CyberPatron © @CyberPatronMC
Welcome to CyberPatron. Your #1 cybersecurity community X account and aside being the best, we want you to be the best. For our services, DM @cyberpatronsrvc 127.0.0.1 Joined March 2019-
Tweets4K
-
Followers27K
-
Following22
-
Likes5K
Welcome to May!!!! From all of us at CyberPatron Network we say welcome to MAY. Password Protection Day is just a day away. Let's endeavor to change our passwords and stay cyber-safe.
10 Notorious types of computer virus
Which of the following encryption algorithms is considered the most secure and widely used for securing internet communications? A. DES (Data Encryption Standard). B. AES (Advanced Encryption Standard). C. RSA (Rivest-Shamir-Adleman). D. MD5 (Message Digest Algorithm 5).
What specific data field in a certificate identifies the entity associated with the public key contained in the certificate? A. Certificate signing request (CSR) B. Intermediate CA C. CN (Common Name) D. Certificate revocation list (CRL)
A network admin is establishing secure communication channels over the internet. What cryptographic protocol suite provides authentication, integrity, and confidentiality for VPN connections, including site-to-site connections? A. SSL/TLS B. IPSec C. Network-based Intrusion…
Which type of System and Organization Controls (SOC) report is based on the design and suitability of controls at a specific point in time? A. SSAE SOC 1 Type I B SSAE SOC 2 Type I C SSAE SOC 1 Type II D SSAE SOC 2 Type II
What type of risk is associated with the potential financial loss due to human errors, fraud, or intentional sabotage within an organization? a. Compliance risk B. Human error risk C. Operational risk D. Financial risk
Hey Hackers 👋 Bookmark & share this Practical Cyber Security Resource! - Web Pentest 📝 - Mobile Pentest 📝 - Cloud Security & Pentest 📝 - Bug Bounty 📝 - OSINT & Google Dorks 📝 - API Security & Pentest 📝 - Active Directory 📝 - Red Teaming 📝 - AppSec & Code Review 📝 -…
Best Laptop for Cybersecurity student and professional ☑️Lenovo ThinkPad X1 Extreme Gen 5 (16, Intel) Laptop - Best Laptop for Cyber Security Professionals ☑️DELL XPS 15 - Best Laptops for Cyber Security Students ☑️Dell Inspiron 15 - Best Budget Laptop for CyberSecurity…
You are configuring a firewall to enhance network security. What is a key consideration when implementing firewall rules? (A) Allow all incoming and outgoing traffic for simplicity. (B) Block all network traffic from external sources. © Create specific rules to allow necessary…
A network administrator is responsible for securing a web server. What is a key consideration when implementing secure communication with HTTPS? (A) Use a self-signed certificate for simplicity. (B) Enable plain HTTP for public-facing content. © Purchase a valid SSL/TLS…
You're conducting a network security assessment and need to identify the actions typically taken during the "Containment" phase of incident response. What are common measures in this phase? (A) Restoring affected systems to their original state, eliminating vulnerabilities (B)…
An organization experiences a data breach, and you're part of the incident response team. What should be a priority during the "Lessons Learned" phase? (A) Implementing additional security measures to prevent future incidents (B) Identifying the intruder and reporting the breach…
Which of the following is an example of a compliance standard relevant to the handling of payment card data? (A) HIPAA (B) PCI DSS © FERPA (D) ISO/IEC 27001
Which regulation is specifically designed to protect the privacy of individuals' personally identifiable information (PII)? (A)GDPR (B)SOX (C)GLBA (D)FERPA
You are configuring a firewall to enhance network security. What is a key consideration when implementing firewall rules? (A) Allow all incoming and outgoing traffic for simplicity. (B) Block all network traffic from external sources. © Create specific rules to allow necessary…
In the context of network architecture, what is the purpose of a demilitarized zone (DMZ)? (A) To host sensitive data and internal applications (B) To isolate internal networks from external networks (c) To provide a buffer zone between the internet and an internal…
What architecture is designed to protect against distributed denial-of-service (DDoS) attacks by routing traffic through a filtering service to scrub malicious traffic before it reaches the target network? (A) DMZ (Demilitarized Zone) (B) Proxy server (C) Intrusion Detection…
