Đào Trọng Nghĩa @nghiadt1098
Pwn2own Vancouver 2021/2022. Pwner at @dfsec_com. Tweets are my own. https://t.co/4Y2w4FalIC Joined June 2018-
Tweets854
-
Followers1K
-
Following1K
-
Likes2K
Recently, many people have been asking me on how to get started with their reverse engineering journey. So I will try to share my path and what helped me on the way 🧵
Difficult vulnerabilities make you more cultured. Difficult exploits make you more persistent. Difficult detection evasion makes you wiser. If in doubt, choose the more difficult path.
Excellent LPE write-up by @gabe_k , where he details how suspected compiler changes lead to the introduction of double fetch vulnerabilities. Also discusses a KASLR side channel bypass. PoCs included. Definitely check it out exploits.forsale/24h2-nt-exploi…
I had an inquiry about ACPI checks, and decided to run through how they work and how to mitigate them on VMware and QEMU. It's a quick and dirty write-up, so excuse the brevity. revers.engineering/evading-trivia…
So @j00ru published two posts on Windows Registry; given that there were a lot of fixes in Windows Registry in recent months I expect these to be fun ;) googleprojectzero.blogspot.com/2024/04/the-wi… googleprojectzero.blogspot.com/2024/04/the-wi…
Here's my blog post about CVE-2024-26230. I aim not only to introduce the exploit stage but also hope to share my thoughts on how I completed the exploitation step-by-step in all my posts from now on. whereisk0shl.top/post/a-trick-t…
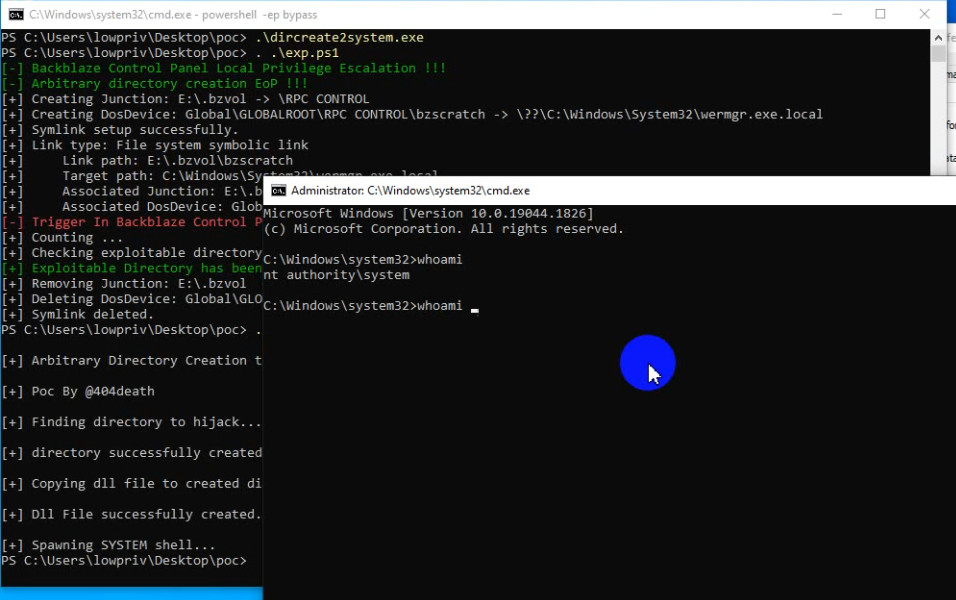
I just created the tool which can help to get NT AUTHORITY\SYSTEM from arbitrary directory creation bugs. github.com/binderlabs/Dir…
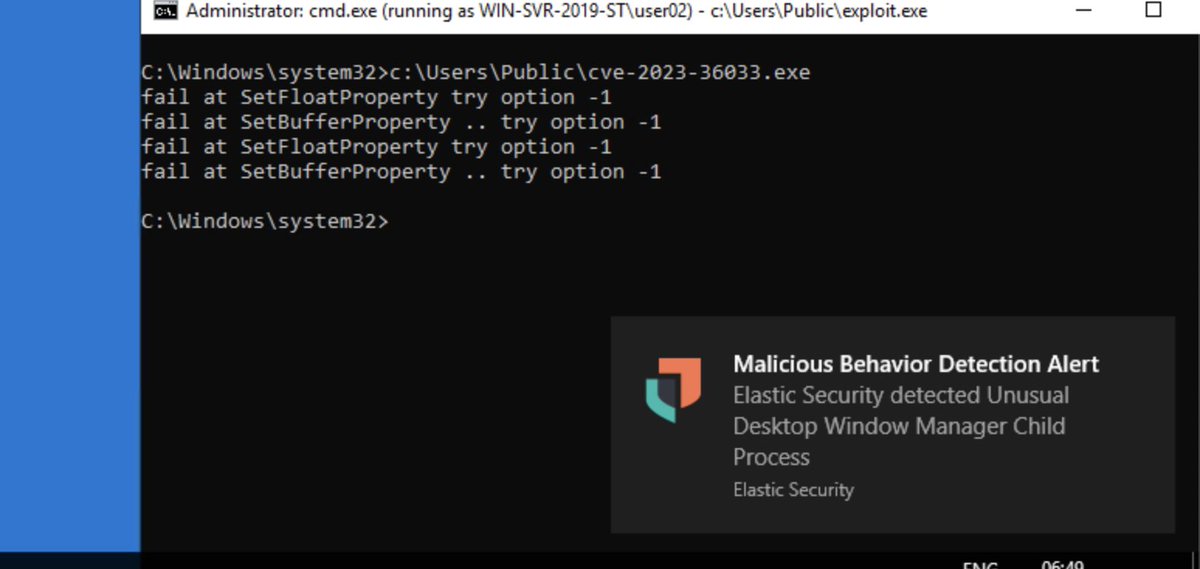
New blog post is up, exploring detection options for some recent In- the- Wild Windows LPE 0- days elastic.co/security-labs/…
If you also need to reverse and debug windows , this simple but useful project maybe can make your life easier. github.com/tinysec/rtypes
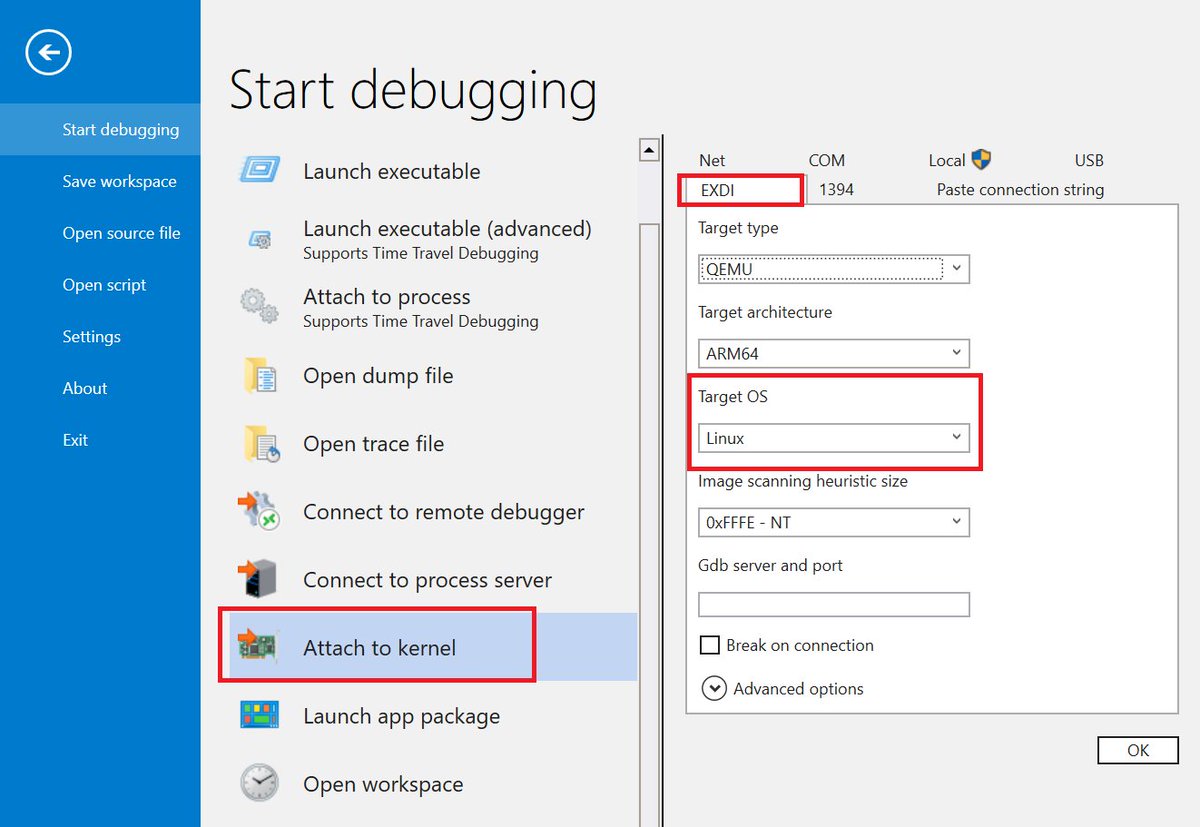
@jvert @markrussinovich Well... It's not quite KD, but WinDbg has supported debugging the Linux kernel via an EXDI connection for some time. Easiest setup is to enable the gdbserver on QEMU and use EXDI in WinDbg selecting "Linux" as the OS. I've source level stepped the Linux kernel doing that...
