laginimaineb @laginimaineb
Tweets are my own (who else would write them?). bits-please.blogspot.com Joined August 2015-
Tweets608
-
Followers5K
-
Following51
-
Likes600
Haha, I fucked up the link for the previous tweet. Here you all are: gist.github.com/SciresM/d31aa8…
Exploring and Breaking Samsung’s TrustZone: a blog series Parts I-II-III medium.com/taszksec/unbox…
Slides for my talk on Weird Machines and provable non-exploitability today in Oxford (more accessible than the paper): docs.google.com/presentation/d…
Exploiting Qualcomm EDL Programmers: Memory & Storage based attacks allowing PBL extraction, rooting, secure boot bypassing & bootloader chain debugging/tracing. Multiple Qualcomm based mobile devices affected (5-part blog post) alephsecurity.com/2018/01/22/qua…
jamais vu - a 1.0.0 TrustZone code execution exploit for the Nintendo Switch: reddit.com/r/SwitchHacks/…
Catch a live demo of a chosen-plaintext attack, exploiting a logical vulnerability in one of Windows' more common protocols, that enables remote code execution. #BHASIA Briefing by @RomanBlachman ow.ly/y0IC30hTOu7
The technical details of a working remote exploit for pixel, security.googleblog.com/2018/01/androi…, Thanks for the generous of Google, it's a Pleasant cooperation with android security team,
First of a few remote code execution flaws in various popular torrent clients, here is a DNS rebinding vulnerability Transmission, resulting in arbitrary remote code execution. github.com/transmission/t…
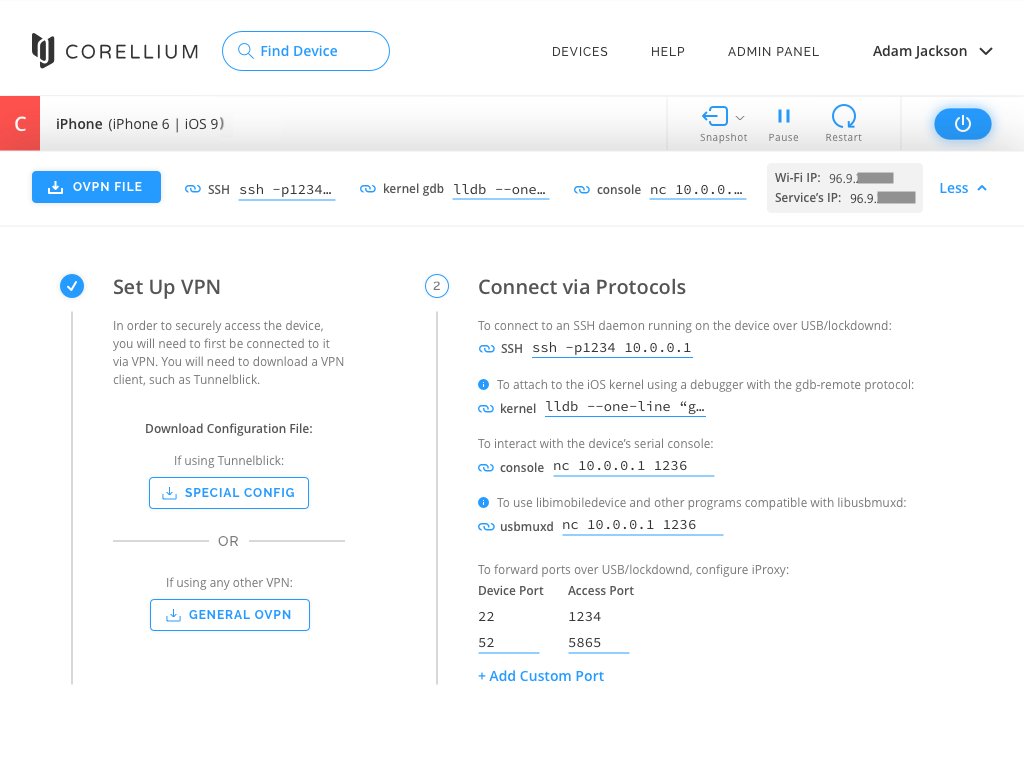
Ready to be CHARMed? Our Corellium Hypervisor for ARM enables us to run virtual iPhones in the cloud with game-changing features like: - Run any version of iOS - On demand thread list & kernel backtrace - Optional jailbreak for any version - Web-based debugging - And much more!