MeOw @MeOwPaWns
7 Followers 64 Following LPU'27 | CyberSec Enthusiast | CTF Player ⚔️ | Script Kiddie 👾
Dyad @Mohame542
67 Followers 194 Following
iratefun @iratefun
1 Followers 58 Following We're all going to make it, maybe, kinda, well... maybe.
Touareg @touareglife_69
42 Followers 175 Following
Hunter Johnson @fogjohnson
1K Followers 2K Following Optimist | Motivator | Entrepreneur | 🎈 Master craftman 🏹
Nucleus Incorporated @nucleusgh
2K Followers 5K Following Graphic Designer || Website Designer and Developer || Digital Marketer ||Social Media Manager|| Forex Trader || Investor||Youtuber 🚀 50% discount for startups
Vera Anulika Nwokoye @Vera_Wonder01
1 Followers 6 Following ABBA'S Wonder || Jesus Girl || Customer Care Executive with a difference || I am the Joy of Many generations 🤠
Tracy Brotherton @b0at1ngal
513 Followers 697 Following Remember what should be remembered, and forget what should be forgotten. Alter what is changeable, and accept what is unchangeable
Bash_ The_ Data_Guy @ahmed_bashorun
251 Followers 1K Following I'm a Data scientists, Machine Learning Engineer | Data-Analyst| Quantitative trader
Caribeauti_ @Caribeauti_
2 Followers 18 Following
Kupon Group @GlobalKupon
975 Followers 2K Following |C.E.O KUPON OIL AND GAS LTD| |C.E.O KUPON HOTEL & SUITS |Dealers on oil, gas, LPG| | Business Man| Son of the Soil |
Kezhairs @kelzhairs
3 Followers 27 Following
Nathaniel Davis @Nathani21963974
1 Followers 834 Following
Roman Johnson, Ph.D. @SonoftheDelta
1K Followers 5K Following -Harvard Postdoctoral Fellow, Retweets =\ endorsement. Africana spiritualist. Writer. Scientist. Healer. 1867
HUNT3R @MeetKC2
152 Followers 1K Following #deriv #syntheticindices #v75 #multimillionaire #2024hereIcome #onlyblues
Agianpuye @agianpuye_
5 Followers 50 Following
Mohammed BG @mohboi_
40 Followers 63 Following
Ifeanyi CJ Ijezie @ifeanyispace
307 Followers 990 Following This is not to suggest that TRUTH itself is variable, but that fallible human beings will vary in their knowledge of & proximity to TRUTH.
Jimmy @jimmy_TheWeasel
31 Followers 774 Following
courtneyceira @ccmitchell__
216 Followers 490 Following
Dylan Thompson @DYLANaiFocus
0 Followers 3 Following Les innovations en IA au cœur du Canada moderne.
Kevin Mwenda @Kevoaladeen
5 Followers 100 Following
Nathan @pottsyscontract
68 Followers 117 Following
Tara Blanca @Nisbeth_su
101 Followers 730 Following
SpectreNBA @spectreNBA
4K Followers 3K Following || I Write crime history 🕵️♂️ || I write academic essays & projects on crime-related topics📝 || Freelancer|Football Lover.
Samod @heissamod
26 Followers 369 Following
726Monika @726_monika
98 Followers 996 Following beauty. health. music. me. | IG: @auntieseasonpodcast ||
ERIMUS🧑🚀 @ERROR_540
748 Followers 2K Following PhD IN (I DON'T KNOW)||TECH|| CYBER SECURITY|| SAVAGE|| RT DON'T EQUATE ENDORSEMENTS||
SIGOGO @sislesego
317 Followers 2K Following
mWave Communications @MwaveService
11 Followers 42 Following Your go-to for wireless internet, mobile plans, VPNs, CCTVs, IT support & networking. Connect seamlessly with our digital family. Join us now!
