-
Tweets286
-
Followers5K
-
Following152
-
Likes848
I will be at @GISECGlobal in Dubai on April 23rd+24th to represent @OutflankNL and our parent company @fortraofficial. If you want a private demo of our toolkit for red teams Outflank Security Tooling (OST) and Cobalt Strike then drop me a line or visit our booth at Hall 6/C75.
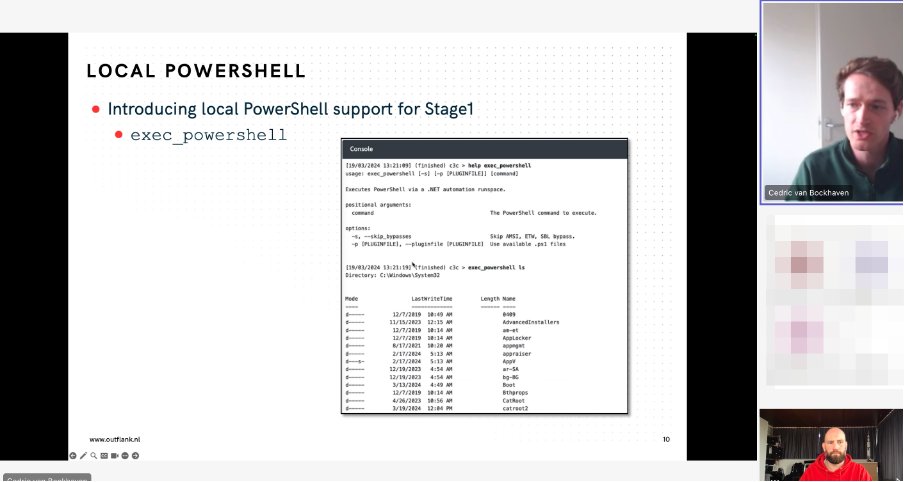
The PowerShell mafia is back! We are giving a Tech Deep Dive session right now where we look at new OST tools to leverage PowerShell for local and remote code execution. PowerShell is not dead for red teams! Available for #OST customers. More info at outflank.nl/ost
This training was really awesome, I learnt quite a few new tricks that still work on MS Office! thank you @StanHacked and @ptrpieter I might have a few ideas to improve oletools 😎
This training was really awesome, I learnt quite a few new tricks that still work on MS Office! thank you @StanHacked and @ptrpieter I might have a few ideas to improve oletools 😎
With his ability to stealthily get into houses, Santa is a natural red teamer, which is why he’s giving you the gift of offensive security! Register now for a free training course on Microsoft Office tradecraft, taught by @StanHacked and @ptrpieter outflank.nl/free-training-…
Let's explore the intricate dance of virtual to physical memory mapping in BYOVD tooling development! 💻 In @c3c's latest blog we delve into resolving addresses using Superfetch, unlocking control over physical memory. Dive into the details now 👉 outflank.nl/blog/2023/12/1…
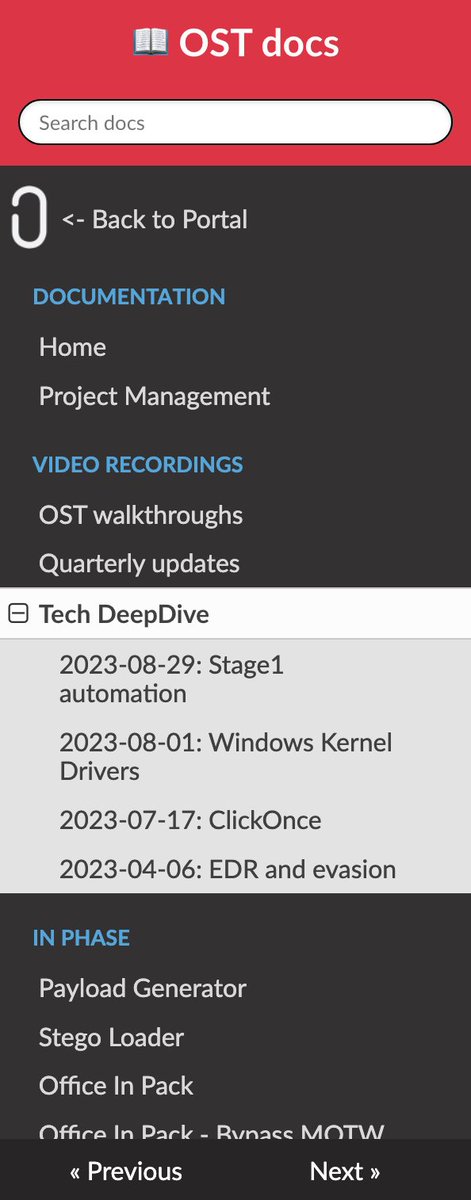
OST is tooling and tradecraft. Our upcoming Tech DeepDive session is with @_dirkjan. He will share OPSEC tricks and private tradecraft on Azure AD attacks. Super useful when red teaming against Azure. Such sessions are recorded and available to customers in their OST portal.
