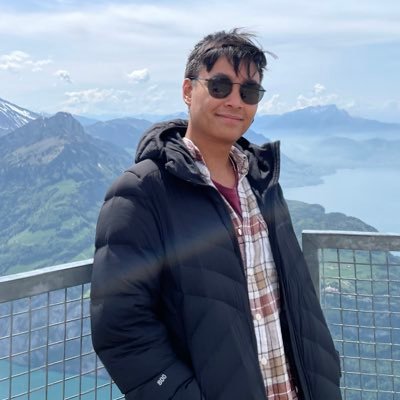
meadori @meadori
compilers;maths;codes;nintendos github.com/meadori Magnolia Springs, AL Joined December 2008-
Tweets22
-
Followers69
-
Following208
-
Likes190
Awesome work!
Ever struggle with C++ buffer issues? Spatial Safety is one of the main root causes for in-the-wild exploits! Read more about how we piloted the LLVM proposal for C++ Buffer Hardening here: bughunters.google.com/blog/636855965…
Come join us in the Google red team! We have a position open in NYC: google.com/about/careers/… The team is fantastic and the work is really cool. Message me if you have questions about the role but if you are interested please don't wait to get your application in.
Excited for @Google TAG’s annual look at 0days in the wild. Nice job @maddiestone - the thing that stood out for me was the importance of variant analysis to the exploit devs. blog.google/threat-analysi…
You're a 1337 hacker? Solve the gVisor sandbox challenge and others! g.co/ctf
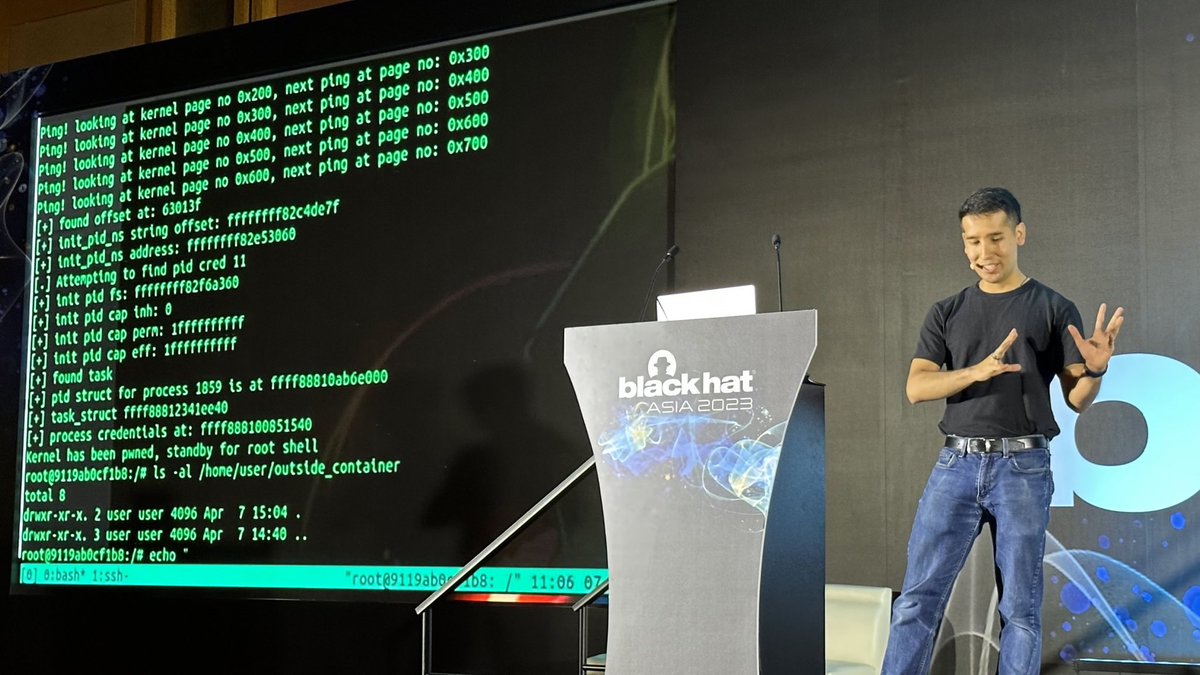
Kernel has been pwned #blackhatasia