Olatunde Nofiu @tunapy212
36 Followers 92 Following
black◇power◇ @black0009000
0 Followers 6 Following
Nyanyu Elias 🇳🇦 @NyanyuE
20 Followers 216 Following An introvert loving wife and mother, reserved and focused
Danny @DCO_Danny
2K Followers 4K Following Entrepreneur, Consultant, loves humanity, being real to oneself and to others. Advocate of a peaceful society. Be ready to take action for opportunities.
Oluwatosin Oloyede @tosinho14
1K Followers 2K Following Agric. Engineer •Web Developer •Entrepreneur •Trader •FC Barcelona •Messi
OIHEC hackers @HackersOIHEC
43K Followers 7K Following Hacker mexicano - Fundador de OIHEC antes OMHE - #opensoc #latam #speaker #pentester #blueteam #redteam #criptoanarquista #security
Ed Harmoush @ed_pracnet
6K Followers 181 Following I teach Networking and Network Security. Youtube: https://t.co/xat3Kn7BLj Courses: https://t.co/6zN0Y9C95U Blog: https://t.co/r4fmIZ1SJq
Zabihullah Atal @ZabihullahAtal
24K Followers 222 Following Asst. Professor. Researcher, IEEE/Nature/Hindawi Author. I am Writing about AI Tools, Digital Products, and Tech Updates. DM for collaboration.
Dr Iretioluwa Akerele @ireteeh
107K Followers 18K Following PhD| Founder @CybarikGlobal | CyberDOC | Researcher| CyberSecurity Career Mentor| @Cloudrica @cyblackorg| @cybersafehq| ChelseaFC|@PhDSafeSpace |Views are mine
The Hacker News @TheHackersNews
914K Followers 2K Following #1 Most trusted publication for breaking cybersecurity and hacking news, insights, and analysis for information security professionals.
CyberPatronServices @CyberPatronSrvc
1K Followers 21 Following A service branch of @cyberpatronmc. We revamp and build your cv to perfection, we offer cybersecurity consultancy and services. Send us a Dm for inquiries.
Cisco Nerd @OnijeC
15K Followers 7K Following CDA, SA, Wi-Fi , Cloud, Net-DevOps 🫶 Cisco Insider Advocate🏆#CiscoNetacad-Trainer #TechTalkWithaNerd #CTO
TheCyberChef👨�.. @IamTheCyberChef
16K Followers 289 Following Microsoft Azure || Blue Teamer || Threat Detection || DFIR || Researcher || Educator || Dedicated to helping beginners go from ZERO to HERO
Mr. Patrick Essien @CyberSecFalcon
8K Followers 1K Following Passionate about protecting individuals and organizations from cyber attacks. Prioritizing detection to prevent SecBreach. https://t.co/nnhrQIt0Wc
Jeffrey P. @codedjeff
3K Followers 423 Following Follow me if you want to grow... It won't easy tho. Retweets are not necessarily an endorsement. DYOR! LINKS to all my IT Resources Below⬇️
Umar Farouk Farouk @Cyber_GRC
1K Followers 729 Following Aspiring Cybersecurity leader| GRC Analyst| ISMS implementer for critical national infrastructure| Trainer |Anime|Chelseafc ⬇️ https://t.co/CKxqaDCPaq
24 | #AfricaCyberFest @twenty4_io
2K Followers 752 Following #Cybersecurity is life + Community Mngr @diaryofhackers / @cysedhq + Community Lead @gdsc_unilorin + Threat intel + Sec PM + Cybersec Advo + Intern @cyblackorg
CompTIA @CompTIA
66K Followers 1K Following We ❤️ #InformationTechnology & believe in advancing the global #tech workforce through #ITcertification We want to hear YOUR story! Send us a DM!