We’ve pushed “RemotePipeList” on our GitHub and released a blog post. The tools is used to list named pipes of remote systems. Useful for remote reconnaissance. Blog post here outflank.nl/blog/2023/10/1… C2 Tool Collection here github.com/outflanknl/C2-…
3 years ago, me, @StanHacked and @MarcOverIP set about creating our own con, built by red teamers for red teamers. Today it finally happened and it was 🔥 #redtreat23 @MDSecLabs @OutflankNL
Our team is expanding, we've recently onboarded Tycho and Kyle (@kyleavery_). Really happy to have these heroes onboard to bring our toolkit for red teams to the next level.
Upcoming demo session with the OST tech team this Thursday October 5th. Our red teamers and developers will do a deep dive into some of the core tools for initial access, C2 and OPSEC for Cobalt Strike. Subscribe here: outflank.nl/demo-request. Hope to see you on Thursday!
In a C2 framework, flexibility is crucial. Stage 1 (which is part of OST) can leverage #Python scripts for automations and event triggering. In this brief video, we showcase Jupyter Notebook automations and a bot that interacts with new implants. outflank.nl/videos/stage-1…
A quick and stable and OPSEC safe persistency method? #OST provides .node payload generation, including Function Forwarding. Great for persistency in favorite Electron apps, such as Teams, Slack, VS Code. Node Function Forwarding in Teams in 1 minute: vimeo.com/856314414
New combined blog detailing Cobalt Strike and Outflank 's collaborative efforts: Find out about our roadmaps moving forward and get a detailed use case demonstrating how Cobalt Strike and OST complement one another. #cobaltstrike #redteaming #ost outflank.nl/blog/2023/07/1…
Proud to release “Cobalt Strike UDRL in 60 seconds”; OST users can now leverage the power of User Defined Reflective Loaders (UDRLs) without writing C code or setting up a dev environment. vimeo.com/842875892/8559…
To emulate sophisticated actors such as Turla and Lazarus requires capabilities to manipulate the Windows kernel. OST customers have this capability a.o. with our newest tool KernelKatz: a credential dumper that abuses a vulnerable kernel driver to access LSASS memory.
Published a new @OutflankNL blog post together with @DaWouw! "So you think you can block Macros?" A journey into new MS Office macro abuse patterns and bypasses for typical enterprise VBA macro settings. Read why signing macros is sometimes a bad idea... outflank.nl/blog/2023/04/2…
My colleague @ptrpieter and I will be hosting a hands-on workshop on offensive MS Office tradecraft at @x33fcon in May. Three hours of @OutflankNL's latest initial access, persistence and lateral movement tricks that go beyond your good old macros. Hope to see you at #x33fcon!
🎉It's #BOFFriday again!🎉 We are adding 2 new public tools to the @OutflankNL repo at github.com/outflanknl/C2-…: > Psm: BOF to show detailed information on a specific process ID > ReconAD: BOF that uses ADSI to query Active Directory (AD and GC) objects and attributes Enjoy!
Outflank Security Tooling received a contribution from @SecuraBV, one of OST's trusted red teaming community members. We added a custom loading technique that bypasses most EDRs. Inspired on research by @azhurtanov, and now just one click away in OST's Payload Generator.
Some time ago we released O365TokenExtractor to OST customers. This BOF allows dumping O365 tokens stored by WAM (Web Account Manager) when using applications like MS Teams and Office. Here you can see it in action.

Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
mgeeky | Mariusz Bana.. @mariuszbit
11K Followers 611 Following 🔴 Red Team operator, ex-MWR/F-Secure pentester, ex-AV engine developer @ESET, green tea addict. 🫖 @[email protected]
b33f | 🇺🇦✊ @FuzzySec
32K Followers 844 Following 意志 / Antiquarian @ IBM Adversary Services / Ex-TORE ⚔️🦅 / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs
Dominic Chell 👻 @domchell
16K Followers 531 Following Just your friendly neighbourhood red teamer @MDSecLabs | Creator of /r/redteamsec | https://t.co/3k3EBAZqGd | https://t.co/KwO2OwDOkl
Marcello @byt3bl33d3r
29K Followers 532 Following CyBeRsEcUrItY | Not afraid to put down with some THICC malware on disk | securing and breaking AI @ProtectAICorp | Ex @spacex
Josh @passthehashbrwn
7K Followers 344 Following Adversarial Simulation at IBM, tweets are mine etc.
Dirk-jan @_dirkjan
25K Followers 173 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
Charlie Bromberg « .. @_nwodtuhs
13K Followers 648 Following Trying to hack the way we hack things 🏴☠️
bohops @bohops
13K Followers 454 Following Full StackOverflow Developer | Security Researcher | Red/Purple
Rad @rad9800
6K Followers 830 Following labs @praetorianlabs opinions are my own and not of my employer
an0n @an0n_r0
11K Followers 716 Following CRT(E|O|L) | OSCP | @RingZer0_CTF 1st (for 2yrs) | HackTheBox Top10 | RPISEC MBE | Flare-On completer | GoogleCTF writeup winner | SSD research | Math MSc |🇭🇺
Jean @Jean_Maes_1994
11K Followers 1K Following Director of Advanced Assessments -EU @neuvik | @sansoffensive Certified instructor/SEC565 author/SEC699 co author https://t.co/haRI3ruvlg
n00py @n00py1
13K Followers 955 Following Retweeter of InfoSec/Offsec/Pentest/Red Team. Occasional blogger/Independent security research. [email protected] on Mastodoge
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Outflank @OutflankNL
5K Followers 11 Following Offensive Tooling for Red Teams, Red Teaming and Trainings
Filip Dragovic @filip_dragovic
6K Followers 1K Following
FaustoBevly @FBevly61714
40 Followers 770 Following
saha @saha6912
12 Followers 75 Following
Socarates @AthenaWisdom13
1 Followers 171 Following
This site is a rageba.. @X_is_ragebait
53 Followers 221 Following
Hacker Hermanos @Hacker_Hermanos
144 Followers 376 Following Follow @Hacker_Hermanos for Offensive Security, Adversary Emulation, Red Team Tradecraft, Infrastructure and Methodology
Yuri @g0ttfrid
195 Followers 313 Following As your shadow follows your body. You become what you think. Be wise. Focus
BiGBells 🎈 @Traxx4G
234 Followers 654 Following
vandey1921 @vandey1921
3 Followers 46 Following
Carlos Mayorga @MayorgTech
286 Followers 2K Following System Administrator | Working on transitioning to Cybesecurity
Nick @___Nickolass___
28 Followers 145 Following Red Team Operator | Veteran 🇬🇧 | Husband | Father | Coffee Enthusiast
b-rad @bradcyb3rguy
0 Followers 53 Following
sajj @QiasSajad
0 Followers 698 Following
annie @AnnieAnnieyou12
1 Followers 381 Following
Soum Mohamed Islam @m3d1sl4m
8 Followers 94 Following Cyber security passionate | DFIR | CTF player | CS student | 🇩🇿
isaac fleming @apeptxi
54 Followers 70 Following
innxrmxst @innxrmxst
8 Followers 22 Following
Aslan Yıldız @a4sec
44 Followers 1K Following Penetration Tester, Reverse engineering fan. OSCP, OSED certificated
Ivanovitch21 @Ivanovitch21
5 Followers 122 Following
MikeWavada @WavadaMike
214 Followers 3K Following Cyber specialist specializing in Imposter Syndrome. Former USMC. Currently with Prestige Worldwide. Likes Nickelback.