Another fun Android privesc, allowing arbitrary service replacement (without racing) x.com/projectzerobug…
Another fun Android privesc, allowing arbitrary service replacement (without racing) x.com/projectzerobug…
This video shows a #Meltdown attack on *uncached* data. The data is not in L1, not in L2, and not in L3 cache. That's what clflush does, it throws the data out of all caches. #Meltdown exploits a race condition and even for uncached data this race can be won. x.com/misc0110/statu…
This video shows a #Meltdown attack on *uncached* data. The data is not in L1, not in L2, and not in L3 cache. That's what clflush does, it throws the data out of all caches. #Meltdown exploits a race condition and even for uncached data this race can be won. x.com/misc0110/statu…
Releasing our PoC implementations for #Meltdown - github.com/iaik/meltdown - More to follow /cc @misc0110 @lavados @StefanMangard #intelbug #kaiser #kpti
The PoC code referenced in our recent blogpost about CPUs is public now: bugs.chromium.org/p/project-zero…
@laginimaineb The ARM whitepaper says "It is believed that there are no implementations of Arm processors which are susceptible to this mechanism that also implement the Pointer Authentication Mechanism introduced as part of Armv8.3-A, where there are keys held in system registers."
Are there any ARM v8.3 CPUs that are susceptible to variant 3a? In theory, on those CPUs the pointer authentication keys can be read, right?
Exploit source that accompanies the Project Zero WPAD blog post (googleprojectzero.blogspot.ch/2017/12/apacol…) was just released in bugs.chromium.org/p/project-zero…. Please enjoy responsibly!
Another ashmem bug allowing inter-process munmaps (should also work from isolated_app) x.com/projectzerobug…
Another ashmem bug allowing inter-process munmaps (should also work from isolated_app) x.com/projectzerobug…
My new vuln CVE-2018-0743 in WSL was patched today && it's tweetable! int main(void) { int n = 0xaaaaaaa; void **p = calloc(n, 8); for (; n; --n) p[n-1] = ""; execv("", p); } Full exploit at @BlueHatIL portal.msrc.microsoft.com/en-us/security…
Project Zero blog post: "Reading privileged memory with a side-channel" by Jann Horn (@tehjh) - googleprojectzero.blogspot.com/2018/01/readin…

Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
Brendan Dolan-Gavitt @moyix
25K Followers 6K Following Associate Professor @ NYU Tandon. Security, RE, ML. PGP https://t.co/3WXr0RfRkv Founder of the MESS Lab: https://t.co/zGycrX3Gmn "an orc smiling into the camera" — CLIP
mdowd @mdowd
32K Followers 744 Following Internet Hacker. Founder of @vigilant_labs. Previously, co-founder of Azimuth Security (now L3Harris Trenchant)
Saar Amar @AmarSaar
18K Followers 362 Following Reversing, exploits, {Windows, Hyper-V, *OS} internals, mitigations. Apple SEAR. Opinions are my own. @[email protected]
Matthew Green @matthew_d_green
143K Followers 1K Following I teach cryptography at Johns Hopkins. Mastodon at [email protected] and BlueSky at https://t.co/GI4QlxYTdk.
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
Ptrace Security GmbH @ptracesecurity
53K Followers 883 Following Empowering IT Security Professionals through Hands-On Online Courses.