Debugging the Windows Secure Kernel with JTAG, EXDI, LBR and Intel Processor Trace, Part 3: asset-intertech.com/resources/blog…
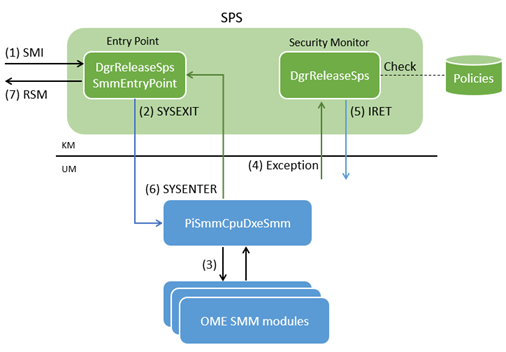
Intel Hardware Shield deep dive: part 1 is user-mode System Management Mode (ISRD). tandasat.github.io/blog/2024/02/2… ISRD is beautifully architected, and I have enjoyed studying it a lot. Excellent work by Intel.
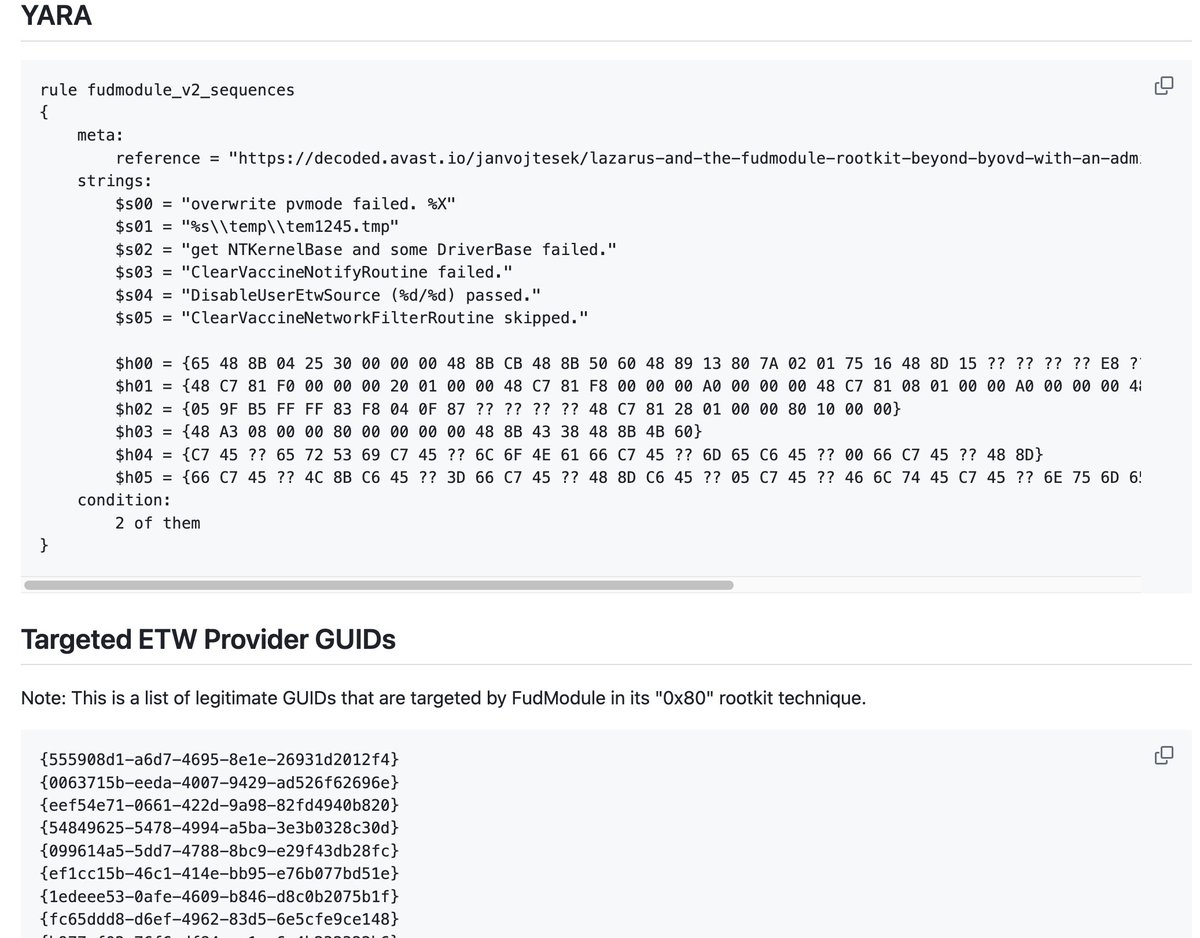
#Lazarus exploited a flaw in the Windows AppLocker driver (appid.sys) as a zero-day to gain kernel-level access and turn off security tools.CVE-2024-21338 Beyond BYOVD with an Admin-to-Kernel Zero-Day decoded.avast.io/janvojtesek/la…
Game hackers really do perform in-depth reverse engineering! A great post on analysis of Valorant's Guarded Regions reversing.info/posts/guardedr… by @Xyrem256 Reverse engineering integrity checks in Black Ops 3 by @momo5502 web.archive.org/web/2023052223…
One of our browser team members(@h0meb0dysj) wrote a detailed analysis on CVE-2024-0517 (Out of Bounds Write in V8). 📍For detailed information, please refer to the provided link. cwresearchlab.co.kr/entry/CVE-2024…
Today, we're disclosing an overlooked, wide-impact bug/attack vector affecting the Windows/COM ecosystem, dubbed #MonikerLink. In Outlook, the bug's impact is far and wide: from leaking NTLM creds to RCE. The same issue may exist in other software, too. research.checkpoint.com/2024/the-risks…
Rootkits, keyloggers, and DKOM (oh my!). The video is finally up for @FuzzySec and I’s BlackHat talk: Close encounters of the advanced persistent kind: Leveraging rootkits for post-exploitation. Check it out ☺️ youtu.be/t7Rx3crobZU?si…
Operating Systems Course: youtube.com/playlist?list=…
I get lots of requests for recommended resources for learning Windows, exploitation, VR, etc. I have some good links but there’s lots of others I don’t know or forgot about. Give me your best suggestions please! Feel free to link your own stuff, I wanna see it!
