Search results for #ghidra
Understanding and Improving The Ghidra UI for Malware Analysis embee-research.ghost.io/understanding-… #malware #análisis #Ghidra #tool
Now imagine if you were a cybersecurity engineer and had to use #Ghidra to reverse engineer and look at the assembly code. You wouldn’t be finding JavaScript that bad, so cheer up mate.
Now imagine if you were a cybersecurity engineer and had to use #Ghidra to reverse engineer and look at the assembly code. You wouldn’t be finding JavaScript that bad, so cheer up mate.
Decompiler Explorer takes a binary and shows decompiler output from popular tools such as #idapro, #binaryninja, and #ghidra: dogbolt.org Helps compare output from popular #reversing tools!
@2stage_Link 合計何バイトなんだろう?16進数かなとか思った。 #Ghidra #Ghidraで解析か
The 3rd part of our Ghidra scripting tutorial is out now! This time, I talked about how to create a call graph using Ghidra. Check it out! youtu.be/QKXBeU0QhPk #Ghidra #Scripting
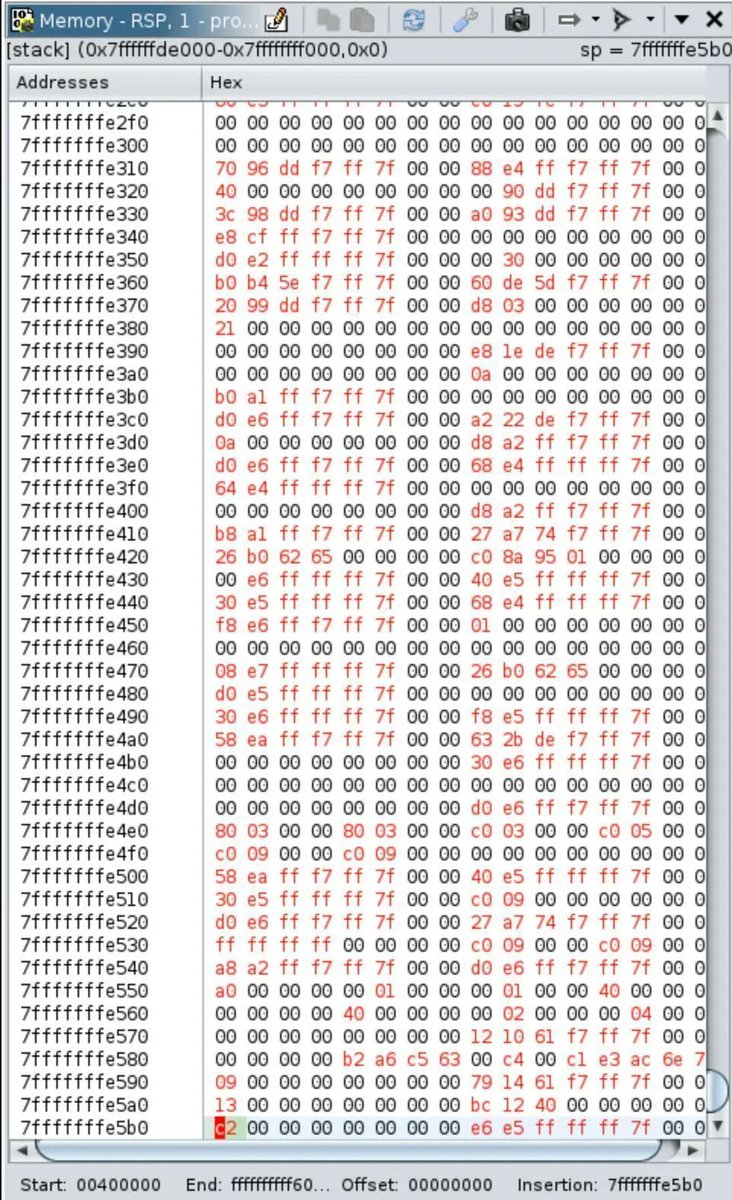
Getting started with Ghidra debugger (Official Ghidra documentation): github.com/NationalSecuri… #ghidra #reverseengineering
[New Blog Post] DWARF Verification via Ghidra and CBMC #ghidra #verification #binaryanalysis #compiler philipzucker.com/pcode2c-dwarf/
Advanced Static Analysis. Check it out! tryhackme.com/r/room/advance… #Cybersecurity #InfoSec #Malware #tryhackme #StaticAnalysis #Ghidra via @RealTryHackMe
Prochain MontreHack sur l'internet des objets! Rendez-vous au Nordelec à Montréal ou de n'importe où dans le monde sur Twitch et Discord :) Next event is on IoT, join us in person in Montreal or online. Date: April 17, 6-9 Details: montrehack.ca/2024/04/17/csg… #IoT #ghidra #decompile
🎉 Ghidra 11.0.3 has been released 1 hour ago with some minor fixes! 😋 👉 Ghidra: github.com/NationalSecuri… 👉 Change History: htmlpreview.github.io/?https://githu… 👉 Installation guide: htmlpreview.github.io/?https://githu… 🔥 I hope you enjoy this new version :) #ghidra #malware #reverseengineering
🔐 365 days of CTF @RealTryHackMe 🔐 {Day 12}: Compiled ⚙️ Difficulty: Easy Tags: #reverseengineering #strings #ghidra
You've just finished installing #ghidra, what is the first thing you do?
