C.J. May @lawndoc
Detection Engineer | DevSecOps Evangelist | FOSS boi github.com/lawndoc Joined August 2017-
Tweets794
-
Followers470
-
Following288
-
Likes3K
📰 New blog post! The second entry in my series on DevSecOps program architecture was just published! This one covers how to use automation in your SDLC to produce "secure-by-design" software. Check it out on @GitGuardian's blog! blog.gitguardian.com/secure-by-desi…
Which of you nerds could use these 10 EMC VNX 2.5in SAS drive caddies? They're free if you pay for shipping and send me a pic of your homelab setup
Does anyone know what the differences are between: - Vulnerable Driver ASR rule - WDAC's Vulnerable Driver list in block mode Are they blocking at different stages (file write vs execute)? I assume they are blocking the same set of drivers? techcommunity.microsoft.com/t5/microsoft-s…
Hot take: I think an evolved form of NFTs could have been a much better passwordless experience than the current state of passkey implementation.
Hot take: I think an evolved form of NFTs could have been a much better passwordless experience than the current state of passkey implementation.
NFTs are such a great example of how badly you can mess up the implementation of a technology. Non-fungible tokens could have been a type of authentication factor with some changes, but instead we used them to declare ourselves the owners of pictures of ugly apes.
Update: this position is allowed to be remote for the right candidate
Update: this position is allowed to be remote for the right candidate
"Really hard to backdoor a distro" is 100% survivor bias, but I do agree that the impact of curious eyes on open source projects helps a lot. Imagine if this sort of thing had happened behind closed doors at Microsoft. Not hard to imagine given the long-game played here.
"Really hard to backdoor a distro" is 100% survivor bias, but I do agree that the impact of curious eyes on open source projects helps a lot. Imagine if this sort of thing had happened behind closed doors at Microsoft. Not hard to imagine given the long-game played here.
Lots of analysis of the xz/liblzma vulnerability. Most skip over the first step of the attack: 0. The original maintainer burns out, and only the attacker offers to help (so the attacker inherits the trust of the project built by the maintainer). Read their words👇🏻 1/
Open source maintainer burnout is a clear and present security danger. What are we doing about that?
Open source maintainer burnout is a clear and present security danger. What are we doing about that?
This upstream supply chain security attack is the kind of nightmare scenario that has gotten people describing it called hysterical for years. It’s real. Sleep well. backdoor in upstream xz/liblzma leading to ssh server compromise openwall.com/lists/oss-secu…
If you have a M365 tenant with Advanced Hunting, you can run this query to see all the WiFi networks your devices have connected to in the last week 😄 security.microsoft.com/v2/advanced-hu…
If you have a M365 tenant with Advanced Hunting, you can run this query to see all the WiFi networks your devices have connected to in the last week 😄 security.microsoft.com/v2/advanced-hu…

Crypto Adam 🇬🇧 @CryptoADUK
2K Followers 5K Following Social Media & Marketing @atcryptoremote In the space 👨🚀 since 2009. #Earlyadopter #Trader, #Miner, #Degen Dad! #BitcoinMaxi If you need help, DM me!
Clarisel Pineda @clariselpineda
0 Followers 36 Following
Aaronia AG @Aaronia_AG
13K Followers 15K Following Manufacturer of RF monitoring, direction finding, real-time spectrum analyzer, SDR, CUAS, IQ vector signal generator, network-analyzer, antennas, software & OEM