At some point last fall/winter I felt like giving up on everything. I don’t know where i got the energy to keep going, but def one place was my work. Today, that work officially paid off: git.kernel.org/pub/scm/linux/… Fuzzer will be open sourced soon :)
A fun decryption story! In 1914, The Netherlands sent a peace mission to Albania (I did not know this either). The mission commander, Major Lodewijk Thomson, was killed in battle under circumstances that are still unclear. And we'd love to know! en.wikipedia.org/wiki/Lodewijk_…
t=0//#つぶやきProcessing Happy Holiday 🎅 draw=_=>{t||createCanvas(W=600,W) noStroke(background(0)) w=W/2 for(j=10;j--;)for(i=60;i--;){p=t+i q=TAU/40*p+TAU/10*j r=p*10 fill(p*20,p*30,p*20) circle(cos(s=q+j/5)*r/2+w,sin(q+j/6)*r+p*20,noise(j,p)*8+cos(s+1.5))} t=(t+0.01)%1}
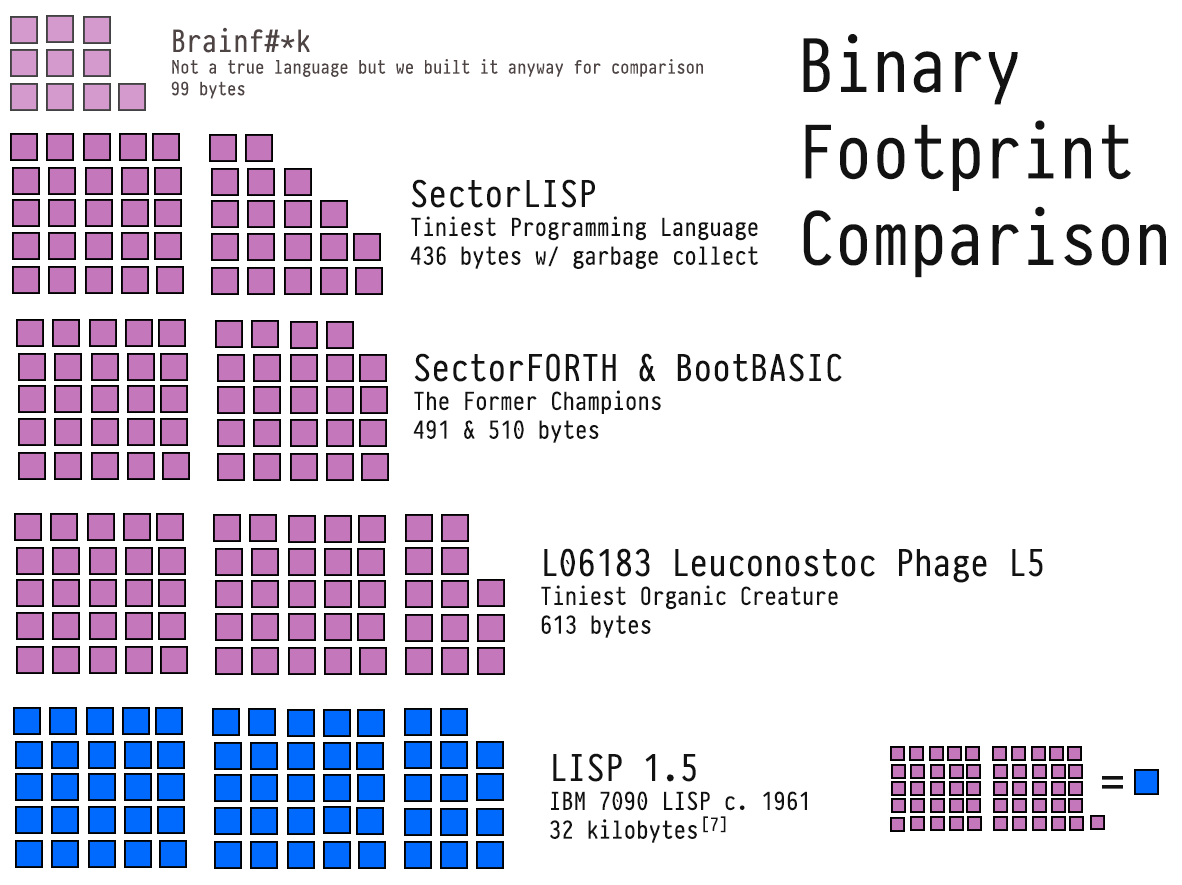
SectorLISP now supports garbage collection and we reduced its size to 436 bytes. That means LISP has now outdistanced FORTH and BASIC to be the most lightweight programming language in the world. justine.lol/sectorlisp2/
Seeing people testing log4j by injecting jndi into password fields. If that works, you don't need a patch, y'all need Jesus.