... @ano_sec0r
124 Followers 854 Following
Momtaz U @UMomtaz89369
0 Followers 2 Following
Irsath Ahamed @Irsathz
406 Followers 3K Following Hacker | Developer | Security Researcher Digital Forensic Investigator
El Mito De Casandra @Sir_Koba
63 Followers 732 Following If I have seen further, it is by standing upon the shoulders of giants.
erm4 @er1cm4
17 Followers 71 Following
highjack @hiighjack
31 Followers 409 Following 決して降伏しない I like to hack websites, mobile apps, compiled apps and computers. #OSCP / #OSCE / #OSWE / #BSCP #CRTO in progress...
fedix_tools @Michell55437948
8 Followers 253 Following 🧑🍳SPY PARTNER// ETHICA//@HIRE📟 BEST 📟 HACKERS 🛑 Bitcoin RECOVERY 🛑 BLOCKCHAIN Business ANALYST #crypto /#NFTS recovery guru 1 CYBER 🛑SECURITY📟
Ted Foxx @TedFoxx238985
175 Followers 3K Following #cancersucks Constantly searching for help for cancer patients.
0xfc @0xfcsec
25 Followers 74 Following
dgevy @dgeevy
11 Followers 40 Following
Martin @cantcomputer
16K Followers 2K Following CSO @ TrustedSec | Music | Tattoos | H@x | Rad Memes
CyberTuna @netsectuna
339 Followers 322 Following OSCP. CRTO. OSWP. Maintainer @ExploitDB. Shitposts are my own. Rare cybersecurity tweets. Speed and power solve everything.
Sum0ne @Sumone921
0 Followers 114 Following
vx-underground @vxunderground
291K Followers 211 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Florian Hansemann @CyberWarship
75K Followers 47 Following Father, Founder @HanseSecure, Pentesting, Student, ExploitDev, Redteaming, InfoSec & CyberCyber; -- Mastodon: https://t.co/KFSKYUN98M
Grzegorz Tworek @0gtweet
29K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
mgeeky | Mariusz Bana.. @mariuszbit
11K Followers 611 Following 🔴 Red Team operator, ex-MWR/F-Secure pentester, ex-AV engine developer @ESET, green tea addict. 🫖 @[email protected]
b33f | 🇺🇦✊ @FuzzySec
32K Followers 844 Following 意志 / Antiquarian @ IBM Adversary Services / Ex-TORE ⚔️🦅 / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs
Dominic Chell 👻 @domchell
16K Followers 531 Following Just your friendly neighbourhood red teamer @MDSecLabs | Creator of /r/redteamsec | https://t.co/3k3EBAZqGd | https://t.co/KwO2OwDOkl
Marcello @byt3bl33d3r
29K Followers 532 Following CyBeRsEcUrItY | Not afraid to put down with some THICC malware on disk | securing and breaking AI @ProtectAICorp | Ex @spacex
Dirk-jan @_dirkjan
25K Followers 173 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
bohops @bohops
13K Followers 454 Following Full StackOverflow Developer | Security Researcher | Red/Purple
Rad @rad9800
6K Followers 830 Following labs @praetorianlabs opinions are my own and not of my employer
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Outflank @OutflankNL
5K Followers 11 Following Offensive Tooling for Red Teams, Red Teaming and Trainings
🥝🏳️🌈 Be.. @gentilkiwi
62K Followers 278 Following A kiwi coding mimikatz & kekeo github: https://t.co/eS3LVgU6i0 Head of security services @banquedefrance Tweets are my own and not the views of my employer
Austin Hudson @ilove2pwn_
6K Followers 34 Following Offline and looking for work. Living life happy and to its fullest . To reach me, I'm available @ [email protected]. GitHub: https://t.co/AihdCtKl5O
James Forshaw @tiraniddo
48K Followers 364 Following Security researcher in Google Project Zero. Author of Attacking Network Protocols. Tweets are my own etc. Mastodon: @[email protected]
ap @decoder_it
7K Followers 258 Following Incident Response and Security Consultant @semperistech . Independent Security Researcher. Cyclist & Scubadiver. MSRC MVR 2022.
CryptoCon @CryptoCon_
96K Followers 22 Following #Bitcoin Technical Analyst || Conservative long-term analysis || Here to help you make money || Creator of the Halving Cycles Theory
mr.d0x @mrd0x
40K Followers 246 Following Security researcher | Co-founder https://t.co/QxBlzpa7Y4 | https://t.co/zqMXQRZRGl | https://t.co/Fq7WSqU9kI | https://t.co/eKezFcOEcL
b4rtik @b4rtik
2K Followers 237 Following Sometimes pentester, sometimes sysadmin. OST Developer at @OutflankNL . eCPPT eCPTX eWPT
azhurtanov @azhurtanov
40 Followers 25 Following
Carsten @0xcsandker
2K Followers 132 Following Security enthusiast, Likes Windows Internals & AD In case twitter implodes: https://t.co/O5CSoJnrIK
HackerHotel @HotelHacker
2K Followers 366 Following Hacker Hotel provides a luxurious hacking experience. For hackers and makers, with workshops and lectures at all skill levels!
