CyberArk Labs @CyberarkLabs
The official Twitter account for @CyberArk Labs news and updates from our threat research team. #CyberSecurity Labs.CyberArk.com Tel Aviv, Israel Joined March 2021-
Tweets303
-
Followers1K
-
Following24
-
Likes193
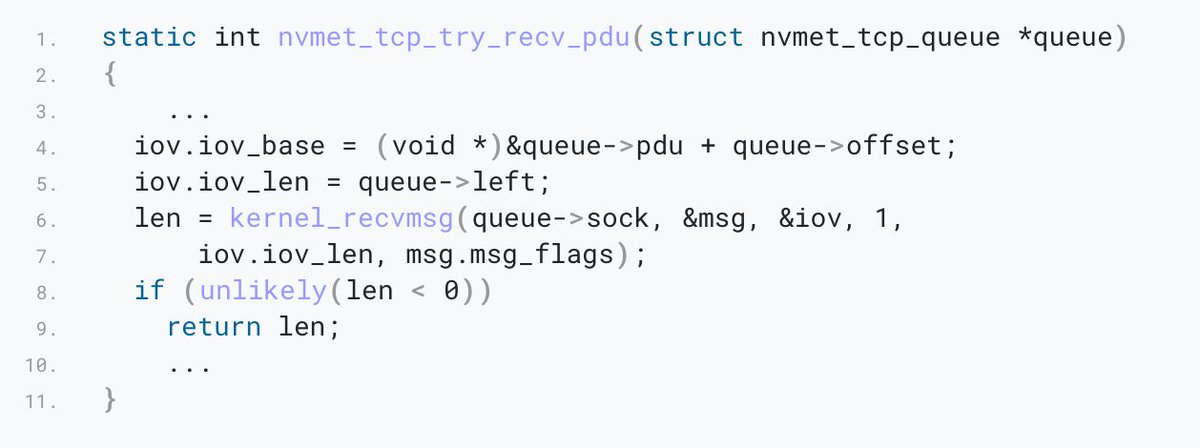
It was a pleasure to talk about my latest project of adding NVMe-oF/TCP to syzkaller during the @1ns0mn1h4ck conference.
Be sure to check out my recent blog about my latest research “Your NVMe had Been Syz’ed”. In there I show how to add new subsystems to syzkaller, and how to use it to find new vulnerabilities. cyberark.com/resources/thre…
We are hiring! We're currently looking for - Senior Malware Researcher - Senior Penetration Testing Engineer - Senior Vulnerability Engineer - AI Security Development Intern careers.cyberark.com
In a world with increased web session hijacking, @CyberarkLabs Malware Analyst Ari Novick breaks down how your organization can minimize the risk of unauthorized access with CyberArk Secure Browser. spr.ly/6019ZCrMS #IdentitySecurity #SecureBrowser #cybersecurity
I need your help. I'm hosting an AMA style chat between myself, @Red_Sec_Shay and @BbMurphy on April 16th. I've got some great topics I want to cover, but I'd like to know what sorts of questions YOU want to ask. Shay is the VP of our Red Team Services, and Bryan runs the…
🍪 Hot off the press! 🍪 Let's talk about cookie-stealing malware and session hijacking You’ll also cover various infostealer families & their techniques. cyberark.com/resources/thre…
In a digital age rife with evolving cyber threats, @Andy_Thompson , Global Research Evangelist at @CyberArk , delves into cybersecurity challenges and strategies. #CyberSecurity #Deepfake #PolymorphicMalware #SocialEngineering #CyberArkLabs Read More: t.ly/fve0w
Have you checked out GETMYFILEBACK.com yet? We've made it super easy to recover data from intermittent encryption attacks! Check out this simple demo by @Andy_Thompson youtu.be/SaxSgGcv3Js #ALPHV #Blackcat #ransomware
Using #WhitePhoenix, you can recover the unencrypted portions of files compromised by intermittent encryption. youtu.be/n3RxZdLwhBA
Finally got around to publishing this post on a 𝙘𝙧𝙞𝙩𝙞𝙘𝙖𝙡 𝙫𝙪𝙡𝙣𝙚𝙧𝙖𝙗𝙞𝙡𝙞𝙩𝙮 𝙞𝙣 𝙖 #𝗖𝗼𝘀𝗺𝗼𝘀𝗦𝗗𝗞 𝙘𝙝𝙖𝙞𝙣! Dive in if you're interested in the security of the #IBC protocol and the Cosmos in general 🪐✨ cyberark.com/resources/thre…
Namaste @Andy_Thompson!
