Charlie Gardner @zcracga
Senior threat intelligence analyst @volexity charliegardner on Keybase Joined July 2014-
Tweets428
-
Followers516
-
Following526
-
Likes662
Evidence of exploitation and post-exploitation activity for #CVE20243400 can be found in log files on the FW in these locations: /var/log/pan/gpsvc.log /var/log/pan/md_out.log /var/log/pan/device_telemetry_send.log /var/log/syslog-system.log /var/log/pan/mp-monitor.log
Evidence of exploitation and post-exploitation activity for #CVE20243400 can be found in log files on the FW in these locations: /var/log/pan/gpsvc.log /var/log/pan/md_out.log /var/log/pan/device_telemetry_send.log /var/log/syslog-system.log /var/log/pan/mp-monitor.log
Details on 0day exploitation of CVE-2024-3400 by UTA0218. Post exploitation activity led to custom Python backdoor, UPSTYLE. Very impressive and speedy work by the team to get this out within a few days of initial observation. It's been a crazy week!
Details on 0day exploitation of CVE-2024-3400 by UTA0218. Post exploitation activity led to custom Python backdoor, UPSTYLE. Very impressive and speedy work by the team to get this out within a few days of initial observation. It's been a crazy week!
Our latest blog post details @Volexity's identification & incident response associated with the Palo Alto Networks GlobalProtect #0day vuln, assigned CVE-2024-3400, that the team found being exploited in the wild. Read more here: volexity.com/blog/2024/04/1… #DFIR #ThreatIntel
Our team at @Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this @PaloAltoNtwks advisory security.paloaltonetworks.com/CVE-2024-3400
security.paloaltonetworks.com/CVE-2024-3400 We have observed targeted exploitation of a 0-day in Palo Alto Global Protect firewall devices. Expect a writeup in the near future.
Great report on iSoon. One particularly striking line: "Local threat actors don’t appear to have any issues gathering intelligence; in fact, they’re so efficient at it that they cannot handle the volume." -> TAs likely care more about data processing than payload design nowadays
Great report on iSoon. One particularly striking line: "Local threat actors don’t appear to have any issues gathering intelligence; in fact, they’re so efficient at it that they cannot handle the volume." -> TAs likely care more about data processing than payload design nowadays
Following @Volexity's initial discovery & reporting on recent Ivanti Connect Secure vulnerabilities, @CISAgov released a joint advisory that warns #threatactors continue to exploit these vulnerabilities. More details + mitigations here: cisa.gov/news-events/cy… #dfir #threatintel
Following @Volexity's initial discovery & reporting on recent Ivanti Connect Secure vulnerabilities, @CISAgov released a joint advisory that warns #threatactors continue to exploit these vulnerabilities. More details + mitigations here: cisa.gov/news-events/cy… #dfir #threatintel
Natto shed some more light on the relationship between Chengdu 404 and iSoon. Prescient stuff
In September 2022, attendees at the inaugural @labscon_io heard about an actor I described then as "one of the most prolific, most deeply connected, and most technically advanced actors around". Events this week were a reminder that the video never went out, so here it is 👇
Roses are red, violets are blue... install my VPN, so I can pwn you. volexity.com/blog/2024/02/1…
In this blog post, @iMHLv2 + @attrc break down how @Volexity used #memoryforensics to discover two #0days being chained together to achieve unauthenticated remote code execution in Ivanti Connect Secure VPN devices. More details here: volexity.com/blog/2024/02/0… #dfir #threatintel
.@Volexity shares new observations on cont'd widespread exploitation of Ivanti Connect Secure VPN vulnerabilities. Now, 2100+ compromised devices & UTA0178 observed modifying built-in Integrity Checker Tool to evade detection. Details: volexity.com/blog/2024/01/1… #dfir #threatintel
Quick turnaround from targeted to mass exploitation of Ivanti Connect Secure VPN devices. Maintaining tempo is crucial for threat actors and so its not surprising to see an attempt to quickly extract as much value from their exposed tools as possible. Patch and investigate
Quick turnaround from targeted to mass exploitation of Ivanti Connect Secure VPN devices. Maintaining tempo is crucial for threat actors and so its not surprising to see an attempt to quickly extract as much value from their exposed tools as possible. Patch and investigate
It has been a busy December and January! We caught a Chinese APT group exploiting multiple chained 0days in Ivanti Connect Secure (Pulse Secure) to compromise the device and pivot into networks. This is a full unauthenticated RCE and impacts all supported versions! 1/2
It has been a busy December and January! We caught a Chinese APT group exploiting multiple chained 0days in Ivanti Connect Secure (Pulse Secure) to compromise the device and pivot into networks. This is a full unauthenticated RCE and impacts all supported versions! 1/2
Excellent work from the incident responders in identifying these exploits and associated artefacts. A serious amount of work went into this investigation and providing meaningful detection and mitigation guidance.