Ivan Fratric 💙💛 @ifsecure
17K Followers 192 Following Security researcher at Google Project Zero. Tweets are my own. Backup @[email protected]
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
Ian Beer @i41nbeer
49K Followers 144 Following
nedwill @NedWilliamson
16K Followers 499 Following Project Zero Researcher Discovered SockPuppet, Soundhax https://t.co/16vegpfPXc
David Weston (DWIZZZL.. @dwizzzleMSFT
25K Followers 1K Following Vice President, OS Security and Enterprise @Microsoft || @CISAgov Technical Advisory Committee
Travis Goodspeed @travisgoodspeed
25K Followers 4K Following Merchant of Dead Trees and Licensed Proselytizer of the Gospel of the Weird Machines with Pwnage, PoC, and Secular Rock.
Alex Plaskett @alexjplaskett
9K Followers 590 Following Security Researcher | Pwn2Own 2018, 2021, 2022, 2024 | Tweets about 0day, OS, mobile and embedded security.
dragosr @dragosr
25K Followers 10K Following Stop, Think, Pwn! (see also @[email protected] for alternate)
Andrey Konovalov @andreyknvl
6K Followers 666 Following Security engineer at https://t.co/027VXUlgOx. Focusing on the Linux kernel. Maintaining @linkersec. Trainings at https://t.co/D5MrxmYimS.
Tavis Ormandy @taviso
127K Followers 645 Following Vulnerability researcher at Google. This is a personal stream, opinions expressed are mine. I'm also @[email protected]
Axel Souchet @0vercl0k
13K Followers 509 Following ¯\_(ツ)_/¯, blogging on https://t.co/36oOc8Mgha and posting codes on https://t.co/P83Oen94Rc.
Gareth Heyes \u2028 @garethheyes
32K Followers 1K Following JavaScript for hackers: Learn to think like a hacker. https://t.co/e0aNEbEDk5
Ayush Goyal @sl4y3r__07
36 Followers 134 Following Undergrad at IIT Roorkee, 2nd Year | Interested in learning CS concepts, Windows Internals, low-level stuffs | CTFs
someone @someone56293152
0 Followers 73 Following
Sparta_EN @sparta_en
29 Followers 526 Following I write spaghetti code. Stray cat. Experienced troublemaker. | 会鲨三无账号 | ヰ組 | spartaen(at)infosec(dot)exchange
Nir / ニル @NirDafnai
67 Followers 584 Following
Philip Åkesson @PhilipAkesson
154 Followers 701 Following Security and embedded systems. @[email protected]
qcqs @fpqcqs
0 Followers 64 Following
Sam @iosamamostafa
0 Followers 315 Following
SAFE(AnWang) @safeanwang
16K Followers 130 Following Next generation of SAFE blockchain network, aiming at large-scale, secure payment and privacy computation.
pidifn voidgh @pidifn
23 Followers 131 Following
Francesco Crecchi @FrancescoCrecch
85 Followers 237 Following Adversarial Machine Learning Researcher, University of Pisa
aswzs gsx @AswzsG
6 Followers 74 Following
Steve @st9eve
38 Followers 230 Following
Santos M Jom @SantosMJom1
347 Followers 3K Following I’m a music star hit me up for any show or business
Raj R @Ne0nR3d
105 Followers 2K Following I’m a security researcher who loves exploring virtual machine and containers. I have a passion for hacking KVM and other Hypervisors, containers, kubernetes.
Brightiup @realBrightiup
7K Followers 544 Following
CJ @CanJmp
111 Followers 2K Following
M @3mptyb0x
0 Followers 169 Following Passionate about CyberSecurity, both Red and Blue team. I'm the sheep inside the box
Martijn Bogaard @jmartijnb
951 Followers 1K Following Reverse engineers source code by day and reviews binaries by night. TEEs, TAs, bootloaders (Secure Boot), RTOSs, firmware blobs and other low-level sw.