🔴🔴🔴 NEW JOB ALERT 🔴🔴🔴 We're looking to hire a senior pentester... linkedin.com/jobs/view/3823…
🔥Hot off the presses!🔥 @Andy_Thompson reviews the TTP's in the latest nation-state attack on Microsoft. cyberark.com/resources/all-…
Technical Analysis of the poorly written PLAY ransomware... 🔥NEW TOOL ALERT!🔥 Check out GetMyFileBack.com cyberark.com/resources/thre…
CVE-2024-23897 (CVSS 9.8): Critical Jenkins Security Vulnerability, RCE Possible securityonline.info/cve-2024-23897…
I was quoted in a recent article by @ITPro. "It does not matter how complex your password is, it doesn't matter if you're using the latest and greatest MFA. Once you hack a cookie, you hijack the session and you bypass all that." itpro.com/software/googl…
When I was talking about the technology that came before generative AI, I was talking about Microsoft's Tay chatbot. Remember how that went? ☠️
When I was talking about the technology that came before generative AI, I was talking about Microsoft's Tay chatbot. Remember how that went? ☠️
"Generative AI has adaptive learning speed, contextual understanding and multimodal data processing, and sheds the more rigid, rule-based coat of traditional AI, supercharging its security capabilities" @Andy_Thompson ft.com/content/35d65b…

INTENT - The security.. @IntentSummit
559 Followers 8 Following INTENT - The security summit for researchers / by researchers. December 18, 2023 • Tel Aviv
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
⛈️ rainmaker ⛈�.. @Andy_Thompson
3K Followers 1K Following Master of Ceremonies of the @Dallas_Hackers | @CyberArkLabs Hypeman
Grzegorz Tworek @0gtweet
29K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Shak Reiner 🍍 @ShakReiner
395 Followers 730 Following Principal Security Researcher @CyberArk Labs. Tell your dog I said gm.
🎙Cyber Distortion .. @DistortionCyber
2K Followers 2K Following The Cyber Distortion Podcast covers all of today's relevant topics related to anything and everything in the world of Cybersecurity. Our opinions are our own!
Muhammad Ridhwan @mdridhwan07
104 Followers 2K Following Chelsea FC ultra and wave rider. Former soldier, 5 SIR, 3 Div. Laksamana Melayu, Rejimen Melayu, Temasek.
Frost @Fr0st1706
26 Followers 362 Following
Wellmissingh @wellmissingh
0 Followers 7 Following
Alex Elbaum @Alex0x90
5 Followers 194 Following
Escanor @escanor_rhitta
30 Followers 408 Following
Jallal_Eddine @BmjJallal
0 Followers 93 Following
Michael Gray @msg76710
194 Followers 884 Following
Luis Gustavo Nogales @luis1xv
31 Followers 277 Following
Mike Bean @nobodymikey7
1 Followers 57 Following
Haruna Muwawu @HMuwawu1
5 Followers 45 Following
Avishkar More @Avishkar_03
68 Followers 223 Following
Olu Olaleye @OluOlaleye_1
60 Followers 118 Following
星曜 @jingxie48465348
57 Followers 829 Following
. @juviag4
2 Followers 479 Following
Ahmed Boureghida @0xmid00
5 Followers 358 Following 🔍 Exploring the world of cybersecurity as a student 📚 | Passionate about penetration testing and eager to learn 🖥️
Joe @Joe31764327
35 Followers 483 Following
Joe @_joestevens_
33 Followers 1K Following
aliveli85 aliveli85 @Aveli8527345
4 Followers 152 Following
听众 @e7HoldYoung
86 Followers 3K Following
Osama Eldosoky @Osama_esoo0
204 Followers 2K Following Offensive security engineer & bug bounty hunter. Tweets are my own.
Bikash Dash @Memport
160 Followers 1K Following गते शोको न कर्तव्यो भविष्यं नैव चिंतयेत्। वर्तमानेन कालेन वर्तयंति विचक्षणाः॥ Vuln Research♧Exploitation♧Fuzzing♧PenTest
0xN1ghtStalker @0xN1ghtStalker
790 Followers 4K Following Hacker for good, Cyber athlete, Security researcher, ex-DHS, he/him, all opinions here are my own. sometimes 18+, twitch username: Nyxthewarlock
Kenergizer @Kenergizer1
67 Followers 133 Following
BlueEye @BlueEye46572843
180 Followers 547 Following Open to immediate work,reverse engineer & malware researcher who is interested in #APT research and targeted #malware.Views are my own.