embeeresearch.io/ghidra-basics-… Useful guide when dealing with encrypted strings. #ghidra #reverseengineering #malware
Useful blog post for beginners approaching ghidra for the first time by @byte_how byte.how/posts/what-are… #ghidra #cybersecurity
Compiled. Check it out! tryhackme.com/r/room/compiled #binary #strings #tryhackme #ReverseEngineering #ghidra via @RealTryHackMe
🚨 Learning reverse engineering often starts with being able to identify the basics. In this video, we'll explore how to identify loops in the disassembler and decompiler using #ghidra 🐉 youtu.be/Y2qd0m4_4ZM
Only few spots left to grab this discount! The course has over 45 hands-on labs that guide you how to analyze #malware. Course covers using #IDA and #Ghidra, so it will be up to you to decide which tool to use and not us. More labs are being added too!! #DFIR #Cybersecurity #C5W
“#OpenSourceSofware - what, how and why?” - @radomirpolach at @InstallFest_SH #InstallFest2024 Heh - @Ghidra_Server made by #NSA (#NationalSecurityAgency). Learn more: ghidra-sre.org #OpenSource #Linux #FLOSS #FOSS #Ghidra #SoftwareReverseEngineering #SRE

HH en @GHidra
2 Followers 120 Following
ghidra @Ghidrahh
28K Followers 1 Following
Ghidra-Server.org @Ghidra_Server
597 Followers 12 Following Donating a community independent Ghidra server (not associated with the NSA) for any users of NSA's SRE Tool available from https://t.co/BHdVdXMTwI
キングギドラ (k.. @King_TLNA
249 Followers 137 Following The 2x Sunday Vintage Challenge Winning streamer, https://t.co/niqPTg4Gh0. small time grinder. Youtube is King_Ghidra
DOOM @MFDOOM
200K Followers 0 Following Official source for all things MF DOOM, METALFACE RECORDS & GAS DRAWLS. Estate Managed. DOOMSDAY Event & other inquiries email [email protected]
🄶🄷🄸🄳🅁�.. @Fxckdbythehydra
133 Followers 60 Following //+18 ACC! Minors will be blocked.\\ (Friendly writer, +5 years of experience, Lit/SemiLit. Open DMs. English acc)
GhidraTheGod @GhidraTheGod
103 Followers 100 Following #TwitchAffiliate #Streamer #Youtuber #Anime & #Gaming are LIFE |The more you know, the more you know that you don't know shit|
KING/QUEEN GHIDRA @wolfiihax
21 Followers 180 Following infosec student | future destroyer of intergalactic planetary systems | 19 | personal twitter: @XO_WOLFII