Antonio Cocomazzi @splinter_code
8K Followers 446 Following offensive security - windows internals - reverse engineering | https://t.co/29suYwH66H
Outsider Security @OutsiderSec
2K Followers 1 Following Security company focusing on Microsoft Entra and Active Directory security. Need an expert view or pentest on your cloud/AD? [email protected]
Cedric Van Bockhaven @c3c
815 Followers 335 Following
winterknife 🌻 @_winterknife_
4K Followers 5K Following low-level developer with a focus on 𝙸𝚗𝚝𝚎𝚕 𝚡𝟾𝟼 ISA devices running 𝚆𝚒𝚗𝚍𝚘𝚠𝚜 | R&D @BHinfoSecurity | https://t.co/lyJL0y7qRZ
kmkz @kmkz_security
18K Followers 1K Following Offensive Security fanatic, Offsec Team lead... pom-pom girl? Who fuckin' cares ??
Max Grim @max__grim
382 Followers 270 Following Red Teamer @OutflankNL | Cyber Security | Messing around with hardware
Greg Darwin @gregdarwin
2K Followers 659 Following Software development manager for Cobalt Strike @FortraOfficial | Professional nerd | Star Wars geek | Wednesdayite
Alfie Champion @ajpc500
2K Followers 515 Following Adversary Emulation Manager | Formerly MWR / @FSecure_Consult | Tweets my own
Charlie Clark @exploitph
5K Followers 1K Following
Peter Winter-Smith @peterwintrsmith
5K Followers 3K Following Security researcher & implant developer @mdseclabs; developing SAST @wsastsupport; malware, code analysis, appsec, cryptography. Trying to follow Christ.
Zerodium @Zerodium
26K Followers 0 Following Zerodium is the world-leading acquisition platform for premium zero-days exploits and advanced cybersecurity research. We pay BIG bounties, not bug bounties!
Filip Olszak @mitohormesis
948 Followers 546 Following
Joe Vest @joevest
7K Followers 916 Following Red Teamer丨Author of Red Team Development and Operations https://t.co/LTiTgnGiyY 丨Don't let perfect be the enemy of good | @[email protected]
Souhail Hammou @Dark_Puzzle
2K Followers 923 Following Reverse Engineering - Windows Internals - Malware Analysis - Vulnerability Research - Senior Reverse Engineer @Intel471Inc
Emeric Nasi @EmericNasi
5K Followers 427 Following CyberSecurity researcher, developer of MacroPack Pro and BallisKit offers. I have a passion for all infosec subjects especially redteam. My tweets are my own.
Michael Weber @BouncyHat
1K Followers 68 Following Security Consultant. Not affiliated with Red Hat. I just like the hat. @[email protected]
Kuba Gretzky @mrgretzky
13K Followers 642 Following Offensive security tools developer. Reverse engineer, vulnerability researcher and ex-MMO game hacker. Creator of Evilginx. @[email protected]
Jamie Shaw @1nPr0c
5K Followers 535 Following Principal Security Consultant / Red Team Lead @mdseclabs
CCob🏴�.. @_EthicalChaos_
8K Followers 414 Following Ceri Coburn: Hacker | R̷u̷n̷n̷e̷r̷ DIYer| Vizsla Fanboy and a Little Welsh Bull apparently 🏴 Author of poorly coded tools: https://t.co/P6tT2qQksC
DTM @dtmsecurity
3K Followers 1K Following Hacker, Security Engineer and Researcher - https://t.co/qC0NwIe7vh - @[email protected] views are my own
Erik Remmelzwaal @erikremmelzwaal
1K Followers 611 Following Managing Director @zolderio | Cybersecurity | Hacking | 🐘 https://t.co/koJ6IWT97m | 🦋 https://t.co/SzKAH1ySrm
X-C3LL @TheXC3LL
5K Followers 622 Following Just a biologist that loves to break cyber-stuff. Ka0labs / @AdeptsOf0xcc / ID-10-Ts member. 🦉
Bank Security @Bank_Security
41K Followers 321 Following Keeping you informed on the latest cyber threats #cybersecurity #threatintelligence
modexp @modexpblog
4K Followers 500 Following All opinions expressed here are mine only (not of my employer etc). Developer @MDSecLabs
ivs @ivansprundel
307 Followers 459 Following
Richard Davy @rd_pentest
1K Followers 897 Following Penetration Tester. CREST CCT | OSCE | OSCP | OSWP
Clément Labro @itm4n
7K Followers 169 Following Pentest & Windows security research (I stopped using this account in December 2022) ➡ Mastodon: @[email protected]Hey NL infosec tweeps. We gaan wat nieuws organiseren: Infosec Kart Cup 2024! Social event met andere red, blue, pentest, audit, CISO infosec profs in Nederland. 2 uurs kart race met bbq na afloop. €400 per kart voor een team van 2 tot 4. DM me voor meer info.