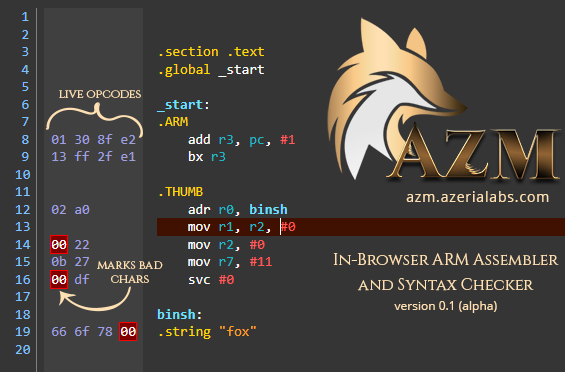
The first version of my ARM Assembler is finally finished! 🖤 AZM - Live ARM Assembler and Syntax Checker: azm.azerialabs.com - Supports most 32-bit ARM and 16-bit Thumb instructions - Automatic assembly of instructions as you type - Marks zero-bytes in output as you type
(•_•) <) )╯for sale: / \ \(•_•) ( (> ARM Cheat Sheet Poster / \ (•_•) <) )> from the finest arsenal. / \ Poster: teespring.com/arm-32-bit-ass… Digital: gum.co/arm-assembly-c…

Deb Pflugh @pflugh68609
77 Followers 5K Following
Francesca Hardiman @FrancescaH66229
73 Followers 5K Following
Neaulash @neaulash9882
0 Followers 141 Following
Katy Trouser @trous_k
40 Followers 5K Following
Sarah Billiet @BillietSara
75 Followers 5K Following
Malena Spene @male_spe
48 Followers 5K Following
Maribel Perozo @MaribelPer91050
93 Followers 5K Following
Perla Cobert @PCobert58381
24 Followers 5K Following
McKelade @KeladeMc9070
41 Followers 2K Following
Soughthes @soughthes16892
63 Followers 2K Following
Thathexoa @thathexoa61464
42 Followers 2K Following
Avery_Reed @reed_avery80208
0 Followers 230 Following
Topealeas @topealeas51493
85 Followers 770 Following
Smiseighph @smiseighph69038
44 Followers 1K Following
Alyse @Bellebytes
1K Followers 1K Following Red Team Director #GXPN #GMOB / I also sing for a band called LYLVC
Norah Patton @NorahPatto1178
83 Followers 3K Following
Briana @briana_lachance
111 Followers 3K Following
Angelina @angelina_wojens
220 Followers 3K Following
Reid Duke @reid_duke4488
113 Followers 3K Following
Rosalie @rosalie_rodriqu
323 Followers 3K Following
Matteo Colazilli @MatteoColazilli
10 Followers 141 Following
DK @0xdarkking_
106 Followers 868 Following
SealOSRS @SealOSRS
146 Followers 597 Following Twitch Affiliate at https://t.co/CNQW2kZiwE | Pet hunting (22/51) on a zerker. Trying to actually get good at this game.
