Samuel Groß @5aelo
V8 Security technical lead. Previously Project Zero. Personal account. Also @[email protected] and https://t.co/aVitnPjBie phrack.org/author_saelo.h… Zürich, Switzerland Joined May 2013-
Tweets735
-
Followers24K
-
Following499
-
Likes2K
Big day for the V8 Sandbox: * Now included in the Chrome VRP: g.co/chrome/vrp/#v8… * Motivation & goals discussed in a new technical blog post: v8.dev/blog/sandbox If there is ever a Sandbox "beta" release, this is it!
New V8 Sandbox design document is out: docs.google.com/document/d/12M… This discusses how a hardware-based sandbox instead of the currently purely software-based one might look like in a somewhat distant future (if at all)
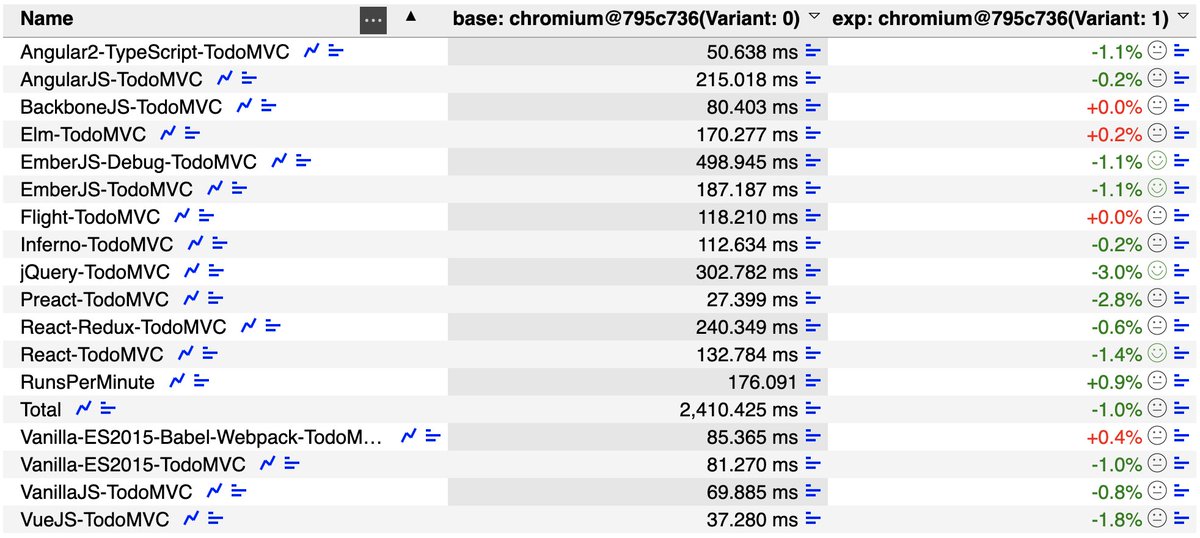
Some early performance numbers for the V8 Sandbox: looks like with most of the performance critical parts in place now, the overall performance cost of this future security boundary is only around 1% on popular benchmarks \o/ More results are linked from chromium-review.googlesource.com/c/v8/v8/+/5206…
The first #v8CTF submission is now public: bughunters.google.com/reports/vrp/38… Note that the current flag is still up for grabs, maybe M118 is unhackable? ;P You should also check out @madStacks3's excellent writeup at madstacks.dev/posts/Start-Yo…
I've been meaning to write this for some time now and finally got around to it: a "V8 Sandbox Glossary" document that briefly explains the most important terms/concepts used for the sandbox and links to the respective design documents: docs.google.com/document/d/10Z…
Venturing into the world of browser exploitation? these two @5aelo's Phrack articles are an essential rite of passage 👇🌐 phrack.org/issues/70/3.ht… phrack.org/issues/70/9.ht…
The first #v8CTF submission is in \o/ This was chromium-review.googlesource.com/c/v8/v8/+/4773…
We just started the #v8CTF: a new exploit bounty program for v8! * $10,000 * N-day vulnerabilities are in scope, but limited to first submission per deployed v8 version * unlimited for self-found bugs (on top of regular VRP) More info here: github.com/google/securit…
Some really cool recent work by @_tsuro: * We now have a V8 exploit bounty ($10k) in the form of the V8CTF: github.com/google/securit… * A blog post about our CFI plans: v8.dev/blog/control-f…
How can you show that a bug is exploitable without actually writing an exploit? Exploit equivalence classes. blog.isosceles.com/exploit-equiva…
I am happy and very excited to be presenting V8 Security’s latest fuzzing work at HITCON!
Sharing another V8 Sandbox design document more widely: docs.google.com/document/d/1CP… This one discusses how to protect code pointers - probably the most performance sensitive part touched by the sandbox - with (almost) no performance overhead.