KingGhidra @KingGhidra69584
6 Followers 20 Following
Anthony Ghidra @AleksandarSimo8
5 Followers 50 Following
Liam Bartels @LiamGhidra
3 Followers 1 Following
Ghidra @Ghidra9
12 Followers 2 Following
Brian Knighton @lazybinding
673 Followers 111 Following Cybersecurity Researcher. GHIDRA. These are my personal tweets.
GhidraOnline @GhidraOnline
10 Followers 0 Following
Ghidra Enjoyer @ghidra_enjoyer
7 Followers 92 Following iOS Vulnerability Researcher at @InterruptLabs, views are my own.
Sawyer @Ghidra_
41 Followers 162 Following 22 || Pronouns: He/Him/His || Only on Tuesdays. || Profile Picture: @CurlyThat
Right Geek @GhidraZ
2 Followers 8 Following Essa é uma página anti cultura woke, aqui você encontrará as maiores desgraças feitas pela cultura woke 🚫🚫🏳️🌈 (lembrando que esse perfil é de HUMOR)
ghidra @ghidras
0 Followers 5 Following
Ghidra @Ghidra182326
7 Followers 1 Following
ghidra @ghidra141925
16 Followers 16 Following
ghidra @ghidraTHEkaiju
2 Followers 64 Following
The Captain @TheCapta.. @ArrrCaptain
887 Followers 302 Following Digital polyglot and Ghidra alumnus, he/him @[email protected]
Ghidra @kkkkddddddbbbbb
77 Followers 377 Following
Nou noussa @Ghidra_nou
3 Followers 7 Following
Anthony Ghidra @AnthonyGhidra
2 Followers 12 Following
S2G HİDRA @S2GHIDRA
0 Followers 6 Following
MF_GHIDRA @AlexBardsley8
1 Followers 0 Following
Ghidra99 @ghidra99
4 Followers 0 Following
KingGhidra @KingGhidra
5 Followers 21 Following
Brandon Lee @King_Ghidra
2 Followers 23 Following
Yuefeng Du @dav3n_re
661 Followers 421 Following Opinions are my own. Happy peering with @keen_lab and Katzebin (or @teama0e). Fan of IDA but loves Ghidra. Also member of XDSEC and L team.
あああ @ghidra_cp
2 Followers 31 Following
Virgiliu Ghidra @VGhidra
5 Followers 92 Following
David Álvarez @wormable
550 Followers 573 Following Malware Analyst at Gen™ | Author of the book Ghidra Software Reverse Engineering for Beginners
GhidraDevTips @GhidraDevTips
2 Followers 0 Following
ghidra @ghidralex
12 Followers 96 Following
Ghidra Akins @AkinsGhidr12035
0 Followers 1 Following
Daniel Porter Wilgar @stealthii
639 Followers 1K Following Day: Kube/AWS/Automation DevOps || Night: Ghidra/Modding/VFX experiments || Pan 🏳️🌈 (he/him) || Chiptune/VGM/Synthwave DJ || Former @Twitch streamer || #ADHD
Joaquin J. @KingGhidra99
2 Followers 6 Following
Ghidra_community @CommunityGhidra
2 Followers 1 Following All things for Ghidra. Created by @redragonx
King Ghidra @KingGhidra2
0 Followers 1 Following
ghidra Ghiryu @GGhiryu
0 Followers 0 Following
GHIDRA 02 @Ghidra0
0 Followers 0 Following
ghidra yt @ghidrayt73h
0 Followers 7 Following
Дмитрий Ган.. @Ghidra97
0 Followers 1 Following
King Ghidra @KingGhidra3
0 Followers 1 Following
new pc @GeedersGhidra
0 Followers 1 Following
ghidra_minus65 @GMinus65
0 Followers 0 Following
Virgiliu Ghidra @VirgiliuGhidra
0 Followers 4 Following
seradam frampton @KingGhidra702
3 Followers 0 Following
Nicolae Arteni @_GHIDRA_
0 Followers 1 Following
Anthony Vaccaro @ghidra88
2 Followers 2 Following
GhidraTheKaiju @GhidraK
1 Followers 0 Following
Gaby Ghidra @GabyGhidra
1 Followers 10 Following
ghidra @GhidraX
0 Followers 0 Following
KingGhidra @ghidra_king
1 Followers 3 Following
GhidraFanClub @GhidraC007
1 Followers 5 Following
Ghidra ghidra @GhidraG
1 Followers 21 Following
ghidra cris @ghidracris1999
0 Followers 3 Following
Gaby Ghidra @ghidra_gaby
0 Followers 12 Following
Ghidra Gaming @GamingGhidra
0 Followers 0 Following YOUTUBE LET'S PLAYER + STREAMER! COME CHECK ME OUT ON https://t.co/lCmUdxYiDP
Çhristopher Powell @godzilla_ghidra
0 Followers 12 Following
Raghav Ghidra @RGhidra81093
0 Followers 0 Following
King Ghidra @KingGhidra7765
0 Followers 0 Following
Troy @_KingGhidra_
0 Followers 3 Following
ThankfulGhidra134 @ghidra13448917
0 Followers 1 Following
Leslie P @QueenGhidra
0 Followers 0 Following
GhidraNSA @GhidraNSA
0 Followers 0 Following