Our Managed Defense team identified a threat actor, UNC4990, who uses USB devices for initial attacks. They have moved from using seemingly benign encoded text files to hosting payloads on popular websites. Read more: mandiant.com/resources/blog… #Malware #ManagedDefense

Tuan Anh Nguyen 🇻�.. @haxor31337
13K Followers 2K Following 28 y/o Bug Bounty Hunter and Red Teamer at Viettel Cyber Security. Brand Ambassador @Hacker0x01 - Researcher Spotlight @Bugcrowd
Bien Pham 🇻🇳 @bienpnn
4K Followers 398 Following P (Million Live!) / LoveLiver / Shihainin hackerman at @qriousec & @ProjectSEKAIctf traveling around the world (mostly to 🇯🇵) Tiếng Việt / English / 日本語 范阮玉邊
Pham Khanh @rskvp93
1K Followers 286 Following Security Engineer at @calif_io. Winner of Pwn2own Vancouver 2021, Torento 2022, Vancouver 2023. MSRC top 100 2019,2020,2021.
Nguyen The Duc @ducnt_
2K Followers 393 Following Just another web warrior ⚔️ Security Researcher ۞ Principal Security Engineer @vngsecresponse ۞ Pwn2Own 2023 ۞ @vnsec squad ۞ 💰https://t.co/wuyz6IfAbA ۞ nano 💻
LamScun @LamScun
2K Followers 785 Following Researcher of mobile and web security issues. It's safer in the forest than on the internet.
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
Nguyen Xuan Hoang @hoangnx99
631 Followers 107 Following Security Researcher at @vcslab Chief Finance Officer of @u0Kplusplus
huyna @huyna89
747 Followers 928 Following
Md Ismail Šojal @0x0SojalSec
22K Followers 4K Following Cyber_Security_Researchers || 0SINT || Digital Forensics System Analysis / incident Response II Pwn || GH0ST_3xP10iT || 0ld Accounts Suspended @0xSojalSec ||
Khoa Dinh @_l0gg
580 Followers 112 Following
crazyman_army @CrazymanArmy
6K Followers 3K Following CTFer / APT hunter / RedTeam / BlueTeam the member of @r3kapig the leader of @ShadowChasing1 CVE-2022-30190 find job opportunities opinions are own not group
thAI Duong @XorNinja
4K Followers 514 Following Chief at @calif_io | ex-Google | I'm hiring https://t.co/OPTRTOOjlS
b33f | 🇺🇦✊ @FuzzySec
32K Followers 844 Following 意志 / Antiquarian @ IBM Adversary Services / Ex-TORE ⚔️🦅 / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs
KHALIL AHMAD @KhalilAhmad3385
42 Followers 487 Following
Cassidy Waddington @CassidWaddingto
63 Followers 5K Following
v0ldemort (blas) @floridacyborg
165 Followers 488 Following Part of FLARE @Mandiant / @GoogleCloud 💻👾🔬 @uf_fics Alum 🐊 Some Web3 & Mobile Sec 📞💰CTF Welcome Challenge Conqueror 🚩 opinions are my own
Denny Emiliano @denny_emili
51 Followers 5K Following
hái nguyễn @hai0207e
5 Followers 19 Following
Christina @foster46christi
198 Followers 3K Following
T-Rex @0xt_r3x
10 Followers 267 Following
BAALI Mohammed @_EDBAALI
3 Followers 188 Following
Bd55 @Bd5511
3 Followers 15 Following
Joseph Kanko @JosephKanko4
44 Followers 1K Following
Wayne @ssh_rootAlpine
0 Followers 53 Following
Lê Văn Chinh @Vn_sou1
0 Followers 18 Following
Nghi Vi @NghiVi1
20 Followers 104 Following
crazyman @crazyman823886
340 Followers 649 Following CTFer / APT hunter / RedTeam / BlueTeam the member of @r3kapig the leader of @ShadowChasing1 CVE-2022-30190 find job opportunities pre account @CrazymanArmy
stackHeaper @Stackmemory
0 Followers 59 Following Binary Exploitation student. Interested in Low level stuff RE-VR-Fuzzing-Assembly-C/C++ Programming
Thái Lê minh @LmThai99
0 Followers 17 Following
jovial @grepNstep
44 Followers 2K Following Retweet != endorsement. Trust those who seek the truth, doubt those who find it
Shimi Segal @shimisegal8