Security Trybe @SecurityTrybe
161K Followers 106 Following A Platform For Cyber Security| Networking | Tech| Education|IG-https://t.co/iWeuXqOxRk
DsL_a ʚїɞ ® @_DeejustDee
21K Followers 4K Following The Cyber-Tech woman||Founder @cyberpatronmc network|| I’m the next BIG THING ||Tech Influencer| GRC🤍||Emphasis on the God factor. 🔥💥DsL ʚїɞ ♔ ♡
DJ BORSH OF THE BUJ @Dj_borsh
7K Followers 6K Following PRO DJ || Official || Bookings [email protected] weddings || Events || Music promotions (Radio) 08037511961 (apple,spotify,audiomack ) || DM open for busines
Cody African Boy 🍀.. @AdedotunCody
5K Followers 4K Following God’s Own, Philosopher, Music, PanAfrican🖤 🌍 , NFT Creator/Collector, Realtor, Leisure 🚢. Gemini 💎 NFT collection @heritagehubart
Hausa Lawyer @Aboki_Esq
9K Followers 8K Following #MUFC #Abusite LLB: BL: Lawyer: Consultant: Aim high☝☝☝ Know your worth. Don't wish for it, work for it. Justice for all. https://t.co/2nQL4jo9KJ
Reformer_Oluseun @ReformerOluseun
12K Followers 11K Following #Humanity #African #Skeptist #sociologist #RealEstate #SocialCritic #Politics #Religion #NonConformist PLEASE DON'T BELIEVE ME; I QUESTION AND DOUBT ALOT ALSO
Cisco @Cisco
740K Followers 3K Following Official info on Cisco news, events and technology innovation. For help, reach out to @CiscoCommunity or @HeyCisco.Day 45-56/#100daysofCybersecurity During this 11 days, i took to learning python with projects @ireteeh @sisinerdtweets @_DeejustDee @CyberPatronMC @OnijeC @brodaishola_ @RedHatPentester @microbialawyer @CyberSecFalcon @Cyblackorg @_Rega_n @jay_hunts @secfortress
Day 42-45/#100daysofCybersecurity On today episode of learning python, I learnt about Lists @ireteeh @sisinerdtweets @_DeejustDee @CyberPatronMC @OnijeC @brodaishola_ @RedHatPentester @microbialawyer @CyberSecFalcon @Cyblackorg @_Rega_n @jay_hunts
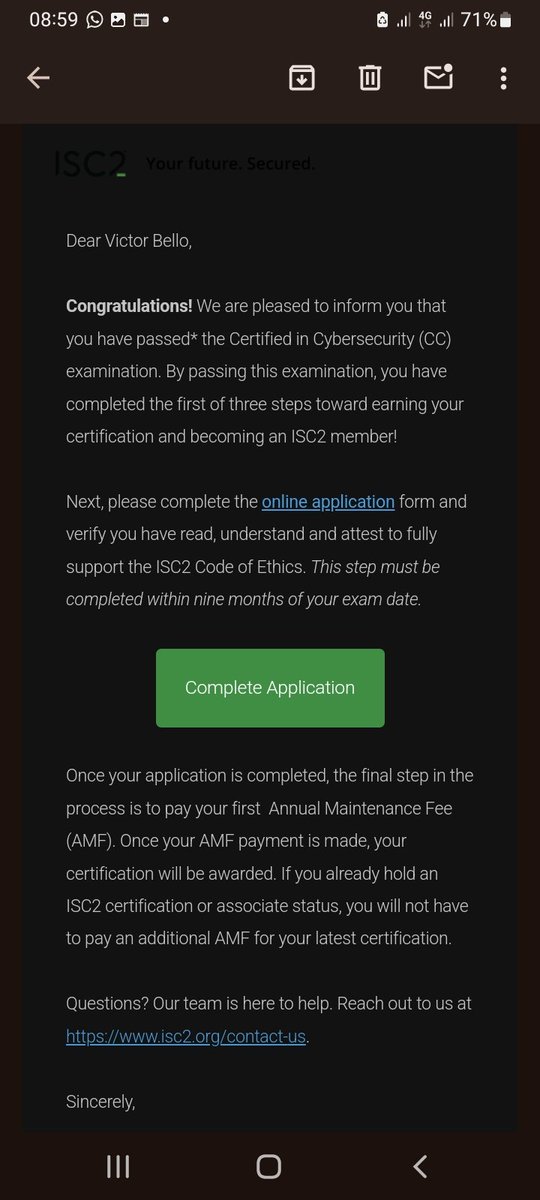
I am happy because I bagged another certificate in Cybersecurity. I am glad I am not just getting the certificates, I am also learning a lot.