The PowerShell mafia is back! We are giving a Tech Deep Dive session right now where we look at new OST tools to leverage PowerShell for local and remote code execution. PowerShell is not dead for red teams! Available for #OST customers. More info at outflank.nl/ost
@StanHacked @kyleavery_ Nooo you changed it!! It needs to be Rerence forever!
This training was really awesome, I learnt quite a few new tricks that still work on MS Office! thank you @StanHacked and @ptrpieter I might have a few ideas to improve oletools 😎
With his ability to stealthily get into houses, Santa is a natural red teamer, which is why he’s giving you the gift of offensive security! Register now for a free training course on Microsoft Office tradecraft, taught by @StanHacked and @ptrpieter outflank.nl/free-training-…
Followed the @OutflankNL Microsoft office tradecraft training. Had to leave by five so I missed the last part of it. But it was really nice to see the expertise and insight of the Outflank team.
OST seems like a very nice options for teams performing red team operations. You won’t magically git gud, but it will offload quite some research and development time.
Yesterday was quite intense, @StanHacked and I presented an Offensive Office tradecraft session. Initially anticipated 50 participants, we closed registration in 48 hours as we had 1000+ 🔥. Session went well, got very positive feedback. Thanks all for listening in!
Thanks for sharing @OutflankNL @ptrpieter @StanHacked, it was a very nice one with cool stuff !
With his ability to stealthily get into houses, Santa is a natural red teamer, which is why he’s giving you the gift of offensive security! Register now for a free training course on Microsoft Office tradecraft, taught by @StanHacked and @ptrpieter outflank.nl/free-training-…
@StanHacked @ptrpieter Thanks a lot for the session on macros. Really interesting.
Ready for next year's conference season with the ROADtools SAO ❤️ huge thanks to @max__grim for the design. With @WEareTROOPERS badge for scale 😄.
Retweeting to raise awareness - I’ve been lucky enough to experience some of the Outflank office R&D and those guys are doing big things! 💪🏻
With his ability to stealthily get into houses, Santa is a natural red teamer, which is why he’s giving you the gift of offensive security! Register now for a free training course on Microsoft Office tradecraft, taught by @StanHacked and @ptrpieter outflank.nl/free-training-…
With his ability to stealthily get into houses, Santa is a natural red teamer, which is why he’s giving you the gift of offensive security! Register now for a free training course on Microsoft Office tradecraft, taught by @StanHacked and @ptrpieter outflank.nl/free-training-…
Let's explore the intricate dance of virtual to physical memory mapping in BYOVD tooling development! 💻 In @c3c's latest blog we delve into resolving addresses using Superfetch, unlocking control over physical memory. Dive into the details now 👉 outflank.nl/blog/2023/12/1…
Last weekend an Ivanti privilege escalation was presented at @BSidesLondon and at RedTreat earlier. @NorthwaveLabs allowed us to include a full weaponised version in OST and we want to thank them, and specifically @tijme and Alex (github.com/lldre) for their contributions.
.@DaWouw is back from his #blackhatMEA visit where he gave two talks about OST. Great attendance! We'll bring some material of his talks into the upcoming public OST demo sessions.
OST is tooling and tradecraft. Our upcoming Tech DeepDive session is with @_dirkjan. He will share OPSEC tricks and private tradecraft on Azure AD attacks. Super useful when red teaming against Azure. Such sessions are recorded and available to customers in their OST portal.
Time flies when you're having fun! In our newest blog we reflect on a year with @fortraofficial. We talk about transitioning the company, the cool stuff we did with OST, our cooperation with the Cobalt Strike team and we take a sneak peak into the future. outflank.nl/blog/2023/11/0…
Just found this photo on my phone, taken at the karaoke bar at RedTreat, Amsterdam, almost a week and a half ago! Thought I'd share! Good times. 🥳 Cheers to @StanHacked @domchell and everyone else on the photo!