tlk @tlk___
810 Followers 1K Following
Anton Dewitz @AntonDewitz
100 Followers 919 Following
emodend @LeHidend
18 Followers 103 Following
yair zak @zak_yair
5 Followers 185 Following
katietheSecurityrecru.. @katieboynton070
16 Followers 94 Following Cyber Security Recruiter - mostly high level IC + leadership roles covering App Sec, Risk Assessment, Sec Eng, Sec Arch WiCyS member. Neurodivergent. Human. 🌿
Tang Wang @TangWan59998005
0 Followers 1 Following
今晚打老虎 @terminator_850
0 Followers 32 Following
𝓐𝓫𝓾 𝓝𝓪.. @ikrem2022
7 Followers 176 Following مبرمج Paython وأعمل بنظام Debian كمنصة رئيسية خبرتي تمتد لمجال iOS و Jailbreak قمة سعادتي في العطاء المعرفي ومساعدة الأخرين
D4rkD0g @D0gD4rk
1 Followers 37 Following
RF_ReadOnly @ReadonlyRf
30 Followers 548 Following
Tiesun 👨💻�.. @TIE__SUN
389 Followers 2K Following A guy who lives with the moments🍁. TI-Analyst | AS-Warrior
zaza @musccleman
35 Followers 422 Following
Freeze @Freeze97
9 Followers 199 Following
Tony Meehan @snowboardvstree
1K Followers 4K Following Co-Founder/CTO @ Stealth. Former @Elastic, @EndgameInc, and NSA/TAO.
Alessio Ravera @alerave96
161 Followers 540 Following
Matthew Green @matthew_d_green
143K Followers 1K Following I teach cryptography at Johns Hopkins. Mastodon at [email protected] and BlueSky at https://t.co/GI4QlxYTdk.
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
Ian Beer @i41nbeer
49K Followers 144 Following
Filippo Valsorda @fil.. @FiloSottile
49K Followers 508 Following Cryptogopher / Go crypto maintainer / @kateconger-knower / RC F'13, F2'17 / #BlackLivesMatter / he+him https://t.co/ZE4RtJ1xqD / https://t.co/qfth7zr00W / https://t.co/j1grpEm8uR
Jeff Vander Stoep @jeffvanderstoep
3K Followers 228 Following Android security @google [email protected]
Tavis Ormandy @taviso
127K Followers 645 Following Vulnerability researcher at Google. This is a personal stream, opinions expressed are mine. I'm also @[email protected]
James Forshaw @tiraniddo
48K Followers 364 Following Security researcher in Google Project Zero. Author of Attacking Network Protocols. Tweets are my own etc. Mastodon: @[email protected]
Simon Willison @simonw
71K Followers 5K Following Creator @datasetteproj, co-creator Django. PSF board. @nichemuseums. Hangs out with @natbat + @cleopaws. He/Him. Mastodon: https://t.co/t0MrmnJW0K
Andrej Karpathy @karpathy
980K Followers 905 Following 🧑🍳. Previously Director of AI @ Tesla, founding team @ OpenAI, CS231n/PhD @ Stanford. I like to train large deep neural nets 🧠🤖💥
Grant Sanderson @3blue1brown
365K Followers 362 Following Pi creature caretaker. Contact/faq: https://t.co/brZwdQfdif
Georgi Gerganov @ggerganov
38K Followers 243 Following Not AI | 0x0e59 0x2550 24th at the Electrica puzzle challenge
René Mayrhofer 🇺�.. @rene_mobile
2K Followers 291 Following Prof. for networks and security @jkulinz/@insjku & Android platform security @Google Statements are only my own.
Jacques Fortier @jacquesgt
2K Followers 148 Following Firmware, operating systems, and security at billion device scale, but mostly pictures of my cat. @[email protected]
Alex Hude @getorix
4K Followers 142 Following Security Researcher ❖ Hardware Hacker ❖ Quality tools writer ❖ iOS/Android/IoT EM @ Corellium
LaForge - @LaF0rge@ch.. @LaF0rge
7K Followers 1K Following #Osmocom founder. Mobile Communications expert, former Linux Kernel Hacker, Freedom Fighter. Nerd. Mensch mit Kommandozeilehintergrund. #retronetworking
Junghoon Lee @lokihardt
2K Followers 0 Following
Chris Evans @scarybeasts
26K Followers 199 Following CISO and Chief Hacking Officer at HackerOne. Past: Founded {vsftpd, Chrome security, Google Project Zero}; Tesla; Dropbox. Hacker / Researcher. beebjit.