27 Followers 162 Following Reverse Engineer || Vulnerability Research Student @SelfLearning
Alex @0xr0y4l
1 Followers 288 Following
Ava Cizek @cize_av
77 Followers 5K Following
Alina Parrino @ParrinoAli85716
70 Followers 5K Following
Yuriko Peschong @YPeschong21439
30 Followers 5K Following
Alisa Esage Шевч�.. @alisaesage
35K Followers 143 Following Independent hacker, solo winner Pwn2Own • Building my system of power knowledge @zerodaytraining
Joe @Joe31764327
33 Followers 485 Following
quang vu @quangvuk
59 Followers 861 Following
baysao @baysao
205 Followers 2K Following
Nhan Vo @nhanvoht
13 Followers 349 Following
Oliver Michels @oliver_44227
0 Followers 116 Following
b-rad @bradcyb3rguy
0 Followers 53 Following
Sang @Sang32798028
51 Followers 59 Following
jiya cheka @jiyacheka20
81 Followers 601 Following
Ngo Thanh Van @_EaZyq_
15 Followers 84 Following
Win win @nonameno1082
1 Followers 8 Following
datdt97 @datdt97
16 Followers 81 Following
Md Mosaraf Hossain | .. @mosarafit
24 Followers 194 Following 🏅 Certified by @Google 🎵 #YouTube & #MusicPromoter 📱 #SocialMediaManager ✨🌍 @SEO Analyst #spotify 📌 Webinar registration 📩DM me for Help
Tính @ @tinhxxxx
3 Followers 48 Following
darshanNaik @ismat_darshan
5 Followers 101 Following
Owen @owench3rn
0 Followers 50 Following
Me0x2 @Me0x2Gain
1 Followers 35 Following
kumar_sidhant @sidhant_kumar3
0 Followers 48 Following
PanPanss @HenPanss
11 Followers 64 Following
Kelvin @Kelvin74223507
9 Followers 50 Following
rthhh @rthhh17
2K Followers 572 Following Hyper-V Security Researcher. Black Hat USA 2021/2022 Speaker. MSRC MVR 2019/2020/2022.
Zero Day Initiative @thezdi
77K Followers 17 Following Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities.
Tuan Anh Nguyen 🇻�.. @haxor31337
13K Followers 2K Following 28 y/o Bug Bounty Hunter and Red Teamer at Viettel Cyber Security. Brand Ambassador @Hacker0x01 - Researcher Spotlight @Bugcrowd
cts🌸 @gf_256
52K Followers 624 Following Co-founder @zellic_io & @pb_ctf | YT: https://t.co/nlNai6iQCn Prev: Vector35, Grayshift, Two Sigma, Dfsec | 23yo hacker femboy
Bien Pham 🇻🇳 @bienpnn
4K Followers 398 Following P (Million Live!) / LoveLiver / Shihainin hackerman at @qriousec & @ProjectSEKAIctf traveling around the world (mostly to 🇯🇵) Tiếng Việt / English / 日本語 范阮玉邊
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
Pham Khanh @rskvp93
1K Followers 286 Following Security Engineer at @calif_io. Winner of Pwn2own Vancouver 2021, Torento 2022, Vancouver 2023. MSRC top 100 2019,2020,2021.
starlabs @starlabs_sg
7K Followers 16 Following A Singapore company that discovers vulnerabilities to help customers mitigate the risks against the ever-evolving threat of cyber attacks.
Nguyen The Duc @ducnt_
2K Followers 393 Following Just another web warrior ⚔️ Security Researcher ۞ Principal Security Engineer @vngsecresponse ۞ Pwn2Own 2023 ۞ @vnsec squad ۞ 💰https://t.co/wuyz6IfAbA ۞ nano 💻
Ptrace Security GmbH @ptracesecurity
53K Followers 883 Following Empowering IT Security Professionals through Hands-On Online Courses.
VCSLab @vcslab
2K Followers 31 Following This is the Twitter channel of VCSLab - the research team of Viettel Cyber Security
0xor0ne @0xor0ne
55K Followers 526 Following | CyberSecurity | Reverse Engineering | C and Rust | Exploit | Linux kernel | PhD | My Tweets, My Opinions :) |
Alex Plaskett @alexjplaskett
9K Followers 590 Following Security Researcher | Pwn2Own 2018, 2021, 2022, 2024 | Tweets about 0day, OS, mobile and embedded security.