Gerrard Tai @gerrard_tai
78 Followers 425 Following ex csgo pro for team "Counter-Terrorists" | pwn with @seetf_sg
goproslowyo @goproslowyo
1K Followers 4K Following Hacker. (SRE|DevOps|Cloud|Security) Professional. prev:🚀, @Google, @Apple and @Twilio/@SendGrid who's tweets are these? they're definitely not mine
Assaf @Assaf97975413
23 Followers 524 Following
Cryptanalyst @Cryptanalyst19
355 Followers 4K Following Exploit writer, Threat Intel and a crypto guy.
vierito5 @vierito5
2K Followers 3K Following Gneeeeeeeeeeinfoseeeeeeeeeeeec. Broken villain, former something.
A. S. M. Muhiminul Ha.. @muhiminulhasan
99 Followers 5K Following
st4m @stamatisl1
182 Followers 5K Following Site Reliability Engineer ©️ Vegan power 🥗 Reverse Engineering ⏪
crazyman_army @CrazymanArmy
6K Followers 3K Following CTFer / APT hunter / RedTeam / BlueTeam the member of @r3kapig the leader of @ShadowChasing1 CVE-2022-30190 find job opportunities opinions are own not group
George Karchemsky @gkarchemsky
50 Followers 656 Following
9MF @n1neMF
132 Followers 3K Following
Amedeo @amedeo_us
185 Followers 358 Following Global Product Security at @Oracle. Tweets are my own.
MFonsec@ @MFonsec3
31 Followers 308 Following
freeide @freeide6
61 Followers 2K Following
Sprinter @0xSpr1nter
44 Followers 587 Following RE, VR , Fuzzing , Windows internals , just another noob
Bishop Fox @bishopfox
26K Followers 5K Following A leading provider of #offensivesecurity solutions & contributor to the #infosec community. #pentesting #hacking VC @forgepointcap @carrickcapital @WestCap8
John Lambert @JohnLaTwC
44K Followers 787 Following Corporate Vice President, Security Fellow, Microsoft Security Research, johnla(AT)https://t.co/3dGtq71Nby
Clint Gibler @clintgibler
19K Followers 575 Following 🗡️ Head of Security Research @semgrep 📚 Creator of https://t.co/xwtIAI0CuJ newsletter
chrisrohlf @chrisrohlf
11K Followers 783 Following 🇺🇸 Waging algorithmic warfare since 2003. Software and Security Engineer. Non-Resident Research Fellow @CSETGeorgetown CyberAI
VUSec @vu5ec
4K Followers 138 Following Systems and Network Security Group @VUamsterdam. Co-led by @herbertbos @c_giuffrida @EKouwe
Retro Tech Dreams @RetroTechDreams
173K Followers 246 Following Retro tech, early web & vintage computing. 80s, 90s, 2000s nostalgia. Follow for daily posts.
Anthony Weems @amlweems
3K Followers 244 Following Cloud Vulnerability Research • The opinions stated here are my own, not those of my company.
Weld Pond | Chris Wys.. @WeldPond
57K Followers 1K Following Hacker. Co-founder/CTO Veracode. Former L0pht security researcher. GenAI Auto-repair of vulns is the future @[email protected]
Zero Day Engineering @zerodaytraining
6K Followers 1 Following Vulnerability Research & Courses • https://t.co/WDjQQrzTtR
Alisa Esage Шевч�.. @alisaesage
35K Followers 143 Following Independent hacker, solo winner Pwn2Own • Building my system of power knowledge @zerodaytraining
maxpl0it @maxpl0it
9K Followers 786 Following Principal Vulnerability Researcher at @InterruptLabs. Occasional Pwn2Owner
Manfred Paul @_manfp
5K Followers 279 Following Maths and cyber and stuff. Playing CTFs with @redrocket_ctf (and @Sauercl0ud). Pwn2Own Vancouver 2020..=2022, 2024. @[email protected]
DilDog Ⓥ @dildog
15K Followers 1K Following Trouble https://t.co/FPiPVkHFaZ | https://t.co/sNADz2vzjF | https://t.co/C7MwH63UcX
The Joy Of Cryptograp.. @JoyOfCrypto
1K Followers 4 Following The Joy of Cryptography is a free undergraduate-level textbook that introduces students to the fundamentals of provable security. By @GarbledCircus
SpaceX @SpaceX
34.6M Followers 113 Following SpaceX designs, manufactures and launches the world’s most advanced rockets and spacecraft
Elon Musk @elonmusk
181.7M Followers 585 Following
Aravind Machiry @machiry_msidc
497 Followers 223 Following a.k.a donfos. Assistant Professor, Electrical and Computer Engineering, Purdue University. Mastodon: @[email protected]
ctfradiooo @ctfradiooo
937 Followers 2 Following Cybersecurity podcast hosted by @adamdoupe and @Zardus focused exclusively on Capture the Flag (CTF).
