Shay Nahari @Red_Sec_Shay
VP of Red-Team services @CyberArk,opinions are my own Joined June 2014-
Tweets69
-
Followers262
-
Following650
-
Likes64
[RELEASE] After a little wait, I'm happy to present SilentMoonwalk, a PoC implementation of a TRUE call stack spoofer, result of a joint research on an original technique developed by namazso, done with my friends @trickster012 and @waldoirc. Enjoy! ;) github.com/klezVirus/Sile…
I'm proud to release my first Google Chrome RCE derived from the most fascinating and mind bending exploit I have yet analyzed: CVE-2019-13720 Wizard Opium. This is a beautiful bug which I have crafted into an exploit bypassing ASLR, CFG and CET on Win10 github.com/forrest-orr/Wi…
Since releasing malmemdetect and providing a list of IOCs i feel more comfortable releasing this. github.com/waldo-irc/YouM… This is a project implementation of x64 gargoyle and sRDI to bypass PeSieve and Moneta in memory as threads. It’s stable, blog post after shmoo.
Already released way earlier but I'm sharing on Twitter too just because. Blog post + poc on detecting malware through return addresses. Recommend also looking at the following made by @thefLinkk github.com/thefLink/Hunt-… arashparsa.com/catching-a-mal…
Just released new blog Post on the CISA advisory regarding the Ukraine attack with @waldoirc @__Curi05ity__ cyberark.com/resources/blog…
CyberArk labs new research on abusing RDP virtual channels for lateral movement and priv esc.
CyberArk labs new research on abusing RDP virtual channels for lateral movement and priv esc.
My personalized Windows 10 re-creation of the HYDSEVEN exploit chain used to target Coinbase. This chain involves the use of a Firefox RCE (CVE-2019-11707) and Firefox sandbox escape (CVE-2019-11708) for shellcode execution as Medium Integrity github.com/forrest-orr/Ex…
Full moneta bypass with 0FPs! A few more tweaks and I’m hoping peseive is next! @_ForrestOrr
#Windows Hello face recognition can be bypassed using a USB device spoofing the camera and injecting images @OmerTsarfati @CyberarkLabs Labs demonstrated why USB cameras and other biometric devices shouldn't be treated as a simple (untrusted) USB device bit.ly/2VsVh07
Blocking access to AWS metadata by two rules: iptables --append -I DOCKER-USER OUTPUT --proto tcp --destination 169.254.169.254 --match owner --uid-owner root --jump REJECT iptables -I FORWARD -i docker0 -d 169.254.169.254 -p tcp -m multiport --dports 80,443 -j DROP
New blog post : Red-Team view on attacking MFA :cyberark.com/resources/thre… @CYBRImpact
Since we're sharing I also created a sploit for cve-2021-21551! I actually used @Void_Sec's post here: voidsec.com/exploiting-sys… and then comboed it with @_ForrestOrr's Spool RPC mechanism here: github.com/forrest-orr/Do… to provide an interactive system shell using the SeImperonsate
Today I completed the world's first re-creation of the Darkhotel APT "Double Star" exploit chain, including many enhancements and personalizations. From Firefox RCE, to sandbox escape, to EoP to SYSTEM utilizing CVE-2020-0674 and CVE-2019-17026 github.com/forrest-orr/Do…
I am feeling excited 😀 to release a new tool: Kubesploit A post-exploitation HTTP/2 Command & Control framework, focused on containerized environments. It was built on top of #Merlin, a great project by @Ne0nd0g. github.com/cyberark/kubes… #kubesploit #kubernetes #redteam
CyberArk Red-Team new blog is up: A Modern exploration of windows memory corruption exploits , part I cyberark.com/resources/thre… @_ForrestOrr @CyberArk
Happy to release my very first blog post @CyberArk! Wrote about how I used @code_ql to find (some) vulnerable calls to memcpy + GitHub link with the query I wrote. @Semmle @GHSecurityLab cyberark.com/resources/thre… @CyberArk.
Check out my new blog post about attacking #Kubernetes cluster with a new open-source kubelet client (#kubeletctl) I wrote 😃 Link to the post: cyberark.com/resources/thre… Link to the tool: github.com/cyberark/kubel… Enjoy 😃 #kubelet #client #pentest #redteam #DevSecOps #DevOps

⛈️ rainmaker ⛈�.. @Andy_Thompson
3K Followers 1K Following Master of Ceremonies of the @Dallas_Hackers | @CyberArkLabs Hypeman
Asaf Hecht @Hechtov
670 Followers 312 Following A passionate Cyber Researcher who is also a former Helicopter Pilot :)
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Dirk-jan @_dirkjan
25K Followers 173 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
CyberArk Labs @CyberarkLabs
1K Followers 24 Following The official Twitter account for @CyberArk Labs news and updates from our threat research team. #CyberSecurity
Alma Schanding @AlSchandi
47 Followers 5K Following
TF Aficionado of Texa.. @TF_Aficionado
776 Followers 211 Following Family Man, Transformers Enthusiast, Photographer, Software Engineer. I had more toys besides Transformers, but my wife told me to pick one. Hold My beer!!