Haifei Li @HaifeiLi
7K Followers 151 Following For contact in the security community. NOTE: All the tweets are totally my personal opinions, not about any of my current employer stuff.
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
ϻг_ϻε @steventseeley
21K Followers 519 Following Hermetic Initiate. Exploring conscience and the nature of reality. I also hack things. @[email protected]
Chromium Disclosed Se.. @BugsChromium
8K Followers 0 Following Tweets publicly disclosed bugs in Chromium. Not an official Google product. Run by @SecurityMB. Mastodon: @[email protected]
Nguyen Xuan Hoang @hoangnx99
631 Followers 107 Following Security Researcher at @vcslab Chief Finance Officer of @u0Kplusplus
v0ldemort (blas) @floridacyborg
165 Followers 488 Following Part of FLARE @Mandiant / @GoogleCloud 💻👾🔬 @uf_fics Alum 🐊 Some Web3 & Mobile Sec 📞💰CTF Welcome Challenge Conqueror 🚩 opinions are my own
crazyman @crazyman823886
340 Followers 649 Following CTFer / APT hunter / RedTeam / BlueTeam the member of @r3kapig the leader of @ShadowChasing1 CVE-2022-30190 find job opportunities pre account @CrazymanArmy
Stephen Sims @Steph3nSims
20K Followers 601 Following Perpetual Student | SANS Fellow | Musician | Braggart Hater | Gray Hat Hacking | VR | 🏂 | d3adc0de | oNLyHaCKeRs | https://t.co/CadJehomsU
4n0nym4u5 @ArjunGU2
200 Followers 242 Following 21 yo undergraduate. CTF Player @ProjectSEKAIctf | Red Team | Vuln Researcher Seeking for job/internship opportunities. Ex NDay intern @ Exodus Intelligence
Ismael Valenzuela @aboutsecurity
17K Followers 9K Following VP Threat Research & Intelligence @BlackBerry ▪️ Ex @Foundstone @Intel @McAfee ▪️ SANS Senior Instructor, GSE #132 ▪️ Author #SEC530 #SEC568 #ThinkRedActBlue
CZ 🔶 BNB @cz_binance
9.0M Followers 2K Following @binance co-founder and former CEO, holder of #bnb #btc
thaihust @thaihust
6 Followers 51 Following
Gareth Evans @kryc_uk
469 Followers 140 Following Security Researcher. Microsoft Edge Security Lead. Words & Opinions are my own.
Kelvin Chan @KelvinMsft
917 Followers 13 Following @Microsoft Windows Core Kernel Engineer | @HongKong People in America | Opinions are my own.
Aleksei Kulaev @flat_z
10K Followers 948 Following Console hacker, former Kaspersky Team Lead of Exploits & Network Threat Detection, security researcher. For tips (thx!): https://t.co/VxJMiawFpP
h0mbre @h0mbre_
12K Followers 577 Following tryhard at linux kernel && avatar is by Ching Yeh: https://t.co/oanjFPPhe7
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
Ramin Nafisi @MalwareRE
5K Followers 2K Following Malware RE Lead @ Microsoft Threat Intel Center (MSTIC) || Fascinated & humbled by your complex malware, me vs. your code, not me vs. you/yours.
crazyman_army @CrazymanArmy
6K Followers 3K Following CTFer / APT hunter / RedTeam / BlueTeam the member of @r3kapig the leader of @ShadowChasing1 CVE-2022-30190 find job opportunities opinions are own not group
Truong Nhat Tran🇻�.. @nhat_truongsec
170 Followers 330 Following Product Security, RedTeam, Security Blogger: https://t.co/LBYn1ENRUv Parttime Bug bounty Hunter (less time now:v) @Hacker0x01-@SynackRedTeam
Chavda Zeel @ChavdaZeel
590 Followers 4K Following Pentester | @synack | Web Security | Learner. My tweets are my own
Prateekg147 @prateekg147
4K Followers 1K Following Focusing on *OS and Browser Security. Research @8ksec
Igor Kuznetsov @2igosha
2K Followers 325 Following Reverse engineering, soldering, programming, digital forensics & random stuff | Director @ Kaspersky GReAT | Tweets are my own
t3ft3lb @t3ft3lb
2K Followers 182 Following Threat researcher, Malware analyst All tweets represent my personal opinion
Leonid Bezvershenko @bzvr_
3K Followers 286 Following Studying math, reversing and Twitter... | Security Researcher @ Kaspersky, GReAT | Drovosec CTF team | Tweets are my own
Fabio Assolini @assolini
13K Followers 485 Following Cybersecurity Expert at @Kaspersky. Cyberthreats hunter. Infosec Speaker. Jesus follower. Tweets in 🇬🇧🇪🇸🇧🇷🇮🇹
Andrew Richards @ARichardMSFT
853 Followers 230 Following Principal Developer in Windows Reliability - !analyze, Symbol Protocol, Sysinternals ProcDump. Co-host Channel 9 Defrag Tools (@defragtools) and Inside Show.