Excellent work from the incident responders in identifying these exploits and associated artefacts. A serious amount of work went into this investigation and providing meaningful detection and mitigation guidance.

Tyler McLellan @tylabs
3K Followers 599 Following Intrusion aficionado. @Google/@Mandiant Advanced Practices
Steve YARA Synapse Mi.. @stvemillertime
15K Followers 1K Following cyber-physical intel @google writing & sharing on adversary tradecraft, dfir, malware, threat detection, ics/ot intel and all things #yara
Kris McConkey @smoothimpact
5K Followers 867 Following #threatintel and #dfir lead @ PwC. Blue team forever. Christian, husband, dad, coffee addict, bad photographer, awful cyclist. Tweets my own, not PwC's.
Dan Black @DanWBlack
4K Followers 1K Following 🇨🇦 Manager, Cyber Espionage Analysis @Mandiant @GoogleCloud. Previous: @NATO Cyber Threat Analysis Branch & @cybercentre_ca. Views personal.
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
Gabby Roncone 🇺�.. @gabby_roncone
5K Followers 1K Following hunting russian apt cyber ops @Mandiant @GoogleCloud. views expressed here are mine, not my employer’s. she/her.
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Marc R @Seifreed
13K Followers 3K Following Experienced in threat intelligence, reverse engineering, and digital forensics. Linktree: https://t.co/fmPijUPWCC
Jamie MacColl @jamiemaccoll
7K Followers 4K Following Guitarist in @BombayBicycle | Cyber Security Research Fellow @RUSI_org | Senior Research Associate @cyber_conflict | Project Fellow @RISCS_UK
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon) https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Seongsu Park @unpacker
11K Followers 1K Following Zscaler APT Research | Formerly Kaspersky GREAT | Threat Intelligence Hustler | Tweets are my own | Keybase: @seongsupark | Mastodon: @[email protected]
Bartek Jerzman @secman_pl
2K Followers 3K Following Hunting ghosts in wires and boxes, former NCSC-PL, PL Navy #fightingthreats
Allison Wikoff @SaltyWikoff
538 Followers 823 Following #threatintel Americas Lead @pwc. Hype woman. Beach Rat. Former Adjunct @Columbia. Lover of all the APTs. | All views are my own. @[email protected]
Karthik @5up3r541y4n
59 Followers 244 Following SDE Security @getastra | Part-time h4x0r | I get high on learning.
Ai Dekorte @dekort_ai
72 Followers 5K Following
Lakeshia Berne @LBerne89760
84 Followers 5K Following
Karly Murrie @KarlyMurri14917
32 Followers 5K Following
Muireann Ullrich @MuireannU37692
35 Followers 5K Following
Ricardo @p1xi3s
41 Followers 2K Following
Simone Kraus @simonekrausora1
384 Followers 739 Following Content and opinions on this account are own views. These views are my own and do not represent those of my company.
xiaoyu @xunnun
85 Followers 689 Following
Erick Baraldi @_Baraldi
44 Followers 1K Following
Patricia cifuentes @patri22493
44 Followers 477 Following Cyber Threat Intelligence & Threat Hunter /Self-learning
Lorenzo @ptrac3
671 Followers 2K Following
Sumit @vu3scd
277 Followers 2K Following CISM CISP TMIET Prince (P) 27K1 CLIP 20 yrs experience in Enterprise Mobility and EPP / EDR security solutions. **ALL TWEETS ARE PERSONAL**
Michael Dunn | Off Ze.. @OffZeroCyber
219 Followers 785 Following Just a guy that has a passion for tailoring cybersecurity solutions for individuals, startups and small businesses. Lets do more with less and get off zero.
Alx Nuñez @alx_nunez
110 Followers 1K Following
Joe Moore @MooreJoseph
128 Followers 541 Following In my 50s now, married with 2 young kids, IT networking professional, interest industrial and metal music, horror novels, I lean toward the fan geek movies.