Anthony. @AnthonySecurity
2K Followers 2K Following Director, Red Team @ Praetorian. Alumni Mandiant, MWR, NCC
Ray [REDACTED] @RayRedacted
56K Followers 6K Following •He/him • Assoc Producer Emeritus: @DarknetDiaries Cybersecurity Researcher •
Brady Bloxham @bradybloxham
3K Followers 251 Following
SecByT̷͔̼̯̖͑̽�.. @techbytom
1K Followers 2K Following Privacy, motorcycle, and craft beer geek. Adversarial thinker. Blue team your blue team for better red teaming.
st4rl0rd @luwhick
241 Followers 3K Following
Michael Novinson @MichaelNovinson
3K Followers 2K Following I cover the vendor and technology landscape for @ISMG_News including M&A, startups and key trends, with a focus on what’s relevant for CISOs. [email protected]
Zachary Gorby @TheGing3rm4n
91 Followers 529 Following Sr DFIR Engineer | Cybersec Consultant | SANS alumni | Gamer | Guitarist | 3D Printing Nerd
Yaniv L @YanivLo
50 Followers 522 Following
suryavamshi @suryavamshi2
8 Followers 201 Following
secmon @secmon2016
161 Followers 2K Following
Sagi Dinar @DinarSagi
7 Followers 246 Following
Trung Nguyen Minh @TonyNguyenDH
0 Followers 2K Following
ndv hlmn @ndv_hlmn
2 Followers 45 Following
__ @bisexy_me
35 Followers 739 Following
TobiTheOnlyKingCharle.. @TheKingCharles_
2 Followers 44 Following
Gal Zror @waveburst
368 Followers 220 Following
Alon Ben Tsur @iamgweej
155 Followers 235 Following
Lidor @Lidor84749835
57 Followers 524 Following
Andrew @4ndr3w6S
2K Followers 2K Following Senior Manager of Detection Engineering @HuntressLabs | Prev. Practice Lead, TAC (Purple Team) @TrustedSec | @SpursOfficial Super Fan - COYS!
David Lang @_david_lang
68 Followers 715 Following
Ron Kagansky @RonKagansky
24 Followers 439 Following
Michael @m33ch33
104 Followers 422 Following WhiteHat hacker, Application Security Expert, Security Researcher, Pen Tester and Principal Consultant @ https://t.co/bAvL43kMCY
Rafi Schwarz @rafischwarz3
84 Followers 511 Following Principal Software Architect @CyberArk. Enthusiastic about technology, software development, DevOps, security, basketball and tennis.
Pedro @Pedro16221254
4 Followers 254 Following
Abhishek Pardeshi @Abhishe77810054
1 Followers 158 Following Learning everyday. Keen on Cybersecurity. Aspiring to be a CISO.
Jeff Vealey @jeffvealey
69 Followers 417 Following Baseball fan and still playing with the Wake Blue Sox in the RDU area. Living the good life and fighting the good fight!
Fortra @fortraofficial
2K Followers 1K Following At Fortra, we’re creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions.
Robert Drannikov @RobertDrannikov
13 Followers 315 Following
Nick VanGilder @nickvangilder
2K Followers 2K Following Red Team Lead @RegionsBank | He/Him | Combat Veteran | Hacker
starturn @starturn2
47 Followers 1K Following
bhaskar @rastogi_bhaskar
43 Followers 2K Following
Jai @Jai_Z0R0
24 Followers 598 Following
Mike Iacovacci @mikeiacovacci
281 Followers 173 Following Senior ██████ Engineer // Digital Forensics :: Incident Response :: Threat Hunting // Advocate for rational egoism and individual liberty. My views only.
