/3OQbob0YQW
ACE Responder @ACEResponder
10K Followers 232 Following Practice threat hunting & detection engineering in a real SIEM with real attacks. Join us and become the best.
Guy Leech @guyrleech
8K Followers 2K Following Consultant|Developer|PowerShell Addict|Grandfather|Comedian|Microsoft MVP|Citrix CTP|Parallels VIPP|Inventor of AppSense Application Manager
IAMERICA @EricaZelic
7K Followers 4K Following Your perception is not my reality. My head is in your cloud. Posts don't represent my employer(s).
Octoberfest7 @Octoberfest73
4K Followers 149 Following Red Team | Offensive Tool Dev | Malware Dev | OSCP | OSEP | RTJC
dr4k0nia @dr4k0nia
5K Followers 97 Following Security Researcher, student in the meantime 👧🏻 I specialize in .NET malware analysis and tooling My Blog ✍🏻 https://t.co/UetpEwyAGq
v1n @0xv1nx0
283 Followers 67 Following | Threat Researcher @ ReliaQuest | Former Detection Engineer @ Red Canary |
Lesley Carhart @hacks4pancakes
168K Followers 7K Following ICS DFIR @dragosinc, martial artist, marksman, humanist, Lvl14 Neutral Good rogue, USAF Ret. Tweet *very serious* things about infosec. Thoughts mine. They/them
Jake Williams @MalwareJake
130K Followers 2K Following Breaker of software | GSE #150 | CTI/DFIR | @ians_security faculty | Bookings: jake at malwarejake dot com | He/him
✖️ par0llel ✖�.. @par0llel
160K Followers 1K Following Par0 | 21 | 🇦🇺| Hi I like drawing and doodling my Ocs :”) | Inquires: [email protected]
Queercon @Queercon
4K Followers 602 Following Supporting LGBTQ+ Hackers for over 15 years and going. Promoting diversity and inclusion of all LGBTQ+ in infosec.
Chetan Nayak (Brute R.. @NinjaParanoid
27K Followers 0 Following DarkVortex Founder | https://t.co/x8K5gzt2RG | Previously RedTeam @CrowdStrike/@Mandiant
MalwareTech @MalwareTechBlog
295K Followers 1 Following Not here anymore. Profiles: https://t.co/sFoOuGmYK2
PwnFunction @PwnFunction
38K Followers 981 Following I make animated computer science videos • product & ai @pdiscoveryio • blog at https://t.co/RLiSNOVQ0W
ippsec @ippsec
111K Followers 348 Following
Alh4zr3d @Alh4zr3d
19K Followers 282 Following Legal Criminal | Twitch cult leader | InfosecPrep founder | Lovecraft scholar | Soros mercenary | Spiritual cargo shorts wearer | Cthulhu fhtagn
Tib3rius @0xTib3rius
56K Followers 442 Following Web App (mostly) Hacker | OnlyFeet Member | Cybersecurity Educator | AutoRecon Dev | Ex-Brit | Links: https://t.co/04RRExvxXj (he/him) 🇺🇸
goproslowyo @goproslowyo
1K Followers 4K Following Hacker. (SRE|DevOps|Cloud|Security) Professional. prev:🚀, @Google, @Apple and @Twilio/@SendGrid who's tweets are these? they're definitely not mine
Nasreddine Benchercha.. @nas_bench
10K Followers 1K Following Detection @nextronsystems | @sigma_hq & LOLDrivers maintainer | Avid learner and passionate about all things #Detection #Sigma
James Kettle @albinowax
70K Followers 83 Following Director of Research at PortSwigger Burp Suite Check out my website for published research, other social platforms & contact details
terjanq @terjanq
9K Followers 222 Following security enthusiast that loves hunting for bugs in the wild. co-founder and player of @justCatTheFish. infosec at @google. opinions are mine.
LiveOverflow 🔴 @LiveOverflow
141K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
cts🌸 @gf_256
51K Followers 621 Following Co-founder @zellic_io & @pb_ctf | YT: https://t.co/nlNai6iiMP Prev: Vector35, Grayshift, Two Sigma, Dfsec | 23yo hacker femboyOne of good friends @cyb3rp_nk put together this fantastic research paper about tactical containment of Active Directory in the event of domain dominance by an adversary. If you work with AD, in IR or anything adjacent, it is well worth your time to read - sans.edu/cyber-research…
''APT28: From Initial Damage to Domain Controller Threats in an Hour (CERT-UA#8399)'' #infosec #pentest #redteam #blueteam medium.com/cyberscribers-…
Bye bye to my admin->kernel priv8 0day 👋 Was sitting on it due to an NDA and i thought it was a quite unique bug, turns out it wasn't. TTP burned 🔥 I might have a blogpost in the future in which i describe how i (differently) exploited it, let's see if time permits...
