Bràhim Ayadhi @B1froSst
Cyber Security Engineer & Pentester @Randorisec | OSEP | OSCP | CRTO 127.0.0.1 Joined October 2019-
Tweets98
-
Followers138
-
Following316
-
Likes605
Modern implant design: position independent malware development. A small blog post on how to design "modern" malware with features like global variables, raw strings, and compile-time hashing. 5pider.net/blog/2024/01/2… Repo: github.com/Cracked5pider/…
We have @_Aleknight_ on stage at #BlackAlps to present how he found two 0days in the Linux kernel using variant analysis!
Nous étions à @passthesaltcon la semaine dernière. Voici notre retour sur quelques présentations: randorisec.fr/passthesalt-20… #pts22
Hajime! We are glad to announce our second ring0 sponsor! 🙏 Thank you @RandoriSec for helping us to gather the infosec community in Paris ⛩️ To find out more about RandoriSec, visit their website at randorisec.fr #HEXACON2022
A write-up of my research into the Office VSTO format. You can build single document files that download and run .NET assemblies from the internet. 😱😱😱medium.com/@airlockdigita…
Two weeks ago we were at @1ns0mn1h4ck for #INS22 and it was a blast! Here is our write-up: randorisec.fr/conference-ins…
Mobile Hacking training by @Guillaume_Lopes and @ddouhine (March 21st to 23rd) @1ns0mn1h4ck 🇨🇭 **Last chance to register** 100% hands-on (featuring @CorelliumHQ) to learn how to assess the security of Android and iOS mobile apps #mobilesecurity #INS22 #INSO22
Congratulations to the 12 new hackers who just joined our community through @hackthebox_eu ! 🔥 Welcome to @a1woareS @lollonsts @Avik_Saikat PenTest42 c0dbat @LikhithCv @d3tonator @th3cyb3rc0p @HackerGautam @sagaryadav8742 @tkalahan @TrGFxX #bugbounty #crowdsourcedsecurity
We would like to wish you a happy new year 2022! randorisec.fr/fr/2022/ Stay safe !
We're pleased to announce that our first public "Mobile Hacking" training for 2022 will occur in Geneva (March 21st to 23rd) 😎🇨🇭
We're pleased to announce that our first public "Mobile Hacking" training for 2022 will occur in Geneva (March 21st to 23rd) 😎🇨🇭
After this can we all just stop using Java?
Exploiting NFS server via SSRF #HITCON CTF 2021 Metamon-Verse Writeup r0.haxors.org/posts?id=27
Is it just me, or have search results become absolute garbage for basically every site? It's nearly impossible to discover useful information these days (outside the ArchWiki).
Et voici le write-up de Brendan sur l'épreuve Troll Game (PNG Analyzer) du CTF de la @sth4ck randorisec.fr/conference-sth…
La semaine dernière nous étions présents à Bordeaux pour la @sth4ck ! Voici notre retour sur la conférence: randorisec.fr/conference-sth… Demain suivra un write-up sur une épreuve du CTF.
So now we are in 2021 and everyone is using LAPS (cough cough), it is time for CrackMapExec to level up the game. I've added a new core function "--laps", so if you have compromised an account that can read LAPS pass, you can conquer the world now 🔥 Pushed on @porchetta_ind 🪂

? @0xdeadh
55 Followers 317 Following
Rohit Bhatt @RohitBh64724268
36 Followers 808 Following
Rebecca Harris @RebeccaH91376
151 Followers 3K Following
Eva @eva25shrader
147 Followers 3K Following
Brenda @brenda_furbee
445 Followers 3K Following
nourchene @Nourchene28
2 Followers 67 Following
Souheyla Saafi @SouheilaSa27221
15 Followers 35 Following Made in Tunisia 🇹🇳 Software Engineer ~ Jerusalem is the eternal capital of Palestine 🇵🇸
Amel KHAMOUM @mel337__
81 Followers 284 Following Security Researcher Apprentice @Randorisec | Cybersecurity student at University of Paris | Computer Science Engineer | GitHub Campus Expert
Mehdi Talbi 🇵🇸 @abu_y0ussef
3K Followers 407 Following
MH @MorpheusH3x
653 Followers 5K Following Co-founder @securinsa & student @ ESNA • CTF @ret2school_fr • „Call My Leg Does Not Exist“ - RFC 2543 • @[email protected] #VForVictory #FreeAssange