Jd52 @sec_farm
0 Followers 121 Following
Tomer Zait @realgam3
1K Followers 297 Following Head Of Security Research at @F5 | Writer at DigitalWhisper | CTF Manager at @BSidesTLV_CTF
Mike Perrin @MikePerrin78
13 Followers 134 Following
Oliver Lyak @ly4k_
8K Followers 267 Following Yet another security researcher 🔦 Github: https://t.co/7WFOFz17KI
vx-underground @vxunderground
291K Followers 211 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
⛈️ rainmaker ⛈�.. @Andy_Thompson
3K Followers 1K Following Master of Ceremonies of the @Dallas_Hackers | @CyberArkLabs Hypeman
sn🥶vvcr💥sh @snovvcrash
10K Followers 439 Following Sr. Penetration Tester / Red Team Operator @ptswarm :: Author of Pentester’s Promiscuous Notebook (https://t.co/rL1sv5A2R7) :: He/him :: Tweets’re my pwn 🐣
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
an0n @an0n_r0
11K Followers 716 Following CRT(E|O|L) | OSCP | @RingZer0_CTF 1st (for 2yrs) | HackTheBox Top10 | RPISEC MBE | Flare-On completer | GoogleCTF writeup winner | SSD research | Math MSc |🇭🇺
mgeeky | Mariusz Bana.. @mariuszbit
11K Followers 611 Following 🔴 Red Team operator, ex-MWR/F-Secure pentester, ex-AV engine developer @ESET, green tea addict. 🫖 @[email protected]
Mike Felch (Stay Read.. @ustayready
15K Followers 2K Following Pentester / Red Team | Hacking since Renegade BBS backdoors | Dev since vb3 | Content since '99-'03 ezines | Prior CrowdStrike / BHIS | In Christ's grip
ap @decoder_it
7K Followers 258 Following Incident Response and Security Consultant @semperistech . Independent Security Researcher. Cyclist & Scubadiver. MSRC MVR 2022.
Jean @Jean_Maes_1994
11K Followers 1K Following Director of Advanced Assessments -EU @neuvik | @sansoffensive Certified instructor/SEC565 author/SEC699 co author https://t.co/haRI3ruvlg
Shak Reiner 🍍 @ShakReiner
394 Followers 730 Following Principal Security Researcher @CyberArk Labs. Tell your dog I said gm.
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
James Forshaw @tiraniddo
48K Followers 364 Following Security researcher in Google Project Zero. Author of Attacking Network Protocols. Tweets are my own etc. Mastodon: @[email protected]
Charlie Bromberg « .. @_nwodtuhs
13K Followers 648 Following Trying to hack the way we hack things 🏴☠️
Asaf Hecht @Hechtov
670 Followers 312 Following A passionate Cyber Researcher who is also a former Helicopter Pilot :)
Nick Carr @ItsReallyNick
38K Followers 4K Following Lead, Cyber Crime Intelligence @Microsoft ☠🏛️ Former Incident Response + Threat Research @Mandiant 🦅 Former Chief Technical Analyst @CISAgov 🛡️
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
strandjs - strandjs@b.. @strandjs
45K Followers 2K Following I will light the way by the bridges I burn. Retired Senior SANS Instructor IANS Faculty Black Hills Information Security Active Countermeasures
Marcello @byt3bl33d3r
29K Followers 532 Following CyBeRsEcUrItY | Not afraid to put down with some THICC malware on disk | securing and breaking AI @ProtectAICorp | Ex @spacex
SandboxEscaper @big_polar_bear1
2K Followers 281 Following Fan of quadratic residues Former microsoft employee selling windows 0days.
Dlive @D1iv3
2K Followers 1K Following Security Researcher. 2022 MSRC MVR. Windows Active Directory Security / Cloud Security / Web Security. Tweets are my own.
winterknife 🌻 @_winterknife_
4K Followers 5K Following low-level developer with a focus on 𝙸𝚗𝚝𝚎𝚕 𝚡𝟾𝟼 ISA devices running 𝚆𝚒𝚗𝚍𝚘𝚠𝚜 | R&D @BHinfoSecurity | https://t.co/lyJL0y7qRZ
Andrew @4ndr3w6S
2K Followers 2K Following Senior Manager of Detection Engineering @HuntressLabs | Prev. Practice Lead, TAC (Purple Team) @TrustedSec | @SpursOfficial Super Fan - COYS!
Anthony. @AnthonySecurity
2K Followers 2K Following Director, Red Team @ Praetorian. Alumni Mandiant, MWR, NCC
Eric Zhang @ekzhang1
9K Followers 335 Following I think about systems and interaction design. Currently working at Modal. recently: reading group, furniture, photos, biking, dataviz, wandering the city
CharlesLYost @CharlesLYost
397 Followers 731 Following
Gabriel Landau @GabrielLandau
3K Followers 701 Following WinDbg’er @ Elastic Security. Thoughts are my own. Some of my writing: https://t.co/EMJxj12lut More: https://t.co/pxG2OnO1OC @[email protected]
Ray [REDACTED] @RayRedacted
56K Followers 6K Following •He/him • Assoc Producer Emeritus: @DarknetDiaries Cybersecurity Researcher •
LaurieWired @lauriewired
30K Followers 205 Following Reverse engineer specializing in cross-platform malware analysis with a focus on mobile threats.