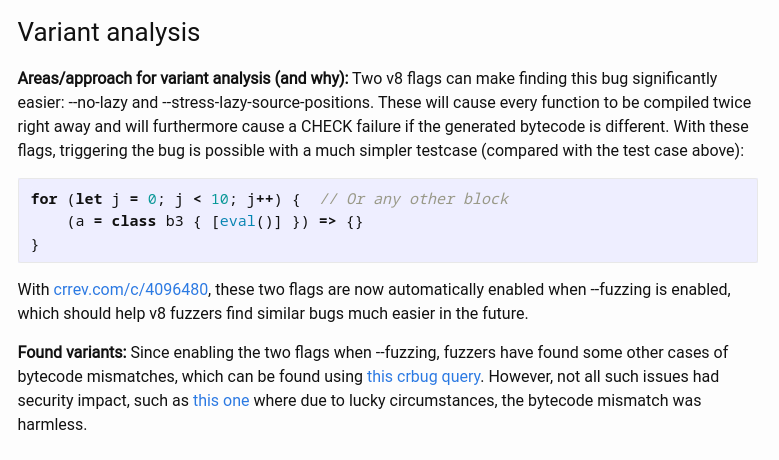
😍 New RCA! The v8 security team is at it again with a new RCA for CVE-2022-4262, the #itw0days patched in December 2022. I really like how they modified the fuzzing flag to better find this class of bugs! Thank you @5aelo! 🔥 googleprojectzero.github.io/0days-in-the-w…

cts🌸 @gf_256
52K Followers 624 Following Co-founder @zellic_io & @pb_ctf | YT: https://t.co/nlNai6iQCn Prev: Vector35, Grayshift, Two Sigma, Dfsec | 23yo hacker femboy
0xor0ne @0xor0ne
55K Followers 526 Following | CyberSecurity | Reverse Engineering | C and Rust | Exploit | Linux kernel | PhD | My Tweets, My Opinions :) |
Saar Amar @AmarSaar
18K Followers 362 Following Reversing, exploits, {Windows, Hyper-V, *OS} internals, mitigations. Apple SEAR. Opinions are my own. @[email protected]
Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
h0mbre @h0mbre_
12K Followers 576 Following tryhard at linux kernel && avatar is by Ching Yeh: https://t.co/oanjFPPhe7
mdowd @mdowd
32K Followers 744 Following Internet Hacker. Founder of @vigilant_labs. Previously, co-founder of Azimuth Security (now L3Harris Trenchant)
stacksmashing @ghidraninja
47K Followers 430 Following Security researcher with a focus on hardware & firmware. I occasionally publish stuff on YouTube. Co-founder of @hextreeio. Contact: [email protected]
Alex Plaskett @alexjplaskett
9K Followers 590 Following Security Researcher | Pwn2Own 2018, 2021, 2022, 2024 | Tweets about 0day, OS, mobile and embedded security.
ϻг_ϻε @steventseeley
21K Followers 519 Following Hermetic Initiate. Exploring conscience and the nature of reality. I also hack things. @[email protected]
Gareth Heyes \u2028 @garethheyes
32K Followers 1K Following JavaScript for hackers: Learn to think like a hacker. https://t.co/e0aNEbEDk5
Maddie Stone @maddiestone
64K Followers 847 Following Security Researcher - Google's Threat Analysis Group | 0days all day. Love all things bytes, assembly, and glitter. she/her.
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
simo @_simo36
7K Followers 107 Following
Julien | MrTuxracer �.. @MrTuxracer
30K Followers 417 Following Freelancer | Full-time #BugBounty | @Hacker0x01 H1-Elite & $1,500,000 Hacker | ❤️ IDA Pro
kylebot @ky1ebot
5K Followers 315 Following CTF player @Shellphish | PhD Student @ASU | @angrdothorse dev | Author of how2heap | Vulnerability Research Hobbyist | @[email protected]
PwnFunction @PwnFunction
38K Followers 981 Following I make animated computer science videos • product & ai @pdiscoveryio • blog at https://t.co/RLiSNOVQ0W
Alisa Esage Шевч�.. @alisaesage
35K Followers 142 Following Independent hacker, solo winner Pwn2Own • Building my system of power knowledge @zerodaytraining
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
Tomer Shinar @tome78467
1 Followers 9 Following
Jack Ma @LovelyJupiter
0 Followers 71 Following
DUGA ADOM JOHN @djohnadom
3 Followers 48 Following
yagyuu @topyagyuu
3 Followers 71 Following
Danci @Danci33899483
1 Followers 32 Following
Reyes Amelia @reyes_amelia28
27 Followers 414 Following Trader | Investor | Entrepreneur 📈 Bitcoin Mining ,📊 NFT / Market Analysis📉 Crypto Currencies Investment 🪙 DM for more info. +18605101558
tester @xxtesterxx
1 Followers 246 Following
Nitesh Surana @_niteshsurana
325 Followers 657 Following Cloud Security Research w/ @trendmicro | Microsoft MVR | Black Hat USA, Asia Speaker | Prev. Blue Teaming w/ @tcs | TCS HackQuest 3.0 Finalist
Ahmed Eltaher @ahmedheltaher
6 Followers 117 Following
figuzt @figuzt_
13 Followers 92 Following
🎙Cyber Distortion .. @DistortionCyber
2K Followers 2K Following The Cyber Distortion Podcast covers all of today's relevant topics related to anything and everything in the world of Cybersecurity. Our opinions are our own!
Qirui @Qirui28124
60 Followers 1K Following
pintokhaw @pintokhaw
1 Followers 26 Following
SecuRepairs (pron. Se.. @securepairs
934 Followers 185 Following An organization of FUD fighters: cyber security and IT pros who support a digital right to repair that benefits consumers, small businesses & the planet.
Amine Miller @Amine__Miller
62 Followers 764 Following
sink0Rswim @laceandload
110 Followers 2K Following
Michelangelo S. @m1chlangel0
2 Followers 29 Following
V0lk3n @v0lk3n
310 Followers 574 Following OSCP & OSWP Certified | CyberSecurity enthusiast | BlueSky : https://t.co/WRcpGTib9g
LegacyStranger @legacystranger1
186 Followers 427 Following
Black Swan @blackswan171
510 Followers 5K Following
WaSsLt_ @WaSsLt_
0 Followers 5 Following
A3391gent @a3391gent
1 Followers 99 Following
A @A35928709
2 Followers 40 Following
Exploit505 @Exploit505
86 Followers 741 Following #Cybersecurity Entrepreneur from #Nicaragua | https://t.co/t573kyGIMU
Keven Belanger @KevenBelanger
463 Followers 5K Following Single father of 3 boys / Asperger / CEO / IT / Infosec / OSINT / AI / ML / Robotics / Photography
unpWn4bl3 @unpWn4bl3
3 Followers 47 Following
user31fibcxw2 @user31fibcxw2
0 Followers 537 Following
maison millemont @maison1000mont
137 Followers 2K Following
Wayne @ssh_rootAlpine
0 Followers 53 Following
Jinu Kumar S V @JinuKumarSV
16 Followers 21 Following
Emmanuel T Odeke @odeke_et
2K Followers 651 Following Building @orijtech, @golang, cloud computing, cybersecurity, accelerating industrialization, technology etc. Always learning!