Animesh Phukon @PhukonAnimesh
11 Followers 126 Following
RET2 WarGames @ret2wargames
1K Followers 2K Following Our industry-leading platform is the most effective solution for learning modern binary exploitation through a world-class curriculum developed by @RET2Systems
Fekher Nouioui @FekherNouioui
7 Followers 197 Following
nemjojo @nemjojo
65 Followers 1K Following
Syrine Sfar @SyrineSfar
13 Followers 121 Following
fir3cr4ckers @YBK_FireLights
83 Followers 284 Following Cloud/Web2-3 sec guy, Hacker, SE Student, a Bookworm, Art enjoyer, A computer guru with an artistic mind and CTF player with @SOter14Team 🧨🚀
mida0ui & adm @admida0ui
194 Followers 3K Following Hey! It's Adam & Rania · Cloud & Network Engineering Working Students @INSAT · CTFs @SOter14Team @Securinets
cryptosec @secucrypt
303 Followers 284 Following Infosec | https://t.co/r0fAwDJLfy l I do not post anymore here: Mastodon @[email protected]
Mohamed Rafraf | Raf�.. @Med_Rafraf
15 Followers 52 Following CTF Player @SOter14Team. DFIR . Kubernetes Geek
me2nuk @me2nuk
229 Followers 750 Following Korea University Sejong Campus, CTF Web Player, KITRI BOB 11th, @TeamH4C
Ayadi Mohamed @Ayadinou_
40 Followers 366 Following I am Ayadi Mohamed, 21 years old, i am studying computer networking and telecommunications at INSAT.
Nabil Ben Salah @NabilBe27242883
31 Followers 344 Following
Cccccc Dddddd @CcccccDddddd
11 Followers 110 Following
Nour Mami @NourEhoudaMami
5 Followers 71 Following
Cyril Katz @Cyril_Kz
59 Followers 165 Following
iA @Alex_Boeker
299 Followers 5K Following
red0xff @red0xff
461 Followers 634 Following Vulnerability research at @apple Open Source / Offensive Security
mimaqa @mimaqa1
3 Followers 86 Following
Khouloud Ghazouani @KhouloudGhazou6
10 Followers 51 Following
SinghK @SinghK76863455
12 Followers 359 Following
zhouyuan24 @20945631
54 Followers 1K Following
Jawher @djoinvests
36 Followers 177 Following Digital Assets Trading & Investing Cyber Security enthusiast Director Wannabe
Richard S Moreland @RichardSMorela1
445 Followers 5K Following My father was Richard Wilbur Moreland. I want to share my experience with abuse spanning through my life and give back to the less fortunate people who matter .
joker @joker247696
11 Followers 653 Following
jav0 @javobernardo
878 Followers 2K Following Hacker | Information Security Analyst | Pentester | Bug Bounty Hunter | Cybersecurity researcher | @BugBountyArg
jambon69 @jamb0n69
359 Followers 224 Following CTF newb, pwning with @Beers4Flags. Starcraft is life #rtfm
B:\a.zza @mcbazza
3K Followers 2K Following I.T. geek. Does things with computers/tech. All views are own. Don't take seriously. Or, should you? Servant to ̷5̷ 4x cats. He/him @[email protected]
Manfred Paul @_manfp
5K Followers 279 Following Maths and cyber and stuff. Playing CTFs with @redrocket_ctf (and @Sauercl0ud). Pwn2Own Vancouver 2020..=2022, 2024. @[email protected]
The DFIR Report @TheDFIRReport
53K Followers 0 Following Real Intrusions by Real Attackers, the Truth Behind the Intrusion. Services: https://t.co/XW613EKt2w
Octoberfest7 @Octoberfest73
4K Followers 150 Following Red Team | Offensive Tool Dev | Malware Dev | OSCP | OSEP | RTJC
spencer @techspence
6K Followers 2K Following hacker | pentester | ethical threat | wiz bang exploit slinger hiding in the shadows | co-host @cyberthreatpov | offsec @securit360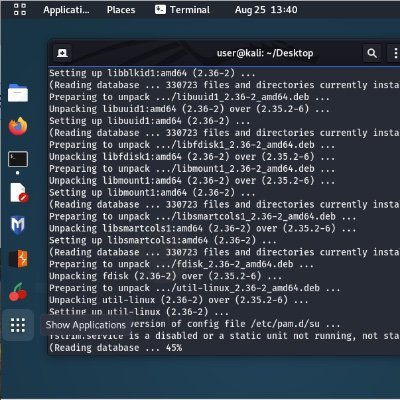
assume_breach @assume_breach
4K Followers 137 Following Why yall have so many calculators in your screenshots? | QAnon Red Team | Labeled Misinformation Propagandist
Bipin Jitiya @win3zz
7K Followers 139 Following Founder of @Cuberks. Maker, hacker, security researcher. Love nature and psithurism. Tweets mostly about hacking, tech, entrepreneurship, and other geeky stuff.