PhreakingGeek @PhreakingGeek
2K Followers 3K Following Purveyor of all things absurd. Security d00d. Lifelong learner. Human. Thoughts posted here are my own.
B:\a.zza @mcbazza
3K Followers 2K Following I.T. geek. Does things with computers/tech. All views are own. Don't take seriously. Or, should you? Servant to ̷5̷ 4x cats. He/him @[email protected]
Ed Targett @editortargett
2K Followers 2K Following Founder: The Stack. Work: Is this technology alphabet soup nutritious? Play: motorbikes, biodiversity, boxing. Not a soupçon of mischief or disclaimer in sight.
F @seallover212
4 Followers 34 Following
simon simonsen @ssimonsen0202
360 Followers 2K Following Without (log)data you’re just another person with an opinion. 4688+cmdLine, or it Did’nt happen. The IT Security guy @meethumio tweets are mine
Cfool @RedirectG
59 Followers 290 Following
Koen Claes @KoenClaes2
7 Followers 362 Following
CYBERWARCON @CYBERWARCON
4K Followers 566 Following Stay tuned for info about #CYBERWARCON 2024! 📧 Email us or visit the site for sponsorship info.
Louvenia Vautour @vauto_louven
23 Followers 3K Following
Kiana Rebolledo @rebolled_ki
40 Followers 5K Following
Caitlyn Defazio @CaitlynDef49812
37 Followers 5K Following
Lea Geno @LeaGeno298597
72 Followers 5K Following
Fox Bravo @FoxBravoCSC
72 Followers 885 Following Cyber Threat Intelligence Analyst Chief Editor, Cyber Sentinel Core (CTIA/AI/CyberSec/Threatscape) Substack musings: https://t.co/t16qQj0OQf
Mei Danowski @MeiDanowski
477 Followers 406 Following Threat intelligence research from geopolitical perspectives. Co-founder of Natto Thoughts.
Asli Koksal @asli_koksal
314 Followers 802 Following
Heather Brakke @BrakkeHeat9671
14 Followers 731 Following
lima @augustintech
3 Followers 1K Following
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Alan Neville @abnev
1K Followers 3K Following Principal Intelligence Analyst @ Symantec. Views are my own etc. https://t.co/XK1XdeAyJr
Tyler McLellan @tylabs
3K Followers 599 Following Intrusion aficionado. @Google/@Mandiant Advanced Practices
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Steve YARA Synapse Mi.. @stvemillertime
15K Followers 1K Following cyber-physical intel @google writing & sharing on adversary tradecraft, dfir, malware, threat detection, ics/ot intel and all things #yara
Kris McConkey @smoothimpact
5K Followers 867 Following #threatintel and #dfir lead @ PwC. Blue team forever. Christian, husband, dad, coffee addict, bad photographer, awful cyclist. Tweets my own, not PwC's.
John Hultquist @JohnHultquist
28K Followers 1K Following Chief Analyst, Mandiant Intelligence @Google. @CYBERWARCON and @SLEUTHCON founder. Johns Hopkins professor. Army vet.
Silas Cutler // p1nk @silascutler
13K Followers 2K Following Hacker, sometimes researcher @Only_Scans, @mal_share Resident Hacker @InsideStairwell, Adjunct Senior Cyber Threat Researcher @IST_org,
Dan Black @DanWBlack
4K Followers 1K Following 🇨🇦 Manager, Cyber Espionage Analysis @Mandiant @GoogleCloud. Previous: @NATO Cyber Threat Analysis Branch & @cybercentre_ca. Views personal.
blackorbird @blackorbird
28K Followers 600 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
MalwareHunterTeam @malwrhunterteam
219K Followers 36 Following Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.
Gabby Roncone 🇺�.. @gabby_roncone
5K Followers 1K Following hunting russian apt cyber ops @Mandiant @GoogleCloud. views expressed here are mine, not my employer’s. she/her.
Ivan Kwiatkowski @JusticeRage
9K Followers 73 Following Lead cyber threat researcher @HarfangLab. Maintainer of Manalyze, Gepetto, and writer. Trolling on a purely personal capacity.