Benjamin Caudill @rhinobenjamin
1K Followers 853 Following Hacker. Builder. Founder of @RhinoSecurity
klez @KlezVirus
6K Followers 668 Following Principal Cyber Security Consultant at Digital Trust Consulting Services, BSI - Opinions are my own
Raviv Drucker @RavivDrucker
407K Followers 536 Following מגיש תוכנית התחקירים המקור, פרשן פוליטי, ערוץ 13
OpenAI @OpenAI
3.4M Followers 0 Following OpenAI’s mission is to ensure that artificial general intelligence benefits all of humanity. We’re hiring: https://t.co/dJGr6LgzPA
Ryan Ries @JosephRyanRies
5K Followers 284 Following Windows Escalation Engineer @ MSFT. I have retired from Twitter.
V2 @ZeroMemoryEx
1K Followers 449 Following Cyber Security Consultant | Malware Developer during train rides
Ɛinav Sitton @Misty_Hunt
2K Followers 561 Following “You have no control who lives who dies who tells your story “
RET2Pwn @RET2_pwn
2K Followers 464 Following #24 y/o | Binary Exploitation Player | Wannabe Malware Developer & Researcher
Brian Roemmele @BrianRoemmele
270K Followers 31K Following we can only see what we think is possible...
Arris Huijgen @bitsadmin
2K Followers 99 Following Windows Offensive Security Enthusiast 🤠 Blog: https://t.co/CAwdjs2rKS GitHub: https://t.co/YG2YOxfosm
I am d3d (dead, мё�.. @deadvolvo
2K Followers 152 Following Security Researcher - Founder of Malicious Group Research - Synack Red Team Operator - DoD researcher of the year 2022 - Top 10 web attacks in 2023 - CRTO
GuillaumeBen @tux_be
78 Followers 135 Following Security analyst, Threat Hunter, Crossfitter, Chess enthusiast. Opinions are mine.
פידטק וידוי.. @FeedTechILUncen
15K Followers 18 Following מחשבות ווידויים ללא צנזורה! הוידויים המועלים נשלחים אנונימית אינם מייצגים את דעתנו ואיננו אחראים להם. (e/acc) הקליקו כאן להתוודות אנונימית 👈 https://t.co/hYu8dLUDnP
FalconFeeds.io @FalconFeedsio
29K Followers 518 Following Democratizing Cyber Security. Threat intelligence platform for Cyber Security professionals and Small/medium business. Insights from Darkweb and Threat Actors.
Maximilian Hils @maximilianhils
4K Followers 422 Following @mitmproxy developer, making cloud more secure at @google. TLS, web, networks, and open source. @[email protected]
HackTricks @hacktricks_live
12K Followers 198 Following HackTricks is a project which aims to offer free quality hacking resources to all the world, so people can learn for free the latest techniques in cybersecurity
Chick3nman 🐔 @Chick3nman512
3K Followers 2K Following Sam Croley, Austin based password cracker & researcher; Team @hashcat Core Dev; Principal Threat Emulation & Offensive Security; DMs always open
Jordan Borean @BoreanJordan
782 Followers 42 Following
Grzegorz Tworek @0gtweet
29K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Rémi Escourrou @remiescourrou
1K Followers 442 Following Information security enthusiast, I work as penetration tester & I am passionate about windows security and active directory
CodeX @codex_tf2
1K Followers 204 Following advanced persistent clown 🤡 📕 redteam blog: https://t.co/ihAv2kG3JR 🛠️ github: https://t.co/VhmOUAWcTp
Freddy Ouzan @falsneg
849 Followers 815 Following i like butter croissants and security controls, uncontrollably eating both.
Octoberfest7 @Octoberfest73
4K Followers 150 Following Red Team | Offensive Tool Dev | Malware Dev | OSCP | OSEP | RTJC
Mika B. @Mika_book
2K Followers 413 Following All I have is my honor, a tolerance for pain, a couple of college credits and my top-notch brain
treasureteen- נער .. @treasureteen
3K Followers 213 Following עמוד הטוויטר של הבלוג "נער אוצר"- על כלכלה, חברה, מדיניות ומה שביניהן.Hi #infosec, I noticed a group of my followers support HAMAS and their acts, commenting with smiles and laughter about babies being murdered in-front of their mothers. (Please bare with me) Started blocking them, but how many are there in our global community? I’M CALLING 🔈…
@khamenei_ir תקשיב כבשל'ה, זה ציוץ חצי כוח. התחביר שגוי, אין פאנץ' וכל הסיפור נראה מאוד לא מאיים. התאכזבתי.