lasterr0r @lasterr0r
0 Followers 296 Following
EthicalVamp @EthicalVamp
2 Followers 40 Following
Wes Johnson @thewesjohnson
56 Followers 284 Following Angel Investor | Startup Advisor. Views are my own
VivianDrake @VivianD70463414
37 Followers 784 Following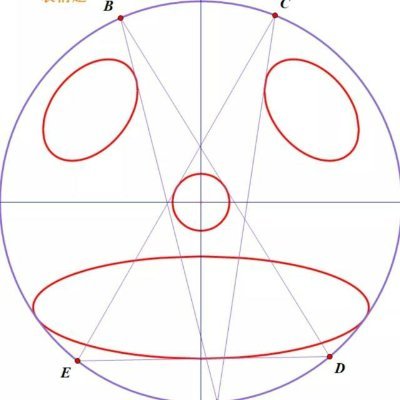
XiaozaYa @XiaozaYa84510
1 Followers 34 Following
maru @maru1766932
82 Followers 585 Following
Lucas Santos @LucasSanto64526
2 Followers 49 Following
joeinthetoilet @gera1t0fnarnia
2 Followers 34 Following
Zero Day Initiative @thezdi
77K Followers 17 Following Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities.
Saar Amar @AmarSaar
18K Followers 362 Following Reversing, exploits, {Windows, Hyper-V, *OS} internals, mitigations. Apple SEAR. Opinions are my own. @[email protected]
Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
mdowd @mdowd
32K Followers 744 Following Internet Hacker. Founder of @vigilant_labs. Previously, co-founder of Azimuth Security (now L3Harris Trenchant)
Alex Plaskett @alexjplaskett
9K Followers 590 Following Security Researcher | Pwn2Own 2018, 2021, 2022, 2024 | Tweets about 0day, OS, mobile and embedded security.
ϻг_ϻε @steventseeley
21K Followers 519 Following Hermetic Initiate. Exploring conscience and the nature of reality. I also hack things. @[email protected]
Maddie Stone @maddiestone
64K Followers 847 Following Security Researcher - Google's Threat Analysis Group | 0days all day. Love all things bytes, assembly, and glitter. she/her.
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
Alisa Esage Шевч�.. @alisaesage
35K Followers 142 Following Independent hacker, solo winner Pwn2Own • Building my system of power knowledge @zerodaytraining
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
Ivan Fratric 💙💛 @ifsecure
17K Followers 192 Following Security researcher at Google Project Zero. Tweets are my own. Backup @[email protected]
offensivecon @offensive_con
21K Followers 1 Following OffensiveCon is a highly technical international security conference focused on offensive security only. Organized by @bluefrostsec @offensivecon.bsky.social
Patrick Wardle @patrickwardle
37K Followers 959 Following Founder of the Objective-See Foundation 🛠️🍎
Brandon Falk @gamozolabs
21K Followers 283 Following I find and exploit 0day, develop OSes, hypervisors and emulators, design massively parallel data structures and code, and do precision machining! Optimization❤️
tihmstar @tihmstar
65K Followers 215 Following Finding offsets since 2017 Email: [email protected] Patreon: https://t.co/FdMYUYWbqr
Gynvael Coldwind @gynvael
38K Followers 1K Following security researcher/programmer/director @ HexArcana Cybersecurity GmbH ⁂ @pagedout_zine ⁂ @DragonSectorCTF ⁂ https://t.co/ShG2c5As1K ⁂ ex-Google ⁂ he/him
[email protected] @amyexp
580 Followers 390 Following security gal | resident Chrome Security border collie && VRP lead | outdoor super-enthusiast | pop culture glutton | she/her/y'all | not here much / see uname
madStacks @madStacks3
78 Followers 30 Following
Donncha Ó Cearbhaill @DonnchaC
5K Followers 5K Following Head of Security Lab at @AmnestyTech - Hunting spyware and unlawful surveillance targeting civil society (He/Him) - Fedi: @[email protected]
Boris Larin @oct0xor
17K Followers 518 Following Former console hacker (PS3/PS4). Hunting in the wild 0-days at Kaspersky GReAT. All tweets are my own.
intrigus @intrigus_
191 Followers 179 Following I create and break stuff. GitHub ⭐. @KITCTF. #Java, #CodeQL and #libgdx. Github: https://t.co/2eJKNdhQaV Security stuff: https://t.co/eg564HmccR
Institute for the Stu.. @TheStudyofWar
717K Followers 3K Following ISW is a policy research organization focused on U.S. national security. Email: [email protected]. For more: https://t.co/FO1PVyOnYB
OpenAI @OpenAI
3.4M Followers 0 Following OpenAI’s mission is to ensure that artificial general intelligence benefits all of humanity. We’re hiring: https://t.co/dJGr6LgzPA
Andrej Karpathy @karpathy
979K Followers 905 Following 🧑🍳. Previously Director of AI @ Tesla, founding team @ OpenAI, CS231n/PhD @ Stanford. I like to train large deep neural nets 🧠🤖💥
Ashley Shen @ashl3y_shen
3K Followers 939 Following Security researcher @TalosSecurity / Ex-Googler / Black Hat & HITCON Review Board / Organizer of @rhacklette41. These tweets are my own not my employer's.