Frank Korving @Frank_Korving
25 Followers 255 Following
CyberResearcher983655.. @CyberResea53894
9 Followers 71 Following
Dean Sherice @DeanSheric55537
114 Followers 1K Following Challenge to increase the number of fans by more than 1,000 within one month.
Md. Rejwar Rahman Rif.. @rejwar
23 Followers 161 Following Standing before the world and kneeling before ALLAH.
BBG @ItsMeBobbyG
75 Followers 415 Following
Clem Fandango @feege_
385 Followers 866 Following DFIR wannabe Professional brrt/skrrt/adlibber in rap songs Dad Joke extraordinaire former blue checkmark
Allaboutclait @allaboutclait
2K Followers 5K Following Lead IS Analyst, ISO 27001 Lead Implementer, MSc Computing (Information Security & Forensics) Ex DPO. Views my own
Sara Wafy 🇵🇸 @sarahwafy1
48 Followers 775 Following SOC analyst @ Global Brands Group (GBG) #DFIR ❤️💻 Karate❤️🥋
Fhloston @Fhloston_
202 Followers 4K Following
Tom @thetomfilip
199 Followers 711 Following
Paul Martin @paulmartin01892
302 Followers 633 Following Sys Admin - Central Saint Giles, Live in TW
markiemark.eth @goof_eth
3K Followers 3K Following ⟠ Always Be Authentic! Server Admin, Shoe nerd, scissor lift certified, 2 time pepperoni roll eating champion. Gamer ⟠
Michael Dunn | Off Ze.. @OffZeroCyber
232 Followers 721 Following Just a guy that has a passion for tailoring cybersecurity solutions for individuals, startups and small businesses. Lets do more with less and get off zero.
Dr. Anton Chuvakin @anton_chuvakin
40K Followers 8K Following Information security - #SIEM, #DFIR, #EDR formerly at Gartner! Now @GoogleCloud Office of the #CISO; host of @CloudSecPodcast https://t.co/VpKtfz8nXG
Enrico Faccioli @FaccioliEnrico
827 Followers 1K Following CEO & Co-founder @Seedata_io #cybersecurity #deception | Prev. CCO @gyaanaa & Innovation @lgim
JoaquinaBleichner @JoaquinaBl46334
50 Followers 2K Following
jupani @jmoihgaunenl
15 Followers 102 Following
David.B @BoundlessMindX7
25 Followers 677 Following Cyber Pathfinder in Training 🛡️ || WGU Cybersecurity Student 💻🏫 || Intel Insights ✨and AI Enthusiast 🧠 || ⚔️Veteran || Casual 🎮🕹️👾
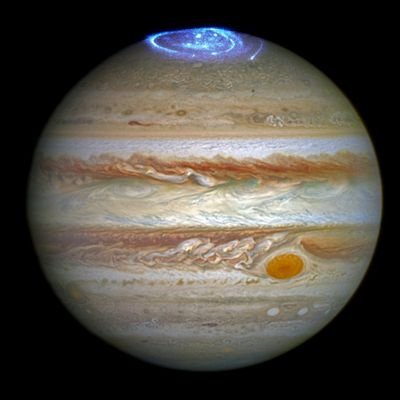
d @danfromjupiter
8 Followers 278 Following
Ahmed Mohamed @slash10_01_neee
130 Followers 2K Following
Mat|n @javr00t
517 Followers 266 Following Bug Hunter|Interested security researching|CTF PLAYER 起死回生 ⚔️
LOKESH JINDAL @jindallokesh83
2 Followers 262 Following
Ibrahim Abdurrahman @ibrahim_haxor
584 Followers 5K Following Android aficionado 🔧 | Expert in software & hardware repair for Android devices 📱 | Solving tech glitches one device at a time 💻 | Your go-to for fixing
Chris Martinez @chriscmartinez
220 Followers 1K Following
Mohammad Javad Abaei @_mjasec
73 Followers 1K Following
Matt Sullivan @msullivan1999
40 Followers 58 Following
Zitni @Zitni10
24 Followers 24 Following
Rakesh Gohel 🇨🇦 @rakeshgohel01
1K Followers 3K Following Entrepreneur. Build. GenAI. EXA AI Chat. cloud-native products, services and solutions. DevOps. CI/CD. Make a difference. https://t.co/ypW0k9l4LR https://t.co/F22DwgzCNb
Wali Khan Kakar @walikhankakar00
92 Followers 2K Following #Cybersecurity #Learner #Bug_Bounty_Hunter Insta: https://t.co/RD0dSVaSU8 LinkedIn: https://t.co/ty1WpVBLpC