April, a month for more milestones. 1. Linux Essentials ✅ 2. Cisco Cyberops Associate ✅ ✅ 3. Home Lab set up ✅ 4. Ingryd Cohort - ongoing 5. Cisco Ethical Hacker - ongoing 6. Google Cybersecurity Certificate - Paused 7. ISC2 CC ✅ ✅ @ireteeh @ernestgfx @akintunero
@Cyblackorg Very loaded & exciting. 1. Linux Essentials ✅ 2. Netacad Cyberops - to be completed this weekend 3. Home Lab set up ✅ 4. Ingryd Cohort - ongoing 5.Ethical hacking with Cyberprowess - ongoing 6. Google Cybersecurity Certificate - on - hold 7. ISC2 CC - Booked for next week
Glad to announce that I have completed another course 🎉🥳. I so much love this particular one because the instructors thoroughly explained the concepts like it's a kidding learning. Now it's time to understand networking fully! I'll be right back!
I am happy because I bagged another certificate in Cybersecurity. I am glad I am not just getting the certificates, I am also learning a lot.
@CyberPatronMC B = PCI DSS ( payment card industry data security standard)
General Data Protection Regulation (GDPR).
Which regulation is specifically designed to protect the privacy of individuals' personally identifiable information (PII)? (A)GDPR (B)SOX (C)GLBA (D)FERPA
Here’s to another week of consistent practice and work. Another week to grind 💪 Another week to push goals. Another week of learning. @Lizettle_ @egheCyber @ireteeh @CyberPatronMC #Grc
Gradually advancing towards my cybersecurity goals. It has been an interesting journey with the help of the accountability class created by @Lizettle_ Bless you 😘 Saving this here. @ISC2 #CyberSecurity #GrcAnalyst
@MJchamus1 @CyberPatronMC Started my team of 7 and am 3 less if interested DM,,,,each person with a role from network engineering, Ethical Hacker,Software Engineering, Machine Learning and AI
@CyberPatronMC How do i learn hacking and programming? i want to be someone's student please help.
Couple who fix their cv together gets discounted on next week offer 😌😌
Today has been so good, woke up to good news and ending it with more good news. Thank God for it all.
I don't know why it should be B...
Which of the following is the primary purpose of using a hash function in cybersecurity? A. To encrypt data B. To verify data integrity C. To compress data D. To authenticate users
Are you a cybersecurity enthusiastic? Do you need mentorship and training? Do you need to revamp your cv? Your answer is right here!! Do well and patronize her🤗 Kindly Retweet. @_DeejustDee @CyberPatronMC
Hi guys, Please does anyone have Comptia security + SY0-501 study guide ? @CyberPatronMC @TheCyberSecHub
Your career summary should be brief: a brief intro about yourself, a bit of notable achievement, tools and what you're looking for in that organization is enough.
If you’re choosing a career in cybersecurity and your focus is GRC, our training is where you start your journey as a GRC professional, we take you from the basics of GRC. Before then be sure to have completed the basics of cybersecurity and still keep learning. Your success in…
@CyberPatronMC @CyberPatronMC @CyberPatronMC @CyberPatronMC @CyberPatronMC @CyberPatronMC
Cybersecurity communities you can look out for: -CyberSafe -Cyblack -Cybarik -CybersecHaven -NexaScale -Virtual Testing foundations Add yours