Повернись ж.. @BackAndAlive
294K Followers 137 Following Ukraine's largest Foundation providing assistance to the Army. We raised more than $330 mil for the🇺🇦Army. 📬[email protected]
Daniel Gruss @lavados
10K Followers 477 Following #InfoSec Professor @ #TUGraz. #meltdown, #spectre, #rowhammer, cache attacks. Produced a side channel security sitcom. @[email protected]
Michael Schwarz @misc0110
8K Followers 484 Following InfoSec Faculty @ #CISPA. Side-channel attacks. Exploiting microarchitectures. #Meltdown #Spectre #ZombieLoad #SGX #JavaScript #Rowhammer
Yann LeCun @ylecun
711K Followers 718 Following Professor at NYU. Chief AI Scientist at Meta. Researcher in AI, Machine Learning, Robotics, etc. ACM Turing Award Laureate.
0xTen @_0xTen
673 Followers 666 Following Human state machine • linux kernel • research @osec_io • CTF/pwn @cor_ctf + @eltctfbr
Event Horizon 'Scope @ehtelescope
89K Followers 116 Following We image black holes (M87* (2019), Sgr A* (2022)) with an Earth-sized telescope https://t.co/q3YH4dHw3g https://t.co/pDMEvA87en
Human Rights Watch @hrw
5.1M Followers 21K Following Exposing #HumanRights abuses around the world Join us to help end them! Staff: https://t.co/2JflyBeYHI HRW social accounts https://t.co/AIpbUxDqR4
Pierre H. 🔥🌸 @pedantcoder
4K Followers 188 Following present: security (zalloc, kalloc_type, IPC, VM, …) | past: GCD, synchro, objc_direct, perf… | timeless: 🇫🇷 snark | @[email protected]
Alexey Navalny @navalny
3.0M Followers 1K Following Основатель Фонда борьбы с коррупцией, лидер партии Россия Будущего.
Sahil Bloom @SahilBloom
1.1M Followers 127 Following Exploring my curiosity and sharing what I learn along the way. Gave up a grand slam on ESPN in 2012 and still waiting for it to land.
Eliot Higgins @EliotHiggins
310K Followers 3K Following Founder and creative director of @Bellingcat and director of Bellingcat Productions BV. Author of We Are Bellingcat. Tonal Whiplash Zone.
Bethany 貝書穎 @BethanyAllenEbr
85K Followers 2K Following Previously, China reporter @axios. Author BEIJING RULES, Financial Times Best Business Books of 2023. Currently in Taipei, via Beijing, Nanjing, Xiamen, and DC.
a16z @a16z
763K Followers 47 Following we invest in software eating the world https://t.co/A9eTFq6Xbx https://t.co/MXGUBJoMi4 Sign up for our newsletters: https://t.co/vkcLgyb2qX
The Kyiv Independent @KyivIndependent
2.1M Followers 37 Following Become a member: https://t.co/jsQiFkoveH One-time donation: https://t.co/eNwj76xa7a
Volodymyr Zelenskyy /.. @ZelenskyyUa
7.4M Followers 1 Following President of Ukraine / Президент України
Perri Adams @perribus
6K Followers 998 Following @DARPA — https://t.co/YcNwJRDMH6 #AIxCC | Prev @DEFCON CTF | @RPISEC Alumna | Opinions my own
Chris Bing @Bing_Chris
35K Followers 10K Following @Reuters reporter. Covers hacking + foreign affairs. @SAISHopkins student.📧: [email protected] I☎️Signal: 2O2-51O-O174. More contact info: https://t.co/FnTdrahhi0
Lily Hay Newman @lilyhnewman
13K Followers 3K Following Security reporter @WIRED. she/her/my man. Well of course, everything looks bad if you remember it. Signal +1 (347) 722-1347 @[email protected]
GovCERT.ch @GovCERT_CH
15K Followers 22 Following National Cyber Security Centre (NCSC), Computer Security Incident Response Team of the Swiss Government (https://t.co/S9JncbbeYk)
Sarah Andersen @SarahCAndersen
936K Followers 2K Following Author of Sarah's Scribbles, FANGS, and Cryptid Club she/her No NFTs 🚫 Inquiries: [email protected]
DB Cargo @DB_Cargo
41K Followers 207 Following Offizieller Account von denen, wegen denen du so lange an der Bahnschranke stehst. 🚂📦
Man Yue Mo @mmolgtm
5K Followers 79 Following Security researcher at GitHub Security Lab. Tweets/views/opinions are my own.
Herbert Diess @Herbert_Diess
47K Followers 88 Following On a mission to shape new mobility and stop climate change.