Zuk @ihackbanme
17K Followers 1K Following Mobile & Security Research | Founder @ZecOps (Acq. by JAMF) 🐊 & @ZIMPERIUM (Acq.) | #FreeTheSandbox✌ | ❤️ Chess | My random thoughts, only some are accurate.
JEB Decompiler @jebdec
2K Followers 461 Following JEB Decompiler & PNF Software news. Tweets by Nicolas Falliere.
Bjoern Kerler @viperbjk
2K Followers 401 Following Analyst and Qc/MTK/Exynos/Unisoc/Kirin chipset pwner (aka RevSkills). Reverse Engineer/Coder/Maker. 3D Print and SDR enthusiast. New Technology.
@[email protected].. @dangoodin001
43K Followers 755 Following Please use this hell site as sparingly as possible. Elmo can't be allowed to succeed. Follow me on Mastodon @[email protected]
Mathew Solnik @msolnik
3K Followers 1K Following CEO @ OffCell Research / Head of Security Engineering @ WitnessAI
CopperheadOS @CopperheadOS
6K Followers 195 Following Secure Android. CopperheadOS by @Copperheadsec. Release, product and community information.
Dmytro Oleksiuk 💥 .. @d_olex
13K Followers 1K Following zero-fucks-given infosec research | contacts: https://t.co/AB3QnrPja0 | 🇺🇦 Ukraine needs your help to kill Ruϟϟian zombies: https://t.co/ihU9OLujfk
Jann Horn - jann@info.. @tehjh
17K Followers 235 Following occasional human borrow checker; works at Google Project Zero; personal account; mastodon: [email protected]
Solar Designer @solardiz
14K Followers 1K Following @Openwall founder, @oss_security maintainer, @lkrg_org co-author. RTs don't imply agreement with points of view.
Tim Strazzere @timstrazz
8K Followers 361 Following Mobile, Drone & (automated) Vehicle Security Researcher and Malware Analyst, Tweets are my own not my employers
Alex Gantman (@agains.. @againsthimself
2K Followers 351 Following Security defense. No wires. Disclaimers: Work at $QCOM. Opinions are mine.
samy kamkar @samykamkar
63K Followers 4K Following think bad, do good. | https://t.co/1k7O9o2Gos | cofounder @openpathsec
Daniel Komaromy @kutyacica
2K Followers 187 Following https://t.co/MRHK7xHqDv | There's no crying in baseband. Security researcher, !SpamAndHex CTF player, Pwn2Own winner, founder of @TaszkSecLabs
Marco Grassi @marcograss
13K Followers 1K Following Expert®️, Information Security @ NIO Pwn2Own Winner
Adam Langley @agl__
13K Followers 120 Following
Daniel J. Bernstein @hashbreaker
22K Followers 23 Following Designing cryptography (deployed now: X25519, Ed25519, ChaCha20, sntrup, Classic McEliece) to proactively reduce risks. Coined phrase "post-quantum" in 2003.
RPW: @[email protected].. @esizkur
8K Followers 932 Following
Yulong Zhang @ansonzyl
71 Followers 30 Following
Jon Oberheide @jonoberheide
15K Followers 247 Following Current: Board member & startup advisor. Past: Co-Founder & CTO at @duosec, PhD at @umich. Go Blue! 〽️
Collin Mulliner @collinrm
9K Followers 717 Following Engineer | Security Researcher | Recovering Academic | KD2WON | Currently: securing Autonomous Vehicles @cruise
André Moulu @andremoulu
3K Followers 2K Following Android security researcher and team leader at @Cellebrite, member of @ge0n0sis Obviously tweets are my own.