Souheyla Saafi @SouheilaSa27221
15 Followers 35 Following Made in Tunisia 🇹🇳 Software Engineer ~ Jerusalem is the eternal capital of Palestine 🇵🇸
The Spectator Index @spectatorindex
2.8M Followers 0 Following News, media and data from around the globe. Covering politics, economics, science, tech and sport.
Insaf 🍉 @inthesaf
5K Followers 1K Following med student doing research @UCLouvain_be , climate activist/negotiator @unfccc, wannabe artist, and casual shitposter // IG: @insaf_draws
Armchair Warlord @ArmchairW
99K Followers 1K Following Weaboo, author and battle theorist. Interactions are not endorsements.
OSINTdefender @sentdefender
1.1M Followers 798 Following Open Source Intelligence Monitor focused on Europe and Conflicts across the World. RT ≠ Endorsement. Want to Support my Work? https://t.co/PcUbewvWPr
War Monitor @WarMonitors
1.0M Followers 96 Following Proud Semite || Breaking News || Geopolitics || Backup: @WarfareBackup || Want to support me? Donate: https://t.co/CkqsdOqqhV || Twitch: warmonitor
War Mapper @War_Mapper
375K Followers 239 Following Map updates for the war in Ukraine with occasional updates for other conflicts. https://t.co/JS7686HyV9
Bassem Youssef @Byoussef
11.7M Followers 665 Following political satirist,vegan,documentary :tickling Giants,book: revolution for dummies instagram: https://t.co/mtJB6E7ZZb official facebook below
Iceman @herrmann1001
8K Followers 1K Following RFID hacking, Proxmark, NFC & EMV | Magic moon beans | Four spaces instead of Tab | https://t.co/A6rzUPpPs6
Jelyfish @JelyfishTN
11K Followers 510 Following -Gaming Influencer -Talent/Caster at Riot games MENA #Bitcoin
Amel KHAMOUM @mel337__
81 Followers 284 Following Security Researcher Apprentice @Randorisec | Cybersecurity student at University of Paris | Computer Science Engineer | GitHub Campus Expert
(╯°□°)╯︵ S�.. @cybersecstu
30K Followers 4K Following Head of Attack & Respond | ❤️OSINT |✍️ CTI & Analytics book ~2024, Tracelabs Black badge x3 | Ex- @themanyhatsclub | #cyber Views my own not employers
Simon Scannell @scannell_simon
3K Followers 481 Following Cloud Vulnerability Research @ google. Opinions are my own
LuemmelSec @theluemmel
6K Followers 486 Following I speak BloodHound. Husband, Father, IT-Guy, Security-Noob Blog: https://t.co/PXB35KEqs6 GitHub: https://t.co/Unp9jZOpBn
Justin Gardner @Rhynorater
27K Followers 2K Following Christian | Full-time Bug Bounty Hunter | Host of @ctbbpodcast | Advisor @CaidoIO | 2x HackerOne MVH | 🗣️ English, 日本語 | ♥️ @mariahchan_ ♥️
Sam Curry @samwcyo
77K Followers 949 Following Hacker, bug bounty hunter. Run a blog to better explain web application security.
Piotr Bazydło @chudyPB
3K Followers 257 Following Vulnerability Researcher at the Zero Day Initiative | Pwn2Own Miami 2022 | Microsoft MVR
Maddie Stone @maddiestone
64K Followers 847 Following Security Researcher - Google's Threat Analysis Group | 0days all day. Love all things bytes, assembly, and glitter. she/her.