MTaborda @mtaborda00
110 Followers 1K Following
Giulio Compagnone @GiulioCom
27 Followers 161 Following
Andrew Tarczynski @AndrewTarczynsk
0 Followers 12 Following
Shelan de Livera @shelandelivera
22 Followers 1K Following Cyber security and DevOps professional with a love for programming and machine learning: IT Architectures | Deployments | Linux | SIEM/SOC | Python
RK @tweet_rk
5 Followers 66 Following
ChBu @topher90
8 Followers 121 Following
jean vivine @JeanVivine
59 Followers 408 Following
Jason Carroll @jas0ncarr0ll
148 Followers 549 Following
IDC | Türkiye @IDC_Turkiye
2K Followers 311 Following The premier global provider of market intelligence, advisory services, and events for the IT, telecommunications, and consumer technology markets
Noddle @noodlegoestotwt
0 Followers 16 Following
Alireza Sadeghpour @alireza11048
34 Followers 202 Following pain ... you made me a believer believer
Siddhartha Rao 🇮�.. @dfirwallah
690 Followers 760 Following Security = Passion. #DFIR for profit, CTFs for fun. Never letting a good crisis go to waste. Researching cloud threats. Ex-chapter lead @OWASPBayArea
Abner @0x4A6F686E
36 Followers 692 Following
Leon Basin @BasinLeon25499
112 Followers 745 Following Passionate about pioneering secure, user-friendly cyber solutions. Building bridges in #BusinessDevelopment for @FudoSecurity. Driven by innovation.
Souvik Mazumdar @Souvik2bai
9 Followers 163 Following
Enrico Westendorf @Pfeffi09
5 Followers 23 Following
INTENT - The security.. @IntentSummit
559 Followers 8 Following INTENT - The security summit for researchers / by researchers. December 18, 2023 • Tel Aviv
⛈️ rainmaker ⛈�.. @Andy_Thompson
3K Followers 1K Following Master of Ceremonies of the @Dallas_Hackers | @CyberArkLabs Hypeman
Shak Reiner 🍍 @ShakReiner
395 Followers 730 Following Principal Security Researcher @CyberArk Labs. Tell your dog I said gm.
David El @0xdavidel
141 Followers 208 Following Security Researcher, APT Hunter Let the fun begin! My tweets and opinions are my own
Alon Zahavi @Alon_Z4
63 Followers 157 Following
Gabriel Sztejnworcel @sztejnworcel
45 Followers 82 Following Software Engineer. Security Researcher.
Gal Zror @waveburst
368 Followers 220 Following
Assaf Sion @assafsion
251 Followers 741 Following Passionate about security, politics and mostly nonsense. Tweets are my own.
EranShimony @EranShimony
701 Followers 129 Following Security researcher, malware analyst, low level lover and not too bad Starcraft 2 player My tweets and opinions are my own
Shay Nahari @Red_Sec_Shay
262 Followers 650 Following VP of Red-Team services @CyberArk,opinions are my own
Niv Levy 🇮🇱 @restr1ct3d
5K Followers 3K Following Penetration Testing Engineer / Offensive Security Certified Professional / Bug Bounty Hunter
HTido @hoorvitch
45 Followers 165 Following
Eviatar Gerzi @g3rzi
631 Followers 888 Following Security Researcher interested in reversing, malware analysis, CTFs, PrivEsc vulns, and DevOps security (docker and k8s) ;)
Lavi Lazarovitz @__Curi05ity__
308 Followers 338 Following Curious about #infoSec, #EnterpriseSec #CloudSec and #EverythingSec. Plays offense to master defense. Head of Research @CyberArk Labs.