Clint Rutkas @ClintRutkas
9K Followers 2K Following Lead for developer experiences on @Windows. Windows Terminal, Microsoft PowerToys, Sudo on Windows, Dev Home and more. I do #woodworking too. Happy to help.
frust @frust93717815
1K Followers 399 Following Majoring in Civil Engineering & English as Vulnerability researcher.
Danis Jiang @danis_jiang
2K Followers 896 Following Yuhao Jiang / former ctfer @ Vidar-Team / Security Researcher @ Ant Group Light-Year Security Lab / GeekPwn 2022 / Pwnie Awards 2023 / Tianfu Cup 2023
Longhorn @never_released
14K Followers 130 Following Kernel/hypervisor engineer @awscloud EC2. Hobby @checkra1n. Mastodon: https://t.co/DsXP8PFgL0 Bluesky: https://t.co/dAOfFSSqY4
Benoît @benoitsevens
745 Followers 134 Following
ocdsec @0xocdsec
3K Followers 4K Following
Microsoft Threat Inte.. @MsftSecIntel
180K Followers 1K Following We are Microsoft's global network of security experts. Follow for security research and threat intelligence.
Tuấn Kiệt @allforest01
115 Followers 555 Following
Satoshi Tanda @standa_t
7K Followers 358 Following Engineer & Trainer. My DM is open. https://t.co/hqylaDLtNv
b1n @b1n0hypn05
3 Followers 81 Following
hex nomad @hexnomad
978 Followers 265 Following researcher, developer, @fieldeffectsoft, [email protected]Recently, many people have been asking me on how to get started with their reverse engineering journey. So I will try to share my path and what helped me on the way 🧵
Difficult vulnerabilities make you more cultured. Difficult exploits make you more persistent. Difficult detection evasion makes you wiser. If in doubt, choose the more difficult path.
Excellent LPE write-up by @gabe_k , where he details how suspected compiler changes lead to the introduction of double fetch vulnerabilities. Also discusses a KASLR side channel bypass. PoCs included. Definitely check it out exploits.forsale/24h2-nt-exploi…
Raise your hand if you saw a rust program segfault today ✋
Today Microsoft open-sourced MS-DOS 4.0. You can check it out here: github.com/microsoft/MS-D…
I had an inquiry about ACPI checks, and decided to run through how they work and how to mitigate them on VMware and QEMU. It's a quick and dirty write-up, so excuse the brevity. revers.engineering/evading-trivia…
So @j00ru published two posts on Windows Registry; given that there were a lot of fixes in Windows Registry in recent months I expect these to be fun ;) googleprojectzero.blogspot.com/2024/04/the-wi… googleprojectzero.blogspot.com/2024/04/the-wi…
Project Zero: The Windows Registry Adventure #1: Introduction and research results googleprojectzero.blogspot.com/2024/04/the-wi…
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
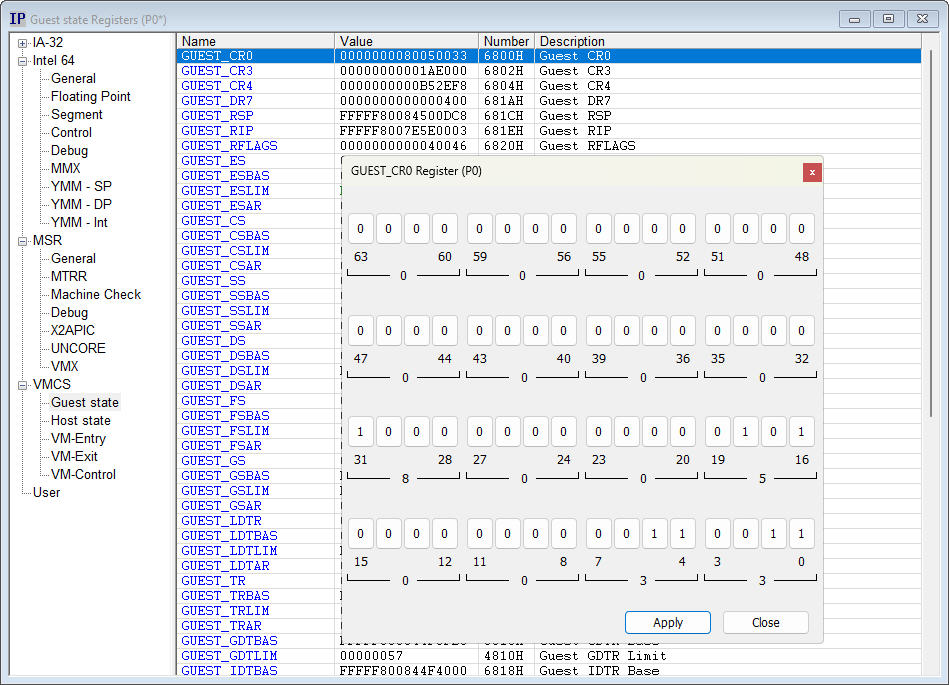
I'm digging even deeper into hypervisor debugging. This viewer enables visual reading and writing of bit fields within the VMCS Guest state, Host state, entry, exit and control fields.