Citizen Lab @citizenlab
122K Followers 1K Following Research & development at the intersection of cyberspace, global security & human rights. Munk School of Global Affairs & Public Policy, University of Toronto
Munich Cyber Tactics,.. @MCTTP_Con
317 Followers 3 Following 2nd edition of our awesome con will happen, save the date 17-19th of september 2024 #mcttp
Beau Bullock @dafthack
17K Followers 682 Following Hacker, trainer, and guitarist | Black Hills InfoSec #RedTeam | @BreakForge Training | Produces music to hack to at @N0BANDW1DTH
PortSwigger Research @PortSwiggerRes
88K Followers 7 Following Web security research from the team at @PortSwigger
SpecterOps 🇺🇦 @SpecterOps
36K Followers 378 Following Know Your Adversary - Adversary Simulation | Detection | Resilience
The Office Frames @office_frames
2K Followers 556 Following I post 1 frame from 1fps episodes of The Office every 30 mins. Parody account. No affiliation with NBC. You can watch the show on official streaming services.
Dirk-jan @_dirkjan
25K Followers 173 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
Zero Day Initiative @thezdi
77K Followers 17 Following Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities.
Forgette Benoît @Mad5quirrel
139 Followers 103 Following
publiclyDisclosed @disclosedh1
56K Followers 2 Following This is an unofficial HackerOne public disclosure watcher who keeps you up to date about the recently disclosed bugs. By @NOBBD
Matt Hand @matterpreter
9K Followers 290 Following Director, Security Research @preludeorg 💜 | Author of Evading EDR https://t.co/E5fs0sSTOv 📖 | Adversary tradecraft & windows internals 🦠
Issam Rabhi @Issam_Rabhi
3K Followers 1K Following Phd in Computer Science. Acknowledged by Google more than 100 times!
vdehors @vdehors
980 Followers 228 Following
Jazz Fall @JazzFall
129K Followers 2K Following
Vincent Le Toux (Pari.. @mysmartlogon
11K Followers 56 Following Author of #PingCastle, contributor to #mimikatz (DCSync, setntlm, DCShadow) and #OpenSC. Wrote GIDS applet, OpenPGP card driver on Windows and OpenSC stuff.
🥝🏳️🌈 Be.. @gentilkiwi
62K Followers 278 Following A kiwi coding mimikatz & kekeo github: https://t.co/eS3LVgU6i0 Head of security services @banquedefrance Tweets are my own and not the views of my employer
terjanq @terjanq
9K Followers 224 Following security enthusiast that loves hunting for bugs in the wild. co-founder and player of @justCatTheFish. infosec at @google. opinions are mine."Hello: I'm your Domain Administrator and I want to authenticate against you". My #SilverPotato is out, check the blog post: decoder.cloud/2024/04/24/hel… 😃
Nice work! Much more comfortable than my old implementation 🙌 github.com/nbaertsch/nimv…
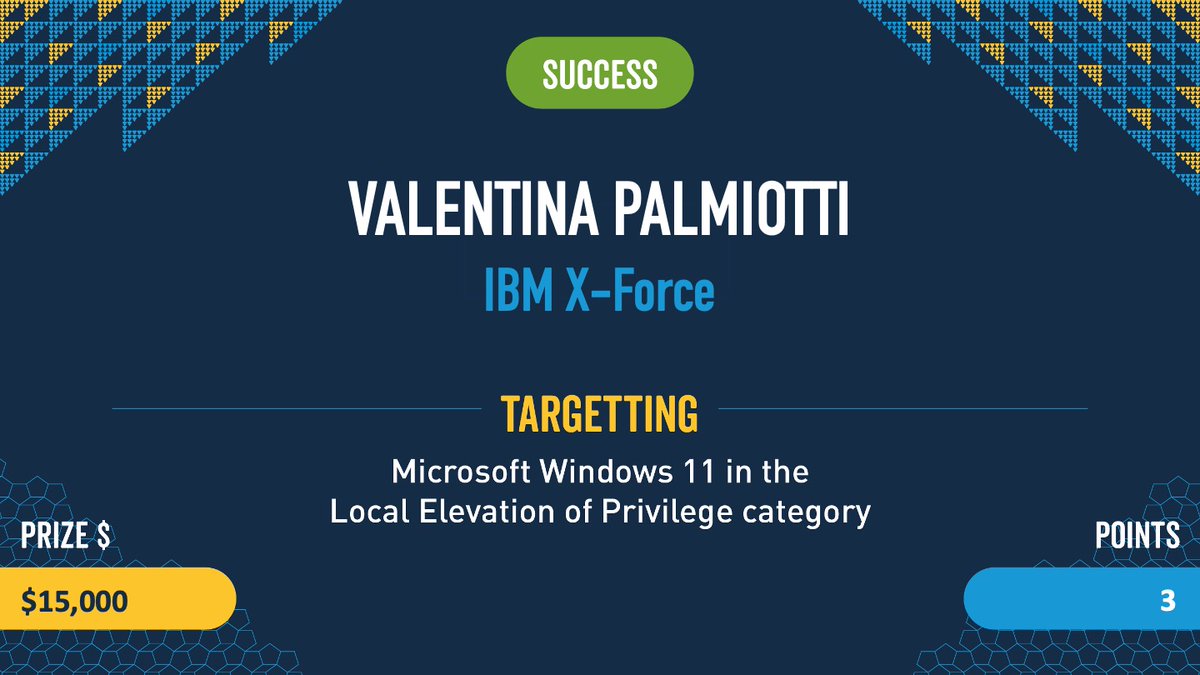
Confirmed! Valentina Palmiotti (@chompie1337) with IBM X-Force used an Improper Update of Reference Count bug to escalate privileges on Windows 11. She nailed her first #Pwn2Own event and walks away with $15,000 and 3 Master of Pwn points.