ZERO WASTA @0xWASTA
8 Followers 307 Following Full time pentester with zero wasta, SRT, Bug Bounty Hunter.
Joe Stocker @ITguySoCal
6K Followers 1K Following Christian Family Man, CEO of Patriot Consulting (Microsoft Gold Cybersecurity Partner) Author of "Securing M365" Microsoft MVP (Security) (2020-2024)
Naveen @Naveen1345741
0 Followers 40 Following
get.back expert @getbackexpert
116 Followers 613 Following HIT ME UP NOW 👆FOR HACKING Professional hacker 📲💻 with 7 years experience in hacking codes,spying and recovery of data and E files in conjunction
Leticia @bradleyleticia1
235 Followers 3K Following
Richard Ackroyd @rfackroyd
822 Followers 700 Following Manager in Detection Engineering @PwC Global Threat Intelligence | I tweet about cyber threats, attacker techniques and the rest
Younes @YOutaousso58124
319 Followers 5K Following “أَعيشُ عَلى فُتاتِ أَحْلامٍ I live on remnants of dreams” Khaled Ibrahim
Elsayed Osama @Elsayed_Osam0
5 Followers 229 Following
perfect4sec @perfect4sec
509 Followers 4K Following DFIR | Threat Intelligence | Malware Analyst | Researcher | Mexican Cybersecurity Defender Team 🇲🇽 #MXCSDT
Kameron McNicholas @KameronMcNicho5
28 Followers 34 Following
IDontCode @_xeroxz
4K Followers 545 Following Compilers, Math, Windows, Obfuscation, x86-64, Hardware Hacking, and everything in-between Cofounder @BackEngineerLab
cts🌸 @gf_256
51K Followers 621 Following Co-founder @zellic_io & @pb_ctf | YT: https://t.co/nlNai6iiMP Prev: Vector35, Grayshift, Two Sigma, Dfsec | 23yo hacker femboy
HackingHub @hackinghub_io
6K Followers 3 Following
spencer @techspence
6K Followers 2K Following hacker | pentester | ethical threat | wiz bang exploit slinger hiding in the shadows | co-host @cyberthreatpov | offsec @securit360
CoD_Segfault@infosec... @CoD_Segfault
2K Followers 219 Following Maker, hacker, tinkerer, things on my head enthusiast. Into electronics, 3D printing, Wi-Fi, and whatever else has my attention. [email protected]
hogfly 🌻 @4n6ir
1K Followers 93 Following
WifiRumHam @WifiRumHam
1K Followers 1K Following Why not RumHam? https://t.co/g137QVijhq Azure/Sentinel PHISHING-PHISHKITS-MALWARE OSINT FORENSICS Don't mistake my generosity for generosity.
HackerGPT @thehackergpt
8K Followers 0 Following #1 Trusted ethical hacking AI for web and network hacking.
Evan Sultanik @ESultanik
1K Followers 477 Following Ph.D. computer security researcher @TrailOfBits. Editor of and frequent contributor to #pocorgtfo. My CV is a PDF that’s also an NES ROM https://t.co/lDrC4Hz6AI
Michael Barclay @michaelbarclay_
365 Followers 101 Following Architect of Defensive Services @specterops
Justin Ibarra @br0k3ns0und
1K Followers 794 Following threat research & detection engineering lead @elastic by way of @endgameinc | compulsive heavy iron displacer | I always like my own tweets
Gabriel Landau @GabrielLandau
3K Followers 701 Following WinDbg’er @ Elastic Security. Thoughts are my own. Some of my writing: https://t.co/EMJxj12lut More: https://t.co/pxG2OnO1OC @[email protected]
Intel-Ops @Intel_Ops_io
1K Followers 4 Following Adversary Infrastructure Hunting & Training Curated Threat Intelligence Feed (Coming Soon) https://t.co/N9OKrTrvV0 https://t.co/3YFZfEbgpI
SECurityTr8Ker @SECurityTr8Ker
3K Followers 5 Following I monitor the SEC's RSS feed for 8-K and 6-K filings with Item 1.05. Last SEC check: 2024-04-24 23:48:30 ET.