Shellphish @shellphish
7K Followers 45 Following Capture the Flag Team from UC Santa Barbara's SECLAB and Arizona State University's SEFCOM. DARPA Cyber Grand Challenge 3rd Place. Phrack author. Let's hack!
Max Tegmark @tegmark
145K Followers 29 Following Known as Mad Max for my unorthodox ideas and passion for adventure, my scientific interests range from artificial intelligence to the ultimate nature of reality
Louis Nyffenegger @snyff
18K Followers 599 Following Founder/CEO/Trainer/Researcher/CVE archeologist @PentesterLab. Security engineer. Bugs are my own, not of my employer...
Ian Beer @i41nbeer
49K Followers 144 Following
hextree.io @hextreeio
5K Followers 2 Following 🌱 Grow your cybersecurity skills with concise and well-edited video courses - coming soon! Created by @LiveOverflow and @ghidraninja.
Retro Software @RetroSoftwareUK
618 Followers 342 Following Retro Software is both a community dedicated to supporting the development of new games for retro computing platforms and a publishing label for Acorn micros.
Joscha Bach @Plinz
129K Followers 754 Following FOLLOWS YOU. Artificial Intelligence, Cognitive Architectures, Computation. The goal is integrity, not conformity. https://t.co/rFUNzdYXuK
John Hultquist @JohnHultquist
28K Followers 1K Following Chief Analyst, Mandiant Intelligence @Google. @CYBERWARCON and @SLEUTHCON founder. Johns Hopkins professor. Army vet.
Christian Blichmann �.. @AdmVonSchneider
2K Followers 593 Following Everything is always broken. Googler by day. #BinDiff maintainer. My tweets, my opinion. During my lifetime, CO2 increased by 67.84ppm (so far). http://pronoun.
Kelly Shortridge @swagitda_
31K Followers 300 Following Senior Director @Fastly | software resilience + modern infosec | [email protected] | http:// https://t.co/68itNjq8tL | aka &void;
Brian Smith @BRIAN_____
3K Followers 549 Following
Veilid Ⓥ @VeilidNetwork
5K Followers 1K Following Pronounced: “Vay-lid”. An official CULT OF THE DEAD COW projekt. Social Media shouldn’t be monetized. Users are not a commodity. Privacy Matters.
Kim Zetter @KimZetter
95K Followers 3K Following Journalist - cyber/national security. Author - COUNTDOWN TO ZERO DAY: Stuxnet and the Launch of the World's First Digital Weapon. https://t.co/334DzfSL1f
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
dragosr @dragosr
25K Followers 10K Following Stop, Think, Pwn! (see also @[email protected] for alternate)
Daniel Litt @littmath
37K Followers 871 Following Assistant professor (of mathematics) at the University of Toronto. Algebraic geometry, number theory, forever distracted and confused, etc. He/him.
Specter @SpecterDev
34K Followers 266 Following Interested in Security and Exploit Development. Nano is the one true text editor.
Mudge @dotMudge
67K Followers 343 Following Make a dent in the universe. Find something that needs improvement: go there and fix things. If not you, then who? {he/they}
Calvin and Hobbes Fan.. @Calvinn_Hobbes
738K Followers 53 Following Posting all the greatest from the famous Calvin & Hobbes comics by Bill Watterson. Not affiliated with Calvin & Hobbes Contact: [email protected]
derek guy @dieworkwear
839K Followers 963 Following Menswear writer. Editor at @putthison. Creator of @RLGoesHard. Bylines at The New York Times, The Washington Post, The Financial Times, Esquire, and Mr. Porter
LaurieWired @lauriewired
30K Followers 205 Following Reverse engineer specializing in cross-platform malware analysis with a focus on mobile threats.
the tiny corp @__tinygrad__
33K Followers 61 Following We make tinygrad. Our mission is to commoditize the petaflop.