XZ backdoor story – Initial analysis securelist.com/xz-backdoor-st…
Here's my blog post about CVE-2024-26230. I aim not only to introduce the exploit stage but also hope to share my thoughts on how I completed the exploitation step-by-step in all my posts from now on. whereisk0shl.top/post/a-trick-t…
New Google Chrome Blog: blog.chromium.org/2024/04/fighti… Windows 11 VBS and TPM defaults are used by Chrome to prevent cookie theft. "Chrome will use facilities such as Trusted Platform Modules (TPMs) for key protection, which are becoming more commonplace and are required for…
I spent the last 5 months reverse engineering Denuvo's protection in Hogwarts Legacy and finally managed to bypass it using more than 2000 hooks 😂 One of the toughest challenges of my life. Here's my blog post about it: momo5502.com/posts/2024-03-…
I just created the tool which can help to get NT AUTHORITY\SYSTEM from arbitrary directory creation bugs. github.com/binderlabs/Dir…
New blog post is up, exploring detection options for some recent In- the- Wild Windows LPE 0- days elastic.co/security-labs/…
Uploaded my script here: github.com/yardenshafir/W… It's very POC-like, requires some manual steps in the debugger and I'm sure someone with read programming skills can make it way nicer (please do!). But it works so I'm calling it done.
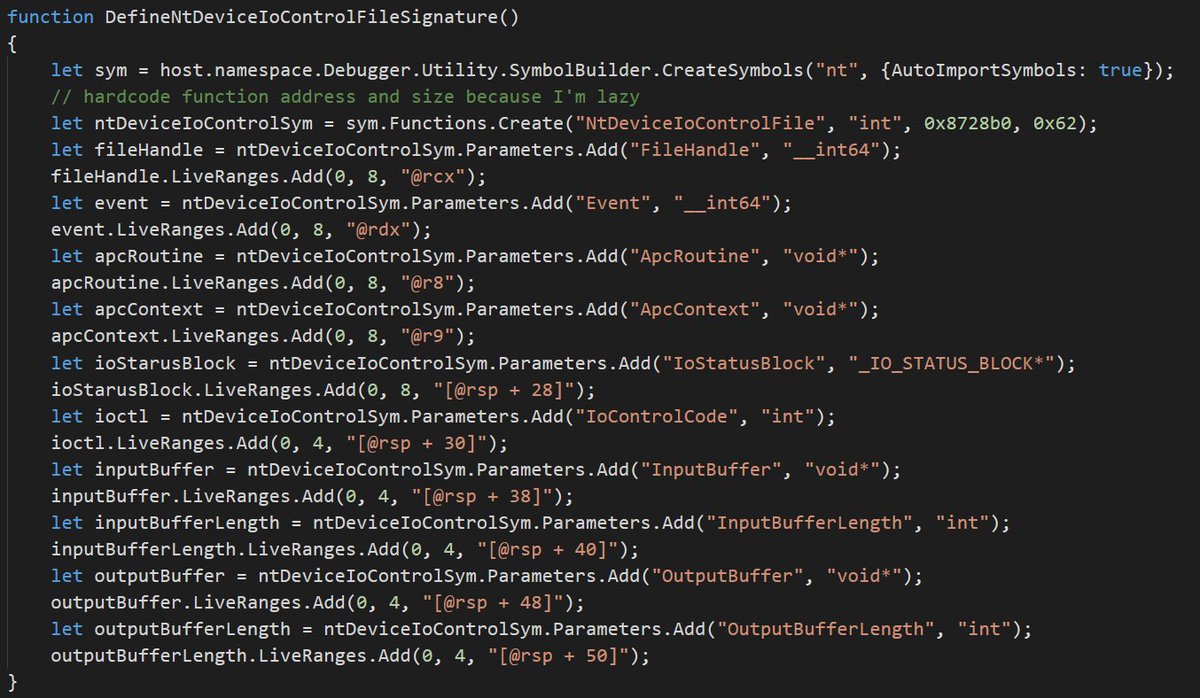
Anyone who uses WinDbg a lot should learn to use Symbol Builder (by @wmessmer). Using it here to define a function signature and combining it with FileSystem module to write log all IOCTL requests to a file.
Good luck to all #Pwn2Own partecipants. A friendly reminder that for real money, not peanuts, you can turn to your friendly zero-day broker :)