Kijo Ninja @kj_ninja25
2K Followers 87 Following Security Engineer @Microsoft - EDR, XDR, KQL, ThreatHunting | #Triathlete 🏊♂️ 🚴 🏃♀️ National Team (Age group).. or KJ Ninja 🥷 My tweets are my own
John Althouse @4A4133
2K Followers 212 Following Inventor of JA4+ network fingerprinting suite. Co-inventor of encrypted channel fingerprinting methods: JA3/S (TLS) HASSH (SSH) CYU (QUIC) JARM (TLS Servers)
TheWirelessShitshow @WirelessShit
2K Followers 187 Following Usually around 2100 US Mountain Time / 0300 UTC. All the RF! Season 2 !! https://t.co/KOls0kxwNV
Kyle Cucci @d4rksystem
4K Followers 483 Following Threat Research @proofpoint | Author of "Evasive Malware" @nostarch | Talks about cybercrime, threat intel, and malware stuff.
Zack Allen @techyteachme
3K Followers 2K Following security research director @datadoghq , @nyustern mba, CCDC red team, cloud, intel and detection engineering. Creator of Detection Engineering Weekly
hackerfantastic.x @hackerfantastic
102K Followers 4K Following Co-Founder @myhackerhouse cyber security assurance & hacker training ~ ISBN9781119561453 ~ a book on professional hacking. Offensive Lua project.
Cas van Cooten @chvancooten
10K Followers 661 Following Benevolently malicious offensive security enthusiast || OffSec Developer & Malware Linguist || NimPlant & NimPackt author || @ABNAMRO Red Team
Tribe of Hackers @TribeOfHackers
12K Followers 130 Following #TribeofHackers by @marcusjcarey and @jen_jin. Published by @wileytech.
It's FOSS @itsfoss2
118K Followers 131 Following Linux and Open Source Web Portal 🐧 Follow us to - Get the latest Linux and Open Source news 📰 - Learn Linux tips and tutorials 💡 - Enjoy Linux memes 🤣
Proton @ProtonPrivacy
298K Followers 483 Following A better internet starts with privacy & freedom. Take control of your data with @ProtonMail, @ProtonVPN, @ProtonDrive, and @Proton_Pass.
V2 @ZeroMemoryEx
1K Followers 447 Following Cyber Security Consultant | Malware Developer and Analyst
icyguider @icyguider
2K Followers 129 Following
Saad AHLA @d1rkmtr
7K Followers 369 Following d1rkmtr, Security researcher @AlteredSecurity, malware dev, kickboxer
PagedOut @pagedout_zine
4K Followers 9 Following Paged Out! is a free magazine about programming, hacking, security hacking, retro computers, modern computers, electronics, demoscene, and other similar topics.
Corgi @corg_e
48K Followers 3K Following ssh’d into the espresso machine // chaotic neutral // (mostly) harmless pentester // president @bsidesnash // organizes @defcon615
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 569 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger | Stronger Together |
Brad @malware_traffic
1K Followers 49 Following Sharing info on malware samples and infection traffic. Also on Mastodon: @[email protected]
𝙽𝙴𝚃𝚁𝙴�.. @netresec
8K Followers 799 Following Experts in Network Forensics and Network Security Monitoring. Creators of #NetworkMiner, #CapLoader, #PacketCache, #PolarProxy and #RawCap.
nzyme - Network Defen.. @nzyme_defense
742 Followers 468 Following nzyme - Network Defense System, free and open
KQLCafe @KqlCafe
1K Followers 2 Following A Community to make the world a better place with KQL | Learn, share and practice the KQL language | #kql #threathunting #security
DEATHCon @DEATHCon2024
702 Followers 29 Following Online conference 16-17 November 2024 for Detection Engineering and Threat Hunting https://t.co/TpkIGjaqpx
IAMERICA @EricaZelic
7K Followers 4K Following Your perception is not my reality. My head is in your cloud. Posts don't represent my employer(s).
Karsten Hahn @struppigel
22K Followers 703 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
Oliver Lyak @ly4k_
8K Followers 267 Following Yet another security researcher 🔦 Github: https://t.co/7WFOFz17KI
Mehmet Ergene @Cyb3rMonk
11K Followers 421 Following 👉 Learn #KQL for #ThreatHunting, #DetectionEngineering, and #DFIR at https://t.co/uAlYlXIpyV - Founder @BluRavenSec | Microsoft Security MVP | #DataScience@_RastaMouse For those interested there is an open PR to bring pentesting tool into Nix: github.com/NixOS/nixpkgs/…
‼️ Exactly 6 years ago, on 24th April, the Evilginx 2.0 journey began. Thank you to everyone who has used the tool since then. It would not be the same without your involvement 💗
Jesus christ I am so done with @Apple bullshit. Do not ever buy an iphone or an apple, I genuinely have buyers remorse. This is literally the most bullshit system I have ever used. I want to get a single picture off my iphone and onto a windows desktop.... That's all.