Jordy Zomer @pwningsystems
2K Followers 219 Following Security Engineer @ Google, likes fuzzing, static analysis and VR. The opinions stated here are my own, not those of my company.
David Chalmers @davidchalmers42
29K Followers 667 Following philosopher@NYU. consciousness, reality+, life, the universe, and everything.@thatjiaozi And where there are vulns there are exploits
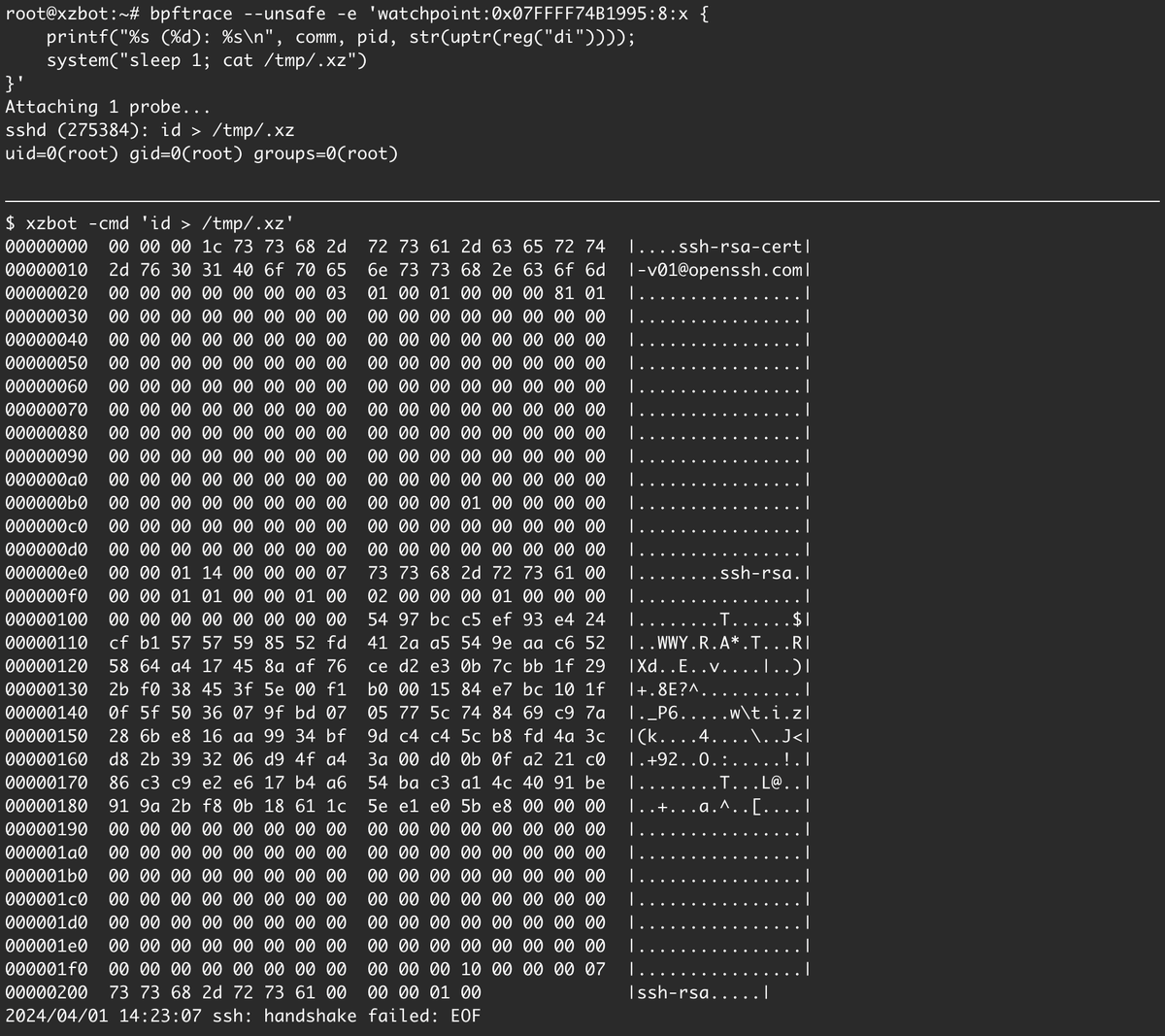
I've been reverse engineering the xz backdoor this weekend and have documented the payload format and written a proof-of-concept exploit for the RCE. The payloads are signed with an ED448 key, so I patched my own key into the backdoor for testing. :-) github.com/amlweems/xzbot
Wow!! Thank you ALL for so much support on my first #Pwn2Own win!! I’m very lucky to have a team and leadership that believes in me. I’m really proud of this bug; this is one of hardest exploits I’ve ever written. I can’t wait to share the details with you once it’s patched!