John Scott-Railton @jsrailton
176K Followers 2K Following Chasing digital badness. Sr. Researcher @citizenlab @UofT @munkschool. Fmr.Ed. @SecPlanner. Tweets mine. Or find me on Mastodon: https://t.co/YPRqnoBtce
John @Big_Bad_W0lf_
2K Followers 699 Following Bad guys and Breaches with #AdvancedPractices 🦅 @Mandiant / @Google | tweets are my own
Dan Perez @MrDanPerez
4K Followers 1K Following Chief #Threat Aficionado @Mandiant | #Malware Naming Wizard | #Attribution Connoisseur | All tweets are my own. #ThreatIntel #APT
Volexity @Volexity
8K Followers 7 Following A security firm providing Incident Response, Proactive Threat Assessments, Trusted Advisory, and Threat Intelligence
Kim Zetter @KimZetter
95K Followers 3K Following Journalist - cyber/national security. Author - COUNTDOWN TO ZERO DAY: Stuxnet and the Launch of the World's First Digital Weapon. https://t.co/334DzfSL1f
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Sherrod DeGrippo 🦓 @sherrod_im
31K Followers 7K Following Strawberry Tempest. Weird security voyeur. Vibe merchant. CISO of your heart. Official USPS fan account. 🎉 Host of THE Microsoft Threat Intelligence Podcast.
Mathew @mittypk
1K Followers 668 Following Frontline Intel Ops 🦅 Advanced Practices @Mandiant | AU Military DCO | My views are my own
AuroraWatch UK @aurorawatchuk
170K Followers 36 Following Receive alerts when the #aurora may be visible from the UK. A service provided by Space Physicists at @LancasterUni For more information see our website
Mei Danowski @MeiDanowski
477 Followers 406 Following Threat intelligence research from geopolitical perspectives. Co-founder of Natto Thoughts.
Julian-Ferdinand @JulianVoeg
400 Followers 410 Following Threat Research @RecordedFuture. Formerly @SecReLabs. He/Him. 🏳️🌈 [email protected]
Asli Koksal @asli_koksal
314 Followers 802 Following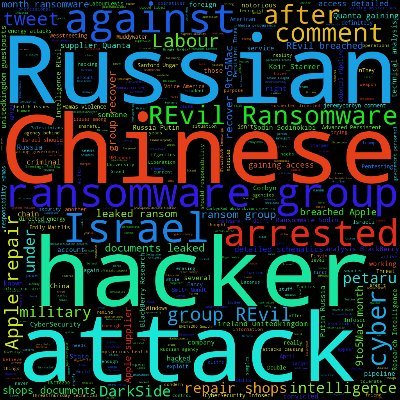
Anchored Narratives @AnchoredNarrat1
385 Followers 460 Following Relevant geopolitical (cyber) threats, forensics and crime stories generated by intelligence requirements. Sign up now so you don’t miss the next issue.
Alex Goldenberg @AlexWGoldenberg
1K Followers 1K Following Research Fellow at @RutgersU Miller Center | Intel at @ncri_io | @NYUCGA Alum | Investigating various forms of online harms.
Network Contagion Res.. @ncri_io
11K Followers 185 Following NCRI is a neutral and independent organization whose mission is to identify and forecast cyber-social threats and report on them in a timely fashion.
Aliz @AlizTheHax0r
1K Followers 961 Following Also https://t.co/Aq1HjGjiHq Curiosity/divergence/general hackery. Quite trans. Pronouns are they/them. Nonbinary, happily married.
watchTowr @watchtowrcyber
2K Followers 9 Following Your very own APT group, in an Attack Surface Management solution.
Emily Carroll @dreadphones
6K Followers 540 Following Threat Intelligence Analyst at Microsoft (MSTIC) • Board of Directors @kc7cyber • Words are my own • She/Her
kimber ✨ @kimb3r__
3K Followers 1K Following big computer fan ✨ data shenanigans @greynoiseio ✨ @dc801 influencer
Granitt @GranittHQ
2K Followers 1 Following Founded by Runa Sandvik. Securing journalists and at-risk people around the world. Tweeting as @runasand.