I'm thrilled to announce that I'll be presenting a previously-unnamed vulnerability class at @BlueHatIL. Oh, and I'll be dropping 0day. Be sure to stop by, learn something new, pwn the kernel, and have a coffee. It should be a good time. microsoftrnd.co.il/bluehatil/conf…
Yesterday we filed our final brief in the lawsuit by 4 corporate publishers against our nonprofit library: blog.archive.org/2024/04/19/int… Here’s why we’re still fighting for library digital rights, and why YOU should care 🧵
Zuck releasing a billion dollar model is actually wild, like really undermining what OAI is doing. flexing compute like “yea we can do that not a big deal”
@NathanMcNulty @EricaZelic I would also have to say that my concerns are around usability and availability. We can’t even get people to understand and use MFA. How are we supposed to bridge this technology gap, when it comes to passkeys? I have not put a lot of thought or practice into this area though.
@EricaZelic My concerns are around usability, not security. OS and browser vendors need to do better. On security, it's certificate based auth where the private key is protected by PIN and optionally Bio, and also hardware attestation. Service provider gets public keys and metadata only.
@NathanMcNulty @lawndoc @trk_rdy @christruncer Yep, I've blindly enabled it in a bunch of environments from small (less than 300 devices) to large (more than 10,000 devices) and have never ever run into a single issue. Nobody has ever known that we turned it on, including other IT staff.
@lawndoc @trk_rdy @christruncer I don't know enough about LUA and API performance, but I'm guessing there's a reason we can't audit on the exact API call that it blocks Instead, we get a lot of "false positives" if you can call it that. It's really more permissions enumeration type stuff.
@lawndoc @trk_rdy @christruncer Quite a few of those are simply checking if the user is privileged Ever since Microsoft did all that work on this rule back in like 2020, I've not heard of a single legitimate issue (unless you really wanted Infection Monkey or similar to run, lol)
@lawndoc @NathanMcNulty @christruncer @keithmweaver @fabian_bader I like to look at prevalence of each rule, per machine per rule. Learn > informed decision > implement. Taking into consideration what the rule is doing is key. Use the below and play with different rules. //(7) Get FolderPath, FileName, deviceCount and ruleCount for "Block…
I've been searching for the Orange Book to complete my rainbow series for several years. Finally find it up for sale on eBay. I'm super secretive about it to tell no-one.... Checking it daily... and I'm the highest bidder. Last few mins a huge bidding war goes on, I win it but I…
Two people I work with like to collect nostalgic hacker things. It turns out recently they were the only two bidding on an item didn't tell each other and drove the price way up 😂😂😂
@lawndoc @NathanMcNulty @christruncer I think you'd find that the troubleshooting for this rule is next to none. Programs often ask system components for permissions to resources or enumerate what is their permission, in this case LSASS. 99.99999% that is not needed but easier to enumerate them all, those just get…
@trk_rdy @lawndoc @NathanMcNulty @christruncer Definitely agree on this rule being one to just implement in block mode. We have had it enabled for 1-2 years and don't think I've ever seen it cause issues.
We're looking to rectify this entire page, especially the this paragraph. Updates to come. CC: @lawndoc
@trk_rdy @NathanMcNulty @christruncer I assume this is the relevant piece? The thing I struggle with is even if it doesn't cause issues when blocking most of the time, it adds some guess-work to troubleshooting when something isn't working whether the ASR block is interfering when so many blocks are benign.
@lawndoc @trk_rdy @NathanMcNulty @christruncer We enable it on clients without hesitation. Even in the server space the fallout is super limited and mostly related to security software
@lawndoc @NathanMcNulty @christruncer That rule is incredibly safe, and it automatically turned on now. Suggest reading this excerpt (guessing you have but for others if interested) - learn.microsoft.com/en-us/microsof…