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
Microsoft please. What is this? Can we please not allow bypasses that are so easy, that a normal user can do it?
This new mechanism seems to completely ignore all supported policies blocking the MS Store and users accessing Winget. This is a pretty considerably issue as far as I see it @JasonSandys @DenelonMs
Reminder: It's never been safe to run a program out of a directory that contains other untrusted files. insights.sei.cmu.edu/blog/carpet-bo…
You can plant a few of your favorite DLLs into \Downloads and bounce off those shiny new Microsoft Store installers 👍 ncrypt.dll, cryptsp.dll, cryptbase.dll, bcrypt.dll, msvcp140_clr0400.dll, profapi.dll, en\StoreInstaller.resources.dll, d3d9.dll, etc.
When the EDR on your idle workstation suddenly alerts on "ping.exe" run as System/Authority... Turns out it was just a Google Chrome Update.
Bypass the anti-tampering mechanism of a leading EDR to execute malicious code within one of the EDR's own processes and altered the mechanism to gain unique, persistent, and fully undetectable capabilities. : safebreach.com/blog/dark-side…
Microsoft has identified longstanding activity by the Russian-based threat actor we track as Forest Blizzard using a custom tool we call GooseEgg to exploit CVE-2022-38028 in the Windows Print Spooler service to elevate permissions and steal credentials: msft.it/6014YG3oI
MITRE says state hackers breached its network via Ivanti zero-days bleepingcomputer.com/news/security/…
Just released new version of WDACConfig ✅MSFT Defender for Endpoint Advanced Hunting ✅High performance and Accurate logs processing ✅Scalable ✅GUI for cloud log selection and filtering ✅All logic built-in 💯 github.com/HotCakeX/Harde… #Windows #CyberSecurity #BlueTeam 💙
What are the consequences of a vendor for a security product choosing to use a feature (shell=true) that's well documented to introduce vulnerabilities? Oh, right. None. There aren't any.
Full @rapid7 analysis of PAN-OS CVE-2024-3400 now available from @stephenfewer and our stellar new research teammate @ChairNectar! Spoiler: It's a two-vuln exploit chain. attackerkb.com/topics/SSTk336…
ICYMI: Last week @_Mayyhem released the open-source scanner MisconfigurationManager.ps1, which helps administrators more easily identify weaknesses in their SCCM environments. Check out @CSOonline to learn more. ⬇️ ghst.ly/4aWw1AV
CVE-2024-3400: OS Command Injection Vulnerability in GlobalProtect Gateway Severity: CRITICAL (10/10) ⚠️ Poc: github.com/DrewskyDev/CVE… Other info: unit42.paloaltonetworks.com/cve-2024-3400/ volexity.com/blog/2024/04/1…
@Chirag99Artani Nah Watchtowr did a real nice write up labs.watchtowr.com/palo-alto-putt…
Since it's out there now this is what I caught in wild CVE-2024-3400 GET /global-protect/login.esp HTTP/1.1 Host: X User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.36 Accept-Encoding: gzip, deflate, br…
Evidence of exploitation and post-exploitation activity for #CVE20243400 can be found in log files on the FW in these locations: /var/log/pan/gpsvc.log /var/log/pan/md_out.log /var/log/pan/device_telemetry_send.log /var/log/syslog-system.log /var/log/pan/mp-monitor.log
Our latest blog post details @Volexity's identification & incident response associated with the Palo Alto Networks GlobalProtect #0day vuln, assigned CVE-2024-3400, that the team found being exploited in the wild. Read more here: volexity.com/blog/2024/04/1… #DFIR #ThreatIntel
Well the cat is out of the bag. If you are interested in all things authentication and passkeys, my talk on Okta Verify might be of interest pretalx.com/bsides-cymru-2…
SMB Enumeration Cheatsheet, by @0xdf_ 0xdf.gitlab.io/2024/03/21/smb…
@4renwald @fin3ss3g0d Thank you! SMS phishing is pretty much a no-go for red teaming since February, but QR code generation (image and ANSI-based) for dynamically generated lures is definitely something to consider and shouldn't be hard to implement.
XSS Bypass Trick onerror=" 𐂃='',𐃨=!𐂃+𐂃,𐂝=!𐃨+𐂃,𐃌=𐂃+{},𐁉=𐃨[𐂃++],𐃵=𐃨[𐂓=𐂃],𐀜=++𐂓+𐂃,𐂠=𐃌[𐂓+𐀜],𐃨[𐂠+=𐃌[𐂃]+(𐃨.𐂝+𐃌)[𐂃]+𐂝[𐀜]+𐁉+𐃵+𐃨[𐂓]+𐂠+𐁉+𐃌[𐂃]+𐃵][𐂠](𐂝[𐂃]+𐂝[𐂓]+𐃨[𐀜]+𐃵+𐁉+'(𐂃)')()" Resource: aem1k.com/aurebesh.js/