لب دوختگان |.. @LabDookhtegan2
3K Followers 101 Following افشای چهره منفور جمهوری اسلامی ایران در کانالهای رسمی لب دوختگان: https://t.co/xhKHbrewey… https://t.co/wvW79mSI8d https://t.co/UUBQ91sZ4n…
Adrian Zenz @adrianzenz
57K Followers 247 Following Director & Senior Fellow in China Studies at @VoCommunism. Researches Xinjiang & Tibet. Author of https://t.co/EHKzeapEB0
Amin Sabeti | امی�.. @AminSabeti
75K Followers 982 Following Infosec, Intelligence Analysis, Hunting Iranian State-Backed APTs, Founder @Certfalab 📱WhatsApp & Signal: +44 7888 865050 📧 [email protected]
TT @SungtingTsai
293 Followers 270 Following Staff, https://t.co/YOUEhjxzYy Core member, https://t.co/N5gLstYtv2
TeamT5 @TeamT5_Official
2K Followers 18 Following Top Malware Researcher & #Cybersecurity Solution Provider in Asia & Pacific Intelligence Portal: #ThreatVision EDR Solution: #ThreatSonar_Anti_Ransomware
Nathan Law 羅冠聰 @nathanlawkc
334K Followers 1K Following Youngest lawmaker of #HongKong. Activist. Exiled in London. Author of Freedom. Founder @HKDC_US @HKUC_UK @hongkongmarch @demosisto (defunct) #TIME100
Global Detwin with Ch.. @DetwinChina
191 Followers 194 Following We are a group of Hongkongers calling for the termination of sister city agreements with China
Axelle Ap. @cryptax @.. @cryptax
6K Followers 266 Following Mainly about security, OS, mobile phones. The postings on this page are solely my own opinion and do not represent my employer.
Mark Karayan @Mgkarayan
975 Followers 4K Following @googlecloud Threat Intel Comms Lead. I don't want to sell anything, buy anything, or process anything as a career. If you have a beagle, please let me pet it.
tay @TaylorLongg
313 Followers 190 Following threat intel at @Mandiant @GoogleCloud| Ice cream enthusiast | Views are my own.
Austin Larsen @AustinLarsen_
688 Followers 814 Following Incident Response and APTs @Google/@Mandiant | Opinions are my own
Sophie in 't Veld @SophieintVeld
44K Followers 3K Following Co-Lead Candidate @VoltEuropa ⚡️🇪🇺Europees lijsttrekker Volt België 💜🇧🇪Instagram: sophie.intveld
KDR @kristindelrosso
1K Followers 914 Following
Jay Park(박재우) @Pparkjaewoo
398 Followers 503 Following Journalist at Radio Free Asia(RFA) in Washington D.C. Focus on North Korea. Reptile 🦎 media officially recognized by North Korea.
Adam Langley @BuildHackSecure
8K Followers 681 Following Full stack dev, I train ethical hackers & teach web devs to secure their code & infra. CTO @hackinghub_io and director @bsidesexeter
Lucas Pope @dukope
109K Followers 95 Following Game developer. Return of the Obra Dinn, Papers Please, Republia Times, Helsing's Fire, Mightier, etc. https://t.co/0nGUOUZVE9
Paul Chichester 🏴�.. @0xChich
2K Followers 401 Following Director Operations, NCSC, GCHQ. Views entirely my own and do not necessarily reflect those of my organisation. 🏴 @[email protected]
Karl Roberts @ProfKARobs
431 Followers 757 Following Dad, Husband, Behavioural Insights Consultant, Forensic Psychologist, Professor, Health Security, Threat Assessment
Aniseh Bassiri Tabriz.. @AnisehBassiri
3K Followers 2K Following Senior Analyst @Control_Risks; #MENA security and geopolitics https://t.co/ezGftFTxHg
Tobias Borck @tobiasborck
1K Followers 740 Following @RUSI_org Senior Associate Fellow; from 🇩🇪and🇬🇧; PhD @UniofExeter. All views my own, retweets ≠ endorsement.
The Bug(official) @thebugzoo
18K Followers 619 Following Pressure/Intercranial : Official FB Artist Page : https://t.co/iDCpT4hXJV… Bookings : [email protected] 'Machine 1' out NOW
Feargal Sharkey @Feargal_Sharkey
236K Followers 882 Following "Regularly touts on Twitter", Secretary of State for Environment, Thérèse Coffey.