Alexandru Niculae @_aniculae
878 Followers 697 Following Software Engineer @reya_xyz Previously @Cambridge_CL and @Google Project Zero
Sophie Garbe @die_gabe
6K Followers 1K Following Redakteurin im Hauptstadtbüro @derspiegel, ausgebildet @djsde
James Hoffmann @jimseven
126K Followers 533 Following Square Mile Coffee Roasters / Youtuber / Author / (sorry, but no recommendations via @ or DM)
Manfred Paul @_manfp
5K Followers 279 Following Maths and cyber and stuff. Playing CTFs with @redrocket_ctf (and @Sauercl0ud). Pwn2Own Vancouver 2020..=2022, 2024. @[email protected]
phakeobj @phakeobj
454 Followers 289 Following Security Researcher; Vulnerability Research and Exploit Development Mastodon: https://t.co/jUCg3DVAV2
Royal Hansen @royalhansen
5K Followers 1K Following Vice President, Engineering, Google - Privacy, Safety, Security: Posts on InfoSec, Privacy, Data, AI, Counter Abuse and random fun stuff from life in CA
Shu-yu Guo (郭纾宇.. @_shu
2K Followers 460 Following Works on @v8js at @google. TC39 editor. Opinions are my own. he/him
Adrian Taylor @adehohum
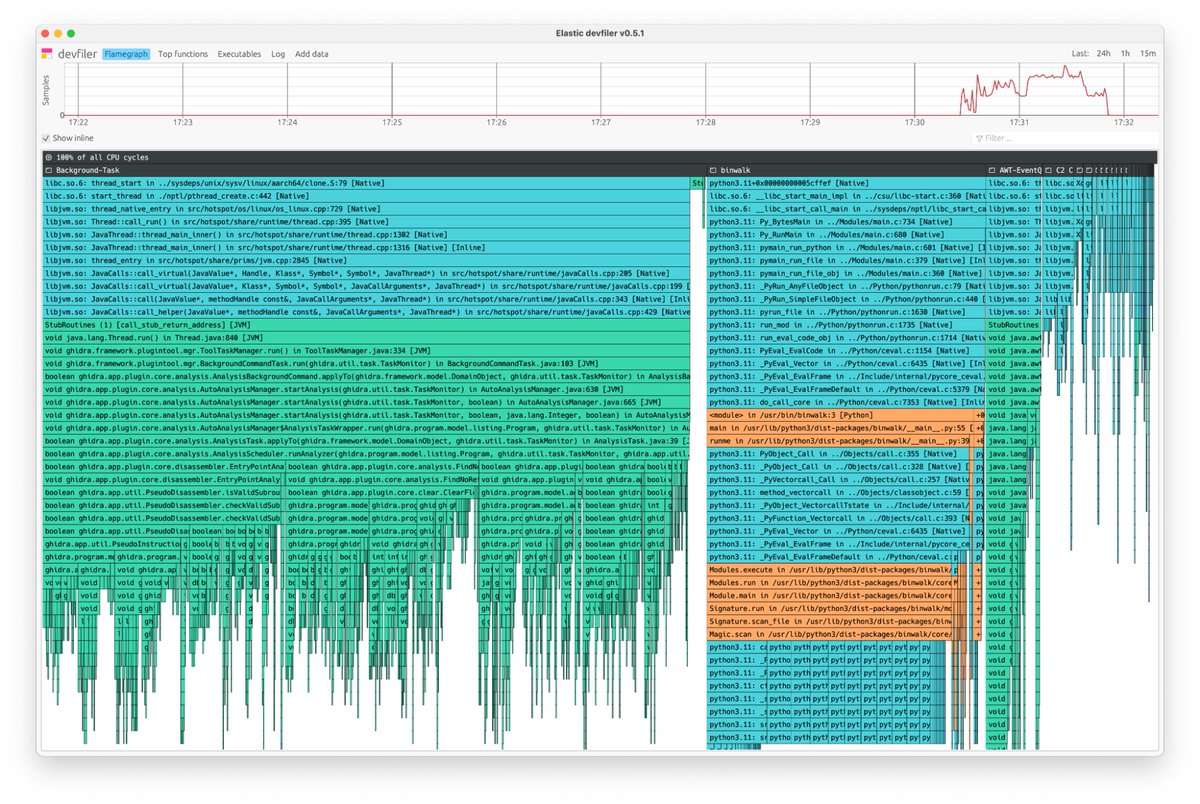
598 Followers 441 Following Chrome security bug wrangler. C++, Python, Rust, kids, mountain biking, snowboarding & climbing. CA & UK. Opinions my own. @[email protected]- Whole system (including kernel) profiling, < 1% CPU overhead - x86-64 and ARM64 - No service restarts or recompilation - C/C++, Rust, Zig, Go, PHP, Python, Ruby, Node, v8, Perl, Hotspot JVM (Java etc) - Works with containerisation (just install on host)
We’re thrilled to announce that the Elastic Universal Profiling agent, a pioneering eBPF-based continuous profiling agent, is now open source under the Apache 2 license! Learn more: go.es.io/3Ul3lw9 #OTel #OpenTelemetry #APM
I just published C isn’t a Hangover; Rust isn’t a Hangover Cure link.medium.com/BfjqLXwQ1Ib
Chrome just got harder to exploit: v8.dev/blog/sandbox Historically, majority of Chrome 0days in-the-wild and in Pwn2Own were based on v8 RCE bugs. v8 sandbox adds a new major level of complexity to the zero day engineering workflow. v8 sandbox bypass bounty program from…
Found a V8 sandbox bypass during @PlaidCTF . Let's see whether I will be the first one claiming the bounty 👀
The V8 Sandbox is now in scope for Chrome VRP for bypass submissions, meeting specific criteria, with rewards up to $5,000! Please see the Chrome VRP rules [g.co/chrome/vrp/#v8…] for full submission criteria and eligibility details.