You don’t FIND exploits. You build them. You FIND vulnerabilities and exploit them. As an exploit developer that has failed to exploit lots of bugs that look good, the distinction is important 😭
Last year I discovered multiple bugs in virtio-net for VirtualBox (CVE-2023-22098, CVE-2023-22099, CVE-2023-22100) and wrote a 100% reliable VM escape using an out-of-bounds write (with ASLR defeat). Published the exploit code: github.com/google/securit…
Ever struggle with C++ buffer issues? Spatial Safety is one of the main root causes for in-the-wild exploits! Read more about how we piloted the LLVM proposal for C++ Buffer Hardening here: bughunters.google.com/blog/636855965…
Oct 14th 1995 - #Hackers of the world united to overload the Gibson, and prevent the Da Vinci virus from capsizing an oil fleet, designed to distract from "The Plague's" worm stealing $25m. 📽️📆 Hackers (1995) #HackThePlanet
That feeling when your exploit chain finally works in prod after months of work
Come join us in the Google red team! We have a position open in NYC: google.com/about/careers/… The team is fantastic and the work is really cool. Message me if you have questions about the role but if you are interested please don't wait to get your application in.
Idk, but the killer reason why I use vim is because I can ssh into a machine and dev there using tmux or screen. I don't have that with any IDE.
I don't get hard-core Vim developers. The gap between Vim and a modern IDE like Visual Studio Code is larger than Grand Canyon. I understand the keyboard argument, but you can use Visual Studio Code in Vim mode and get the best of both worlds. Are they really more productive…
Excited for @Google TAG’s annual look at 0days in the wild. Nice job @maddiestone - the thing that stood out for me was the importance of variant analysis to the exploit devs. blog.google/threat-analysi…
Always great to see this level of partnership across the ecosystem and shout out to @taviso for the great find on CVE-2023-20593. Thank you to @AMD for the partnership, collaboration like this is how we as an industry continue to keep users safe online cloud.google.com/support/bullet…
Zenbleed status. Great partnership across the ecosystem and shout out to @taviso for the great find on CVE-2023-20593. Thank you to @AMD for the partnership and collaboration, this is how we as an industry continue to keep users safe online. cloud.google.com/support/bullet…
And a reminder that we used github.com/google/buzzer to find this vuln! We are actively making the fuzzer better and adding more features. Stay tuned for new discoveries and feel free to contribute if you like the project!
I could say more thank you words for these three amazing people, but my gratitude does not fit in a single tweet :)
To conclude the tale of CVE-2023-2163 here is the exploit github.com/google/securit… Thanks again @chompie1337 for her amazing RCA and her other ebpf research @meadori For his amazing engineering feedback and also amazing help with RCA @scannell_simon For his original research!
I use Ghidra, Binary Ninja, and IDA - usually all at once. The performance of the first two is good enough that the price tag of IDA just isn’t warranted. Sorry. Binja is my daily driver because it’s the only one of the that’s not a pain in the ass to use.