Most impressive! The ninjas from @Synacktiv needed less that 30 seconds to demonstrate their exploit on the Tesla ECU with Vehicle (VEH) CAN BUS Control. The attempt was done in an RF enclosure to ensure no passers by were impacted. #Pwn2Own
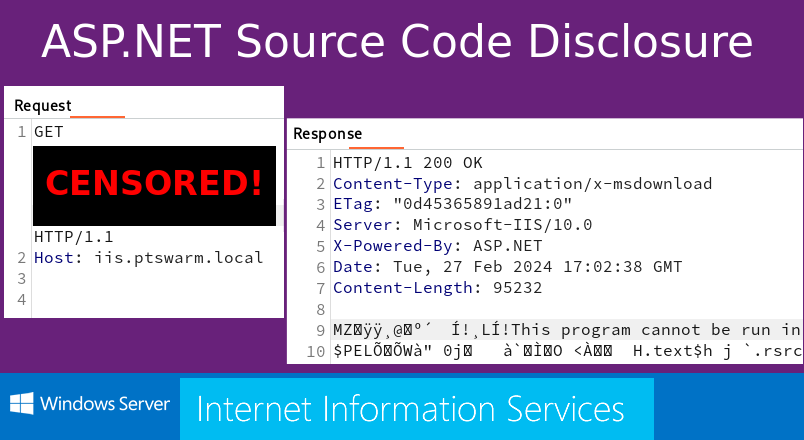
🎁 Source Code Disclosure in IIS 10.0! Almost. There is a method to reveal the source code of some .NET apps. Here's how it works. 👉 swarm.ptsecurity.com/source-code-di…
#PingCastle 3.2 released !!! pingcastle.com/download/ Active Directory & AzureAD security health check in seconds >200k AD audited, management readable, no install, no admin, no data sent "to a cloud" Example of report: pingcastle.com/PingCastleFile… github: github.com/vletoux/pingca…
@acole76 I’m talking about pentest reports. You seem to be talking about vulnerability assessment. When you deliver your pentest report, giving them findings that don’t demonstrate risk doesn’t motivate them to fix it. Or worse, they want to fix it but can’t get the executives to fund it…
My take on "I'm not a pentester (and you might not want to be one either)": Edited to add: Don't get into this line of work unless you're really passionate about it and willing to outwork the masses to keep learning and excel. TLDR: There is no shortage of supply of desperate…
Has a red teamer or pen tester requested that you refrain from uploading their implant to VirusTotal? How did you respond? If not, how would you respond?
Modern implant design: position independent malware development. A small blog post on how to design "modern" malware with features like global variables, raw strings, and compile-time hashing. 5pider.net/blog/2024/01/2… Repo: github.com/Cracked5pider/…
@assume_breach @geeknik You made a lot of valid points. You’ll find the exact same issues in any profession because of companies putting profit over treating employees well. It’s human nature and profit margins.