Blasting Past Webp by @i41nbeer offensivecon.org/speakers/2024/…
🛡️ Google adds V8 Sandbox to Chrome, designed to combat memory corruption issues within its JavaScript engine—addressing the root cause of many zero-day exploits. Read details here: thehackernews.com/2024/04/google… #technews #cybersecurity #hacking
@buptdsb Perhaps the next step for us is to take a look at the V8 sandbox. Thank you for your analysis :)
"A way to detect "sandbox violations": V8 provides a "sandbox testing" mode which installs a signal handler that determines if a signal such as SIGSEGV represents a violation of the sandbox's security guarantees. " - @5aelo source.chromium.org/chromium/chrom…
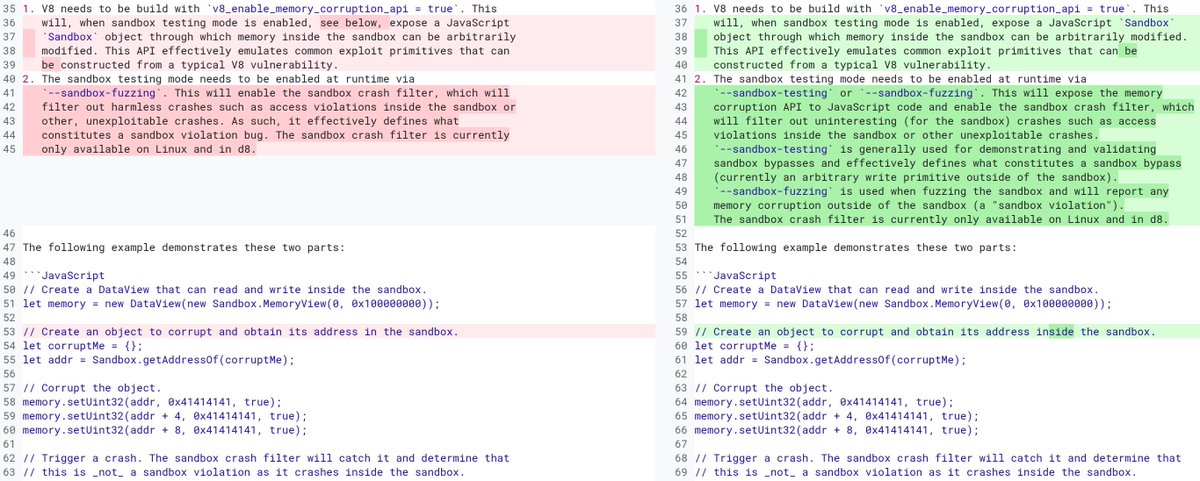
[12878][sandbox] Introduce the sandbox testing mode. It is used specifically for demonstrating and validating sandbox bypasses. chromium-review.googlesource.com/c/v8/v8/+/5412…
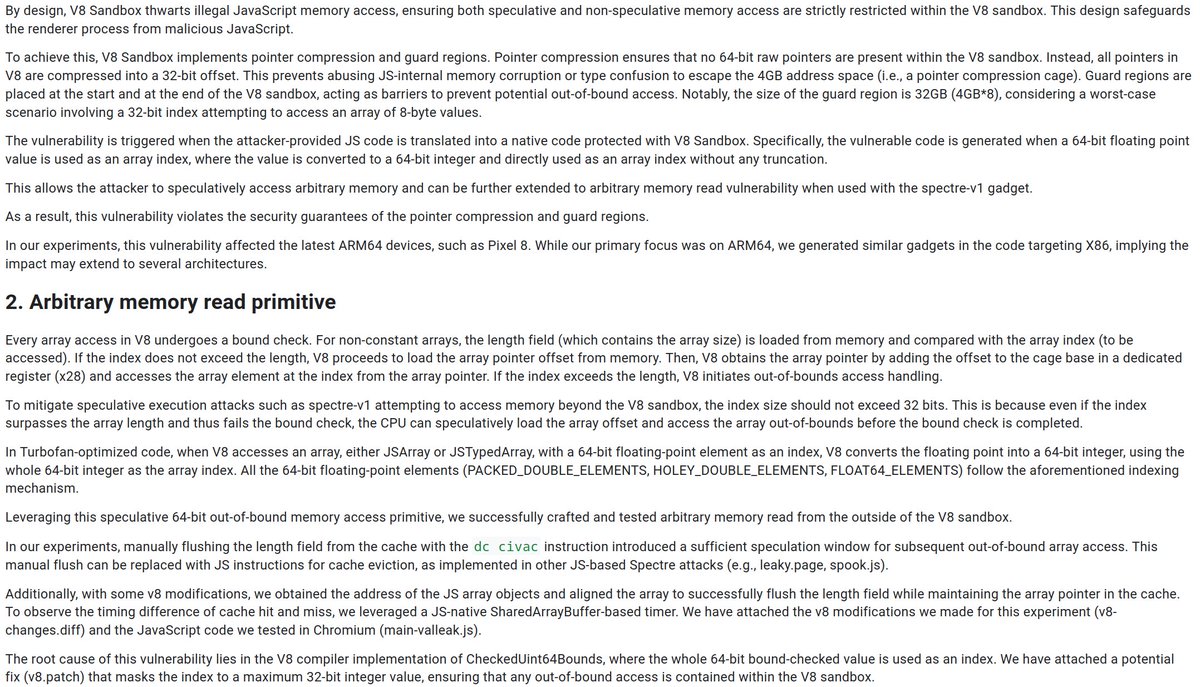
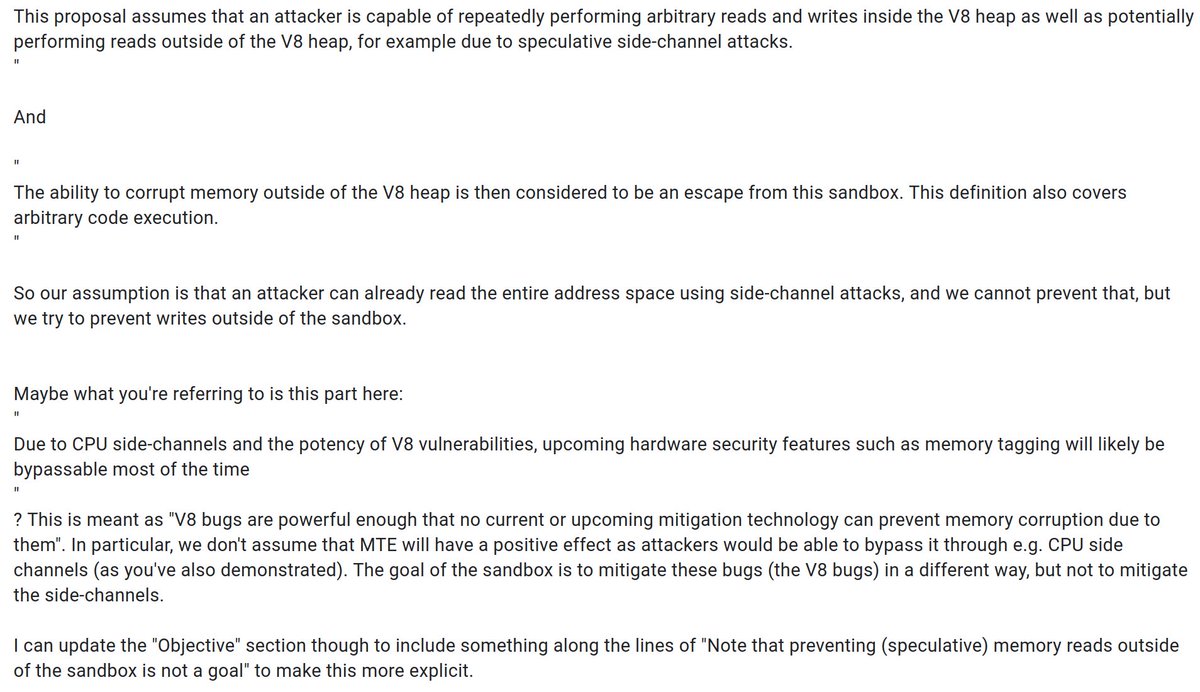