Ankur @kernelm0de
445 Followers 475 Following
Marianna Spring @mariannaspring
97K Followers 10K Following BBC’s Disinformation & Social Media Correspondent | Radio 4 podcasts | Investigations @BBCPanorama & current affairs | #Americast host | RTS & BPG winner
PLAOPs @PLAOpOSINT
151 Followers 7 Following Shedding light on #China and #PLA operational proficiency. All opinions are my own. RT =/= endorsement I also shitpost. Like, a lotMy new favourite technical drawing tool is Excalidraw.. Just the right amount of unprofessionalism to keep the inner anarchist alive.
Unplugging PlugX - Sinkholing the PlugX USB worm botnet - #plugx #mustangpanda #worm blog.sekoia.io/unplugging-plu… (h/t @charlesmeslay, @r1chev & @sekoia_io)
⛺️Dartmoor National Park Authority have updated the map showing where public can camp on the commons... Regardless of the outcome in the Supreme Court this autumn, this will likely be the definitive zonation going forward. 🧵So, let’s take a look at what’s GONE and what's NEW.
super interesting backdoor design 🐍📜🧹
Our threat brief is up, Operation MidnightEclipse #CVE20243400 unit42.paloaltonetworks.com/cve-2024-3400/
And huge thanks to the @Volexity team. Check out their blog on the activity volexity.com/blog/2024/04/1…
It wouldn't be a Friday in Infosec if there wasn't a 0day exploited in the wild by and APT, and yes it was a VPN again
Our team at @Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this @PaloAltoNtwks advisory security.paloaltonetworks.com/CVE-2024-3400
Our team at @Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this @PaloAltoNtwks advisory security.paloaltonetworks.com/CVE-2024-3400
#ESETresearch has discovered a new campaign by 🇨🇳China-aligned #APT #EvasivePanda, leveraging the Monlam Festival to target Tibetans. The campaign included a targeted watering hole, compromised news website, and an additional supply-chain attack ... welivesecurity.com/en/eset-resear… 1/7
So while the US slaps sanctions on #Intellexa spyware vendor, it can operate unhampered in the EU. No-one lifts a finger, not the national authorities (they wouldn’t would they, as they are actually using it) nor the @EU_Commission. EU is a #spyware paradise
BREAKING: US Treasury sanctions commercial spyware consortium & key enablers for spyware abuses. OFAC designations = America’s big gun. First time they’re used against a mercenary spyware company. Huge deal, let me break the #sanctions against #Intellexa down 1/
We published our in-depth analysis of the I-Soon leak. We detail their offerings, victimology and relationships with known APT activities: harfanglab.io/en/insidethela…
We're releasing our analysis of the I-Soon leak. As the title implies, it's *extremely* comprehensive. My longest 🧵 ever follows. harfanglab.io/en/insidethela…
Following @Volexity's initial discovery & reporting on recent Ivanti Connect Secure vulnerabilities, @CISAgov released a joint advisory that warns #threatactors continue to exploit these vulnerabilities. More details + mitigations here: cisa.gov/news-events/cy… #dfir #threatintel
We released a Cybersecurity Advisory to assist organizations with understanding the ongoing exploitation of multiple vulnerabilities w/Ivanti Connect Secure & Policy Secure as well as ways to mitigate potential, dormant compromise. Learn more: go.dhs.gov/Jeg
41 shots of baijiu: After the Natto Team's report on i-SOON in last October, the recent i-SOON leak gives us new perspectives on the business culture of China's hacker-for-hire industry. #isoon #hackerforhire nattothoughts.substack.com/p/i-soon-kicki…
The #Predator #spyware ecosystem is not dead - #Cytrox 👇blog.sekoia.io/the-predator-s…
bristol tonight @RoughTrade ! doors 730 pm Johanna Warren 8 pm (!!!!) Speedy Ortiz 9 pm
This week, we will drop "Hunting APT38 Lazarus Group/Bluenoroff 🇰🇵, part two" where you'll discover how this group impersonates cryptocurrency exchange organizations. @Intel_Ops_io
My write up with @milenkowski on the I-Soon leaks is now out!
🇨🇳 The leak of I-Soon, a key player in #China's cyber operations, exposes a #hacker #marketplace driven by state demands. Discover the strategic motives behind these operations in @DakotaInDC & @milenkowski latest research: sentinelone.com/labs/unmasking… #CyberSecurity
In September 2022, attendees at the inaugural @labscon_io heard about an actor I described then as "one of the most prolific, most deeply connected, and most technically advanced actors around". Events this week were a reminder that the video never went out, so here it is 👇