Nimrod Stoler @n1mr0d5
62 Followers 49 Following
Asaf Hecht @Hechtov
670 Followers 312 Following A passionate Cyber Researcher who is also a former Helicopter Pilot :)Be sure to check out my recent blog about my latest research “Your NVMe had Been Syz’ed”. In there I show how to add new subsystems to syzkaller, and how to use it to find new vulnerabilities. cyberark.com/resources/thre…
In a world with increased web session hijacking, @CyberarkLabs Malware Analyst Ari Novick breaks down how your organization can minimize the risk of unauthorized access with CyberArk Secure Browser. spr.ly/6019ZCrMS #IdentitySecurity #SecureBrowser #cybersecurity
🍪 Hot off the press! 🍪 Let's talk about cookie-stealing malware and session hijacking You’ll also cover various infostealer families & their techniques. cyberark.com/resources/thre…
I need your help. I'm hosting an AMA style chat between myself, @Red_Sec_Shay and @BbMurphy on April 16th. I've got some great topics I want to cover, but I'd like to know what sorts of questions YOU want to ask. Shay is the VP of our Red Team Services, and Bryan runs the…
In a digital age rife with evolving cyber threats, @Andy_Thompson , Global Research Evangelist at @CyberArk , delves into cybersecurity challenges and strategies. #CyberSecurity #Deepfake #PolymorphicMalware #SocialEngineering #CyberArkLabs Read More: t.ly/fve0w
Finally got around to publishing this post on a 𝙘𝙧𝙞𝙩𝙞𝙘𝙖𝙡 𝙫𝙪𝙡𝙣𝙚𝙧𝙖𝙗𝙞𝙡𝙞𝙩𝙮 𝙞𝙣 𝙖 #𝗖𝗼𝘀𝗺𝗼𝘀𝗦𝗗𝗞 𝙘𝙝𝙖𝙞𝙣! Dive in if you're interested in the security of the #IBC protocol and the Cosmos in general 🪐✨ cyberark.com/resources/thre…
🔥Hot off the presses!🔥 @Andy_Thompson reviews the TTP's in the latest nation-state attack on Microsoft. cyberark.com/resources/all-…
CVE-2024-23897 (CVSS 9.8): Critical Jenkins Security Vulnerability, RCE Possible securityonline.info/cve-2024-23897…
#OPINIÓN🗣️| Andy Thompson, investigador de #ciberseguridad de @CyberarkLabs, afirma, ante el problema de #seguridad que afecta a millones de registros, que no basta con establecer #contraseñas seguras, necesitamos cambiar con frecuencia los #credenciales🔐 eu1.hubs.ly/H07fRJN0
I was quoted in a recent article by @ITPro. "It does not matter how complex your password is, it doesn't matter if you're using the latest and greatest MFA. Once you hack a cookie, you hijack the session and you bypass all that." itpro.com/software/googl…
Exciting news 🚀 I've joined the incredible team at 💙 @CyberArk as their Head of Experiential Marketing. Stepping into the 🔒 #cybersecurity space is a thrilling adventure. Honored to be part of a company shaping the future of identity security. #newjob #career #news
I was on the @PhillipWylie show!!! youtube.com/watch?v=LAfMMf…
When I was talking about the technology that came before generative AI, I was talking about Microsoft's Tay chatbot. Remember how that went? ☠️
We know that #GenAI is being used by innovative attackers to drive more effective #cyberattacks in greater volumes than ever before, but what part does it play in cyber defenses? @CyberarkLabs @Andy_Thompson adds his expert view to an @FT Special Report: spr.ly/6014rJAo0
@ChicagosMayor Aren’t you a sanctuary city? Talk the talk but not going to walk the walk?
In @wilfredchan's latest piece for @FastCompany, he interviews our very own @Andy_Thompson and discusses how #CyberSecurity lapses have put U.S. water utilities at risk. Read the full story here: fastcompany.com/91002831/us-wa…
Did you check out the latest Trust Issues podcast with @Andy_Thompson? He deconstructed the latest breaches and showed the far-reaching implications of our digitally interconnected ecosystem. Listen in today! spr.ly/6013Ry87h #IdentitySecurity #Breach #cybersecurity
Ransomware operators are leveraging legitimate software tools to infiltrate systems and compromise data. From abusing encryption tools to exfiltrating data using popular collaboration apps, attackers are becoming more sophisticated in their techniques. cyberark.com/resources/blog…
Unit 221B chief researcher Allison Nixon peels apart 'the Com', the online sub-culture that includes dangerous teenage hackers responsible for major corporate breaches @nixonnixoff #SecurityConversations Full episode: securityconversations.com/episode/alliso…
So I literally JUST got done recording a webinar where @KhizarSultan and I broke down the recent Okta breach...HAR's and all. I really hope you sign-up and check it out. Nov 16th. (It'll also be recorded and on-demand after) lp.cyberark.com/20231116-web-a…
Interesting reading on how to use Static Code Analysis tools for finding vulnerabilities (with a NULL Pointer Dereference in the NVMe driver of the Linux kernel as practical example) Credits @TalLossos (@TalLossos) cyberark.com/resources/all-… #Linux #kernel #infosec