[1511448]V8 Spectre-v1 Vulnerability in V8-optimized code that allows speculative memory access to arbitrary 64-bit memory addresses, which bypasses the V8 Sandbox. issuetracker.google.com/issues/41484034 @5aelo Juhee Kim Youngjoo Lee
🔒We've been working on a custom in-process sandbox for V8. Find out more about the motivation behind this project and its goals in our new blog post: v8.dev/blog/sandbox
After 6.5 year, today was my last day at Google. What a chapter it's been. From Android Security to Project Zero to TAG, I've had opportunities to tackle technically challenging and meaningful projects & work with the best people along the way.
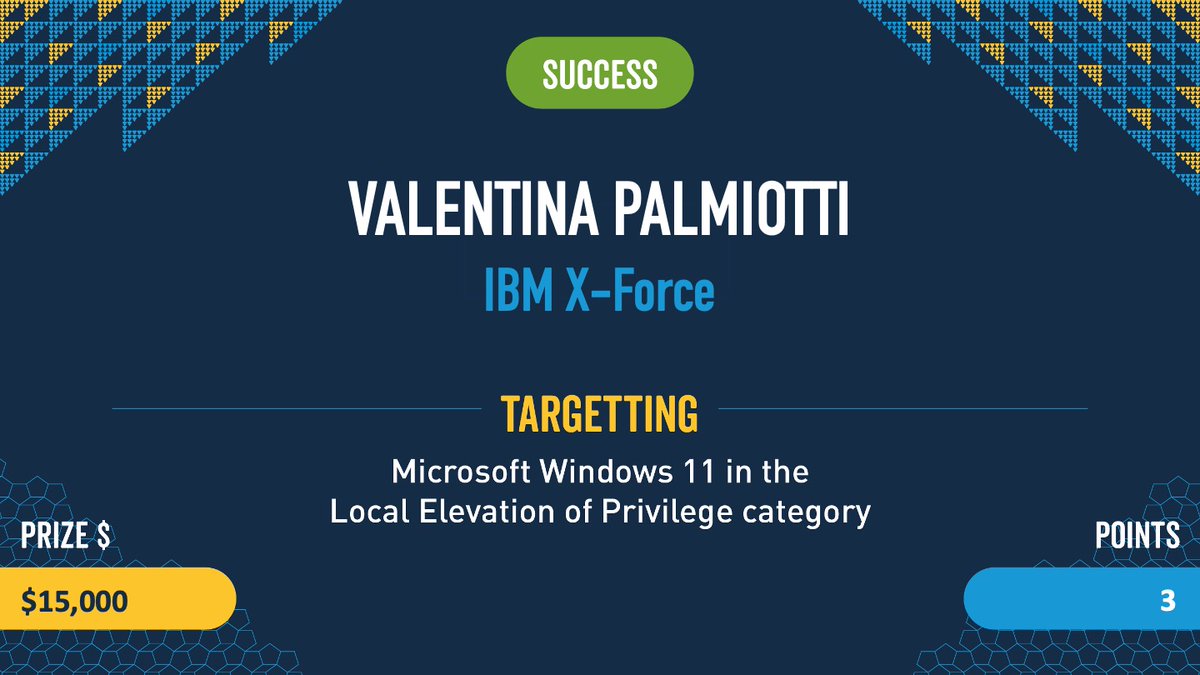
Wow!! Thank you ALL for so much support on my first #Pwn2Own win!! I’m very lucky to have a team and leadership that believes in me. I’m really proud of this bug; this is one of hardest exploits I’ve ever written. I can’t wait to share the details with you once it’s patched!
Confirmed! Valentina Palmiotti (@chompie1337) with IBM X-Force used an Improper Update of Reference Count bug to escalate privileges on Windows 11. She nailed her first #Pwn2Own event and walks away with $15,000 and 3 Master of Pwn points.