Joshua J. Drake @jduck
28K Followers 2K Following A funemployed researcher living in the intersection between security and embedded Rust.פייקים חדשים בעניין ראש הממשלה לשעבר אהוד ברק במסמכי אפשטיין. @guyzo וצוות #מהצד_השני, עושים סדר בין האמת לעיוותים. א-ה סביב 17:00 בכאן 11 ובכאן BOX
Some new work from the part of Google Brain that works on ml for healthcare: we have encouraging early signs that non-invasive retinal images contain subtle indicators of cardiovascular health that ml models can pick up on, that weren't previously even known to human doctors. x.com/googleresearch…
Learn how #deeplearning makes it possible to accurately assess cardiovascular risk factors using retinal images. --> goo.gl/z44vPS
Another ACG bypass, this time without needing to compromise the entire JIT process bugs.chromium.org/p/project-zero…
Haha, I fucked up the link for the previous tweet. Here you all are: gist.github.com/SciresM/d31aa8…
Did a short writeup on how to recover some Switch RSA public keys that are supposed to be unknowable hardware secrets :) - never thought I'd get to actually use this attack, haha: gist.github.com/SciresM/d31aa8…
Exploring and Breaking Samsung’s TrustZone: a blog series Parts I-II-III medium.com/taszksec/unbox…
Slides for my talk on Weird Machines and provable non-exploitability today in Oxford (more accessible than the paper): docs.google.com/presentation/d…
@taviso Coherent UI is probably a nice target as it is used by a lot of games. Not only is it based on an old WebKit fork, but also native bindings into the game... Found a XSS via steam name once. coherent-labs.com
Exploiting Qualcomm EDL Programmers: Memory & Storage based attacks allowing PBL extraction, rooting, secure boot bypassing & bootloader chain debugging/tracing. Multiple Qualcomm based mobile devices affected (5-part blog post) alephsecurity.com/2018/01/22/qua…
jamais vu - a 1.0.0 TrustZone code execution exploit for the Nintendo Switch: reddit.com/r/SwitchHacks/…
Catch a live demo of a chosen-plaintext attack, exploiting a logical vulnerability in one of Windows' more common protocols, that enables remote code execution. #BHASIA Briefing by @RomanBlachman ow.ly/y0IC30hTOu7
The technical details of a working remote exploit for pixel, security.googleblog.com/2018/01/androi…, Thanks for the generous of Google, it's a Pleasant cooperation with android security team,
Less ordinary vulns: OOM which is exploitable -> 🐞 bugzilla.mozilla.org/show_bug.cgi?i… 🐞 bugzilla.mozilla.org/show_bug.cgi?i… 🐞 bugzilla.mozilla.org/show_bug.cgi?i…
pretty cool attack by @taviso using DNS rebinding to achieve RCE against a torrent client: github.com/transmission/t…
First of a few remote code execution flaws in various popular torrent clients, here is a DNS rebinding vulnerability Transmission, resulting in arbitrary remote code execution. github.com/transmission/t…
If we don't come out with a hardware dongle for testing CPU security called the In-Spectre Gadget I don't even know what we're doing anymore.
@lavados Were you also able to mount the attack against data that resides in memory with UC caching type?
This video shows a #Meltdown attack on *uncached* data. The data is not in L1, not in L2, and not in L3 cache. That's what clflush does, it throws the data out of all caches. #Meltdown exploits a race condition and even for uncached data this race can be won. x.com/misc0110/statu…
@aionescu That can be optimized a lot, in this video I read uncached memory with our internal #Meltdown tools (not public): youtu.be/6ViS_YOvmpg (can't upload GIF to Twitter for some reason...)
Researchers found that anyone who controls a WhatsApp server (sophisticated hackers, a government coercing the company) can insert themselves into any group chat, undermining WhatsApp’s promises of end-to-end encryption wired.com/story/whatsapp…