I'm exited to release GraphStrike, a project I completed during my internship at @RedSiege. Route all of your Cobalt Strike HTTPS traffic through graph.microsoft.com. Tool: github.com/RedSiege/Graph… Dev blog: redsiege.com/blog/2024/01/g… #redteam #infosec #Malware #Microsoft
It's nice to have my .NET deserialization research nominated to that list. It made my day:)
Voting is now live for the Top ten web hacking techniques of 2023! Make a brew, browse the nominations, and cast a vote for your personal top ten here: portswigger.net/polls/top-10-w…
Only a few days until #Pwn2Own Automotive in Tokyo. Our ninjas will bring some interesting entries with them ;)
We unveil scnr (prononce "scanner") a tool coded in Rust that eases the process of working with heterogenous files. You can use it to parse, convert and query the content of files. It's used at the core of Shindan to process iOS sysdiagnose archives. github.com/shindan-io/scnr
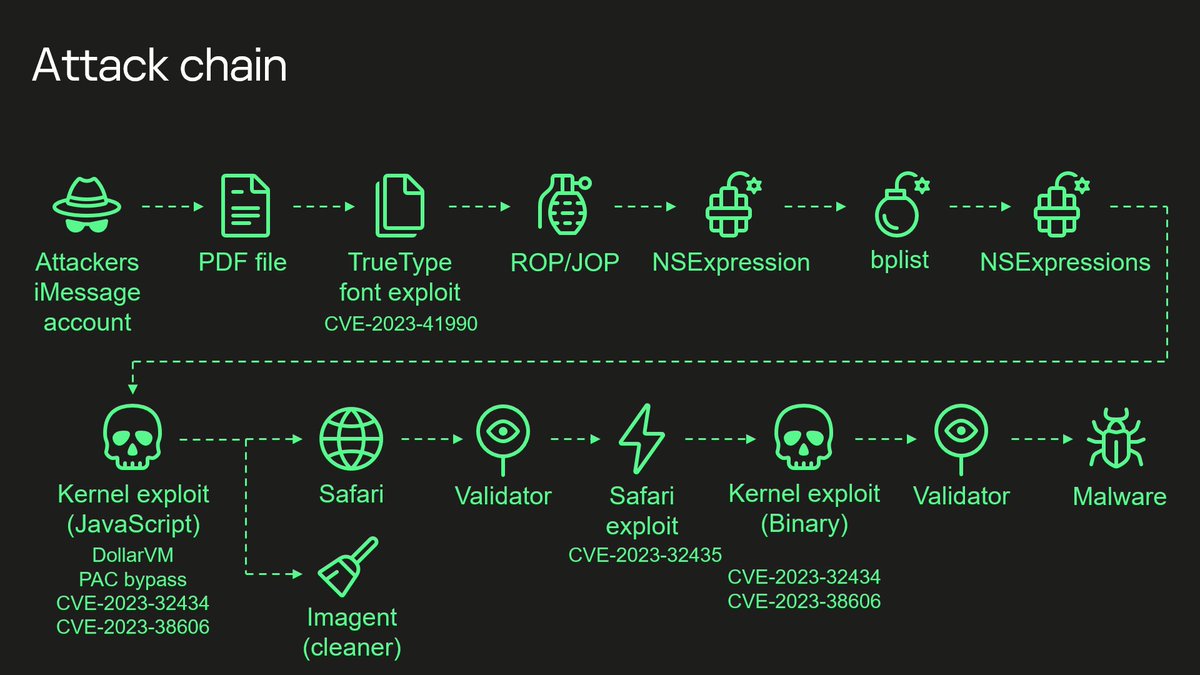
As a former NSA guy, watching the community reverse engineer this exploit makes me think of all the people who developed it sitting and crying somewhere as it’s secrets are spilled.
Hector Martin (marcan) has some good ideas that the iMessage exploit used dbgwrap and cache debugging registers. He also talks about how the "sbox" design is very clearly an ECC or CRC and not intended to obfuscate anything. social.treehouse.systems/@marcan/111655…
Hector Martin (marcan) has some good ideas that the iMessage exploit used dbgwrap and cache debugging registers. He also talks about how the "sbox" design is very clearly an ECC or CRC and not intended to obfuscate anything. social.treehouse.systems/@marcan/111655…
This Mastodon post by Hector Martin talks about some ideas about the hardware feature that was used: social.treehouse.systems/@marcan/111655…
The fact that they developed a complete zero-click to kernel chain, JUST to then force the device to open a web page to trigger the "real" chain, is the most bureaucratic exploit I can imagine 🙈 koeln.ftp.media.ccc.de/congress/2023/…