Have Docker? Run BloodHound CE with one command: curl -L github.com/SpecterOps/Blo… | docker compose -f - up
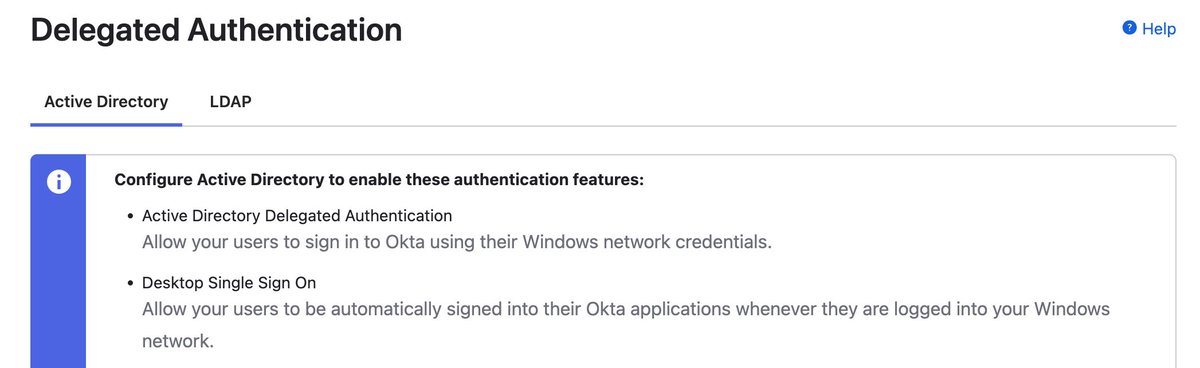
If you're on an engagement, keep an eye out for the SPN HTTP/<company>.kerberos.okta.com. It provides delegated auth to Okta for a compromised AD user (and usually doesn't require MFA when proxied). getST.py -spn HTTP/company.kerberos.okta.com.
I'm really excited to share my talk from @defcon - Hacking ISPs with PPPoE youtube.com/watch?v=Uwwg4g… #DEFCON #DEFCON30
An update 🎉🎉 for silentrobots.com/burpsuite-proj…. This should make it easer to parse a Burp Suite project file for portions of requests or responses. For example, only return the [response.body] and [url] from all traffic in proxyHistory.
Here is my variant of Gargoyle for x64 to evade memory scanners. Fully relies on ROP and PIC without any APC. Huge thanks to @waldoirc for the documentation. github.com/thefLink/DeepS…
"Reject binary thinking" < Said exactly 01 people, ever.
I'm proud to release my first Google Chrome RCE derived from the most fascinating and mind bending exploit I have yet analyzed: CVE-2019-13720 Wizard Opium. This is a beautiful bug which I have crafted into an exploit bypassing ASLR, CFG and CET on Win10 github.com/forrest-orr/Wi…
Since releasing malmemdetect and providing a list of IOCs i feel more comfortable releasing this. github.com/waldo-irc/YouM… This is a project implementation of x64 gargoyle and sRDI to bypass PeSieve and Moneta in memory as threads. It’s stable, blog post after shmoo.
Already released way earlier but I'm sharing on Twitter too just because. Blog post + poc on detecting malware through return addresses. Recommend also looking at the following made by @thefLinkk github.com/thefLink/Hunt-… arashparsa.com/catching-a-mal…
My personalized Windows 10 re-creation of the HYDSEVEN exploit chain used to target Coinbase. This chain involves the use of a Firefox RCE (CVE-2019-11707) and Firefox sandbox escape (CVE-2019-11708) for shellcode execution as Medium Integrity github.com/forrest-orr/Ex…
Full moneta bypass with 0FPs! A few more tweaks and I’m hoping peseive is next! @_ForrestOrr
I made a post about research I did recently for fun on learning how to encrypt the Cobalt Strike heap. arashparsa.com/hook-heaps-and… Learned a lot of interesting things along the way and I'd like take it further. Special Thanks to: @_ForrestOrr @ilove2pwn_ and @MrUn1k0d3r for the help
Blocking access to AWS metadata by two rules: iptables --append -I DOCKER-USER OUTPUT --proto tcp --destination 169.254.169.254 --match owner --uid-owner root --jump REJECT iptables -I FORWARD -i docker0 -d 169.254.169.254 -p tcp -m multiport --dports 80,443 -j DROP