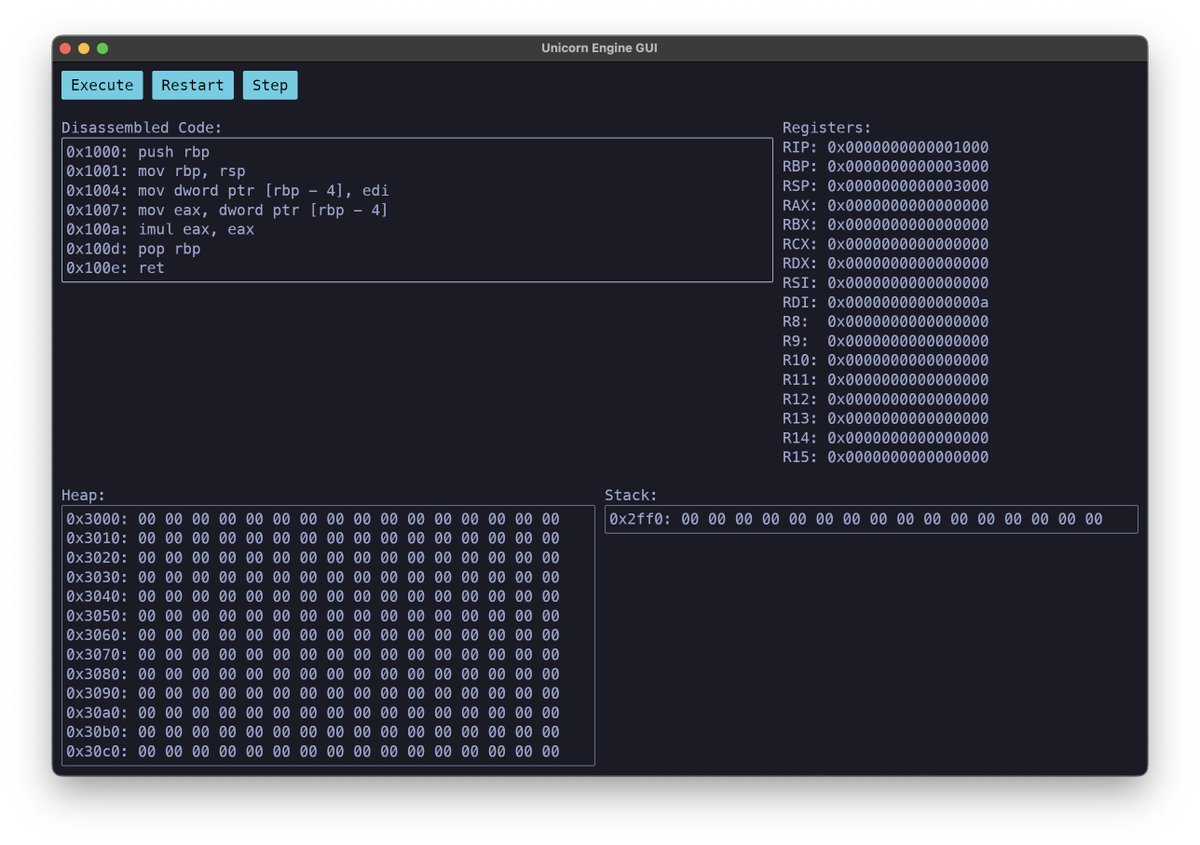
Unicorn Engine @unicorn_engine
The Ultimate CPU Emulator. Also see our related frameworks @capstone_engine, @keystone_engine unicorn-engine.org Joined June 2015-
Tweets1K
-
Followers6K
-
Following20
-
Likes834
Trends for United States
94,4 B posts
58,7 B posts
54 B posts
72,2 B posts
86,6 B posts
82,8 B posts
43 B posts
16,8 B posts
5.019 posts
2.309 posts
12,5 B posts
4.068 posts
44 B posts
8.345 posts
4.962 posts
4.767 posts
12,4 B posts
2.195 posts
6.637 posts
4.355 posts