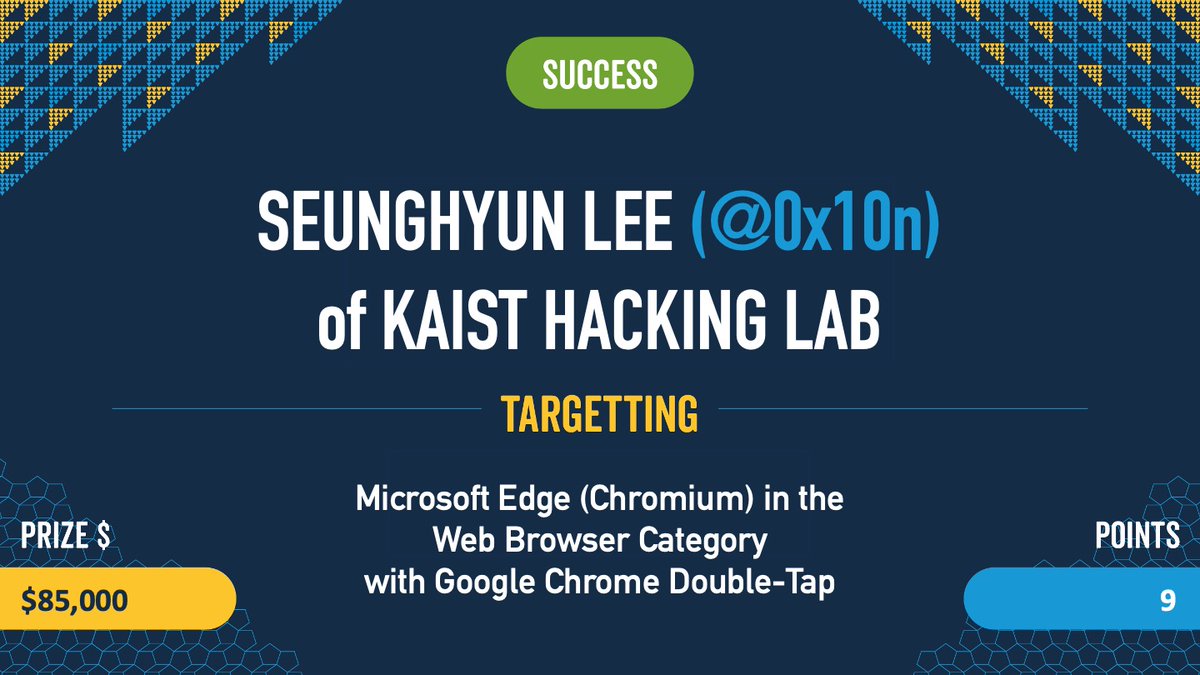
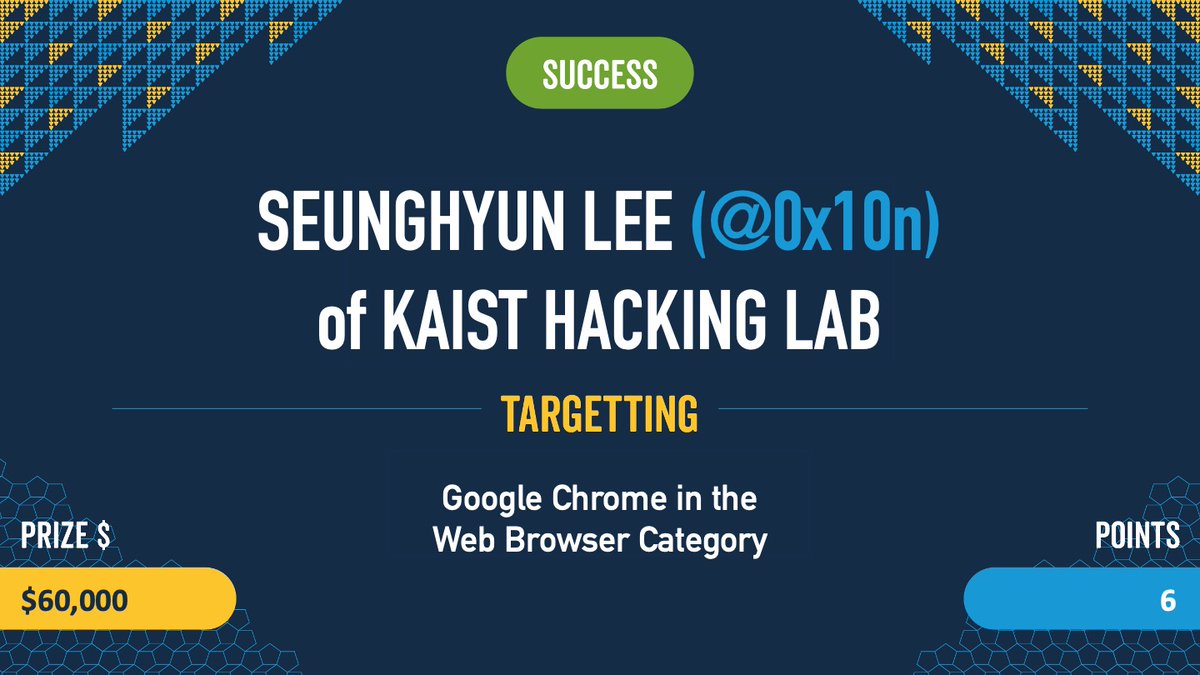
Amazing! Manfred Paul (@_manfp) successfully executed his double tap attack. He used one exploit to to pop both #Google #Chrome and #Microsoft Edge (Chromium). He's off to the disclosure room with both vendors to disclose the details. #Pwn2Own #P2OVancouver
Got a horrible draw for the upcoming #Pwn2Own, but still super excited to be competing for the first time. It’s always been a goal of mine ☺️
Really interesting examples where the compiler might actually *introduce* a security flaw (via a complicated UB). When patched in source code, the optimizing compiler might potentially *reintroduce* that security flaw. github.com/v8/v8/commit/c…
@5aelo @jduck @farazsth98 @adhsec @silviocesare @mboehme_ This patch is interesting - the compiler could also just decide to remove the UNREACHABLE() macro as unreachable dead code, changing nothing at all in the binary - so you are definitely already relying on the compiler implementation for safety